Red Teaming: Top tools and gadgets for physical assessments
Understanding the strengths and weaknesses of physical security controls in critical infrastructures is a valuable part of cybersecurity. Because from this angle, adversaries can obtain confidential information about targeted assets. Imagine that you access the main door, enter the lift and take a photo of the building's floor plan. These techniques can provide you with a lot of information about critical locations to keep under the radar.
While many organizations have a strong awareness of emerging cyberattacks, their concerns are not as well observed regarding physical security. The risk associated with physical attacks is high because there is often no adequate protection against daily situations. For instance, imagine a simulation that includes bypassing the door locks, stealing devices, or even using social engineering strategies to get valuable information. This scenario could include convincing the employee to connect a USB device to their computer, take photos from long-range to capture sensitive information from an opened window, or even using the same uniform of the cleaning services to access the servers' room.
In this sense, there is a broad set of approaches and strategies to address this kind of attack. The benefits are apparent:
- Exposing weak physical barriers, such as gaps in fences, not monitored doors, and taking advantage of internet connection plug in the building.
- Understanding the risk, the damage of a well-succeded attack, which information could be impacted and exfiltrated, and so on.

What should you learn next?
Most popular tools and gadgets
This section will list some gadgets and tools associated often used by red teaming experts when executing physical security assessments.
Crazyradio: USB radio dongle based on the nRF24LU1+ from Nordic Semiconductor. 2.4GHz ISM band radio. For instance, you can control vulnerable mouse devices and introduce a new reverse-shell on the target. This hardware device is compatible with mousejack, keyjack, keysniffer and JackIt projects.
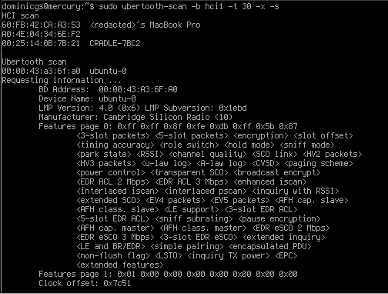
Ubertooth: This hardware is extremely useful for sniffing Bluetooth close ranges. With this device in place, executing experiments in Bluetooth packers is possible.

HackRF: HackRF, one from Great Scott Gadgets, is a software-defined radio peripheral capable of transmitting or receiving radio signals from 1 MHz to 6 GHz. Designed to enable the test and development of modern and next-generation radio technologies, HackRF One is an open-source hardware platform that can be used as a USB peripheral or programmed for stand-alone operation.
More details on the GitHub repository are here.
AirDrive Keylogger: The AirDrive Keylogger is an innovative ultra-small USB hardware keylogger that can be accessed with any Wi-Fi device such as a computer, laptop, tablet, or smartphone. It can record keystrokes from any keyboard, works as a Wi-Fi hotspot, and has a simple and straightforward HTTP interface to obtain the collected information.
USB rubber ducky: With this device, just plugging an innocent USB drive into a target computer can install backdoors, exfiltrate documents or simply capture credentials. With a few lines of code, anything is possible.
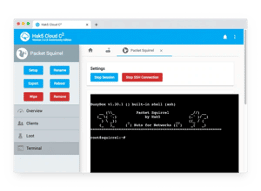
Packet squirrel: The man-in-the-middle device is very stealthy and capable of giving you covert remote access, painless packet captures, and performing secure VPN connections. The ability to gain persistent, remote access via VPNs and reverse shells is a straightforward process via the power of this device.

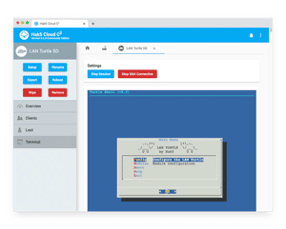
LAN turtle: The LAN Turtle is a covert Systems Administration and Penetration Testing tool providing stealth remote access, network intelligence gathering, and man-in-the-middle surveillance capabilities through a simple graphic shell. In short: "drop a LAN turtle, and you can get a shell."

WIFI PINEAPPLE: Automate Wi-Fi auditing and get actionable results from vulnerability assessment reports. This hardware allows airspace command with a new interactive recon dashboard and stays on-target and in-scope with the leading rogue access point suite for advanced man-in-the-middle attacks.
The importance of physical security
Although this is not an extensive list of tools and gadgets, we have presented some of the most notable gadgets that can be used in physical attacks against critical infrastructures. Maybe this can be the right moment to highlight this type of attack scenario on the agenda - a surface more exposed to attacks and a desirable vertex for opponents.
Become a Certified Ethical Hacker, guaranteed!
Get training from anywhere to earn your Certified Ethical Hacker (CEH) Certification — backed with an Exam Pass Guarantee.
Let's make physical security part of our cybersecurity strategy!
Sources:
- Red teaming list, GitHub
- Awesome Red Teaming, GitHub
- Physical Penetration Test, Red Team Secure
- Red Teaming tools, GitBook Segurança Informatica












