Investigating wireless attacks
In an earlier article, we discussed the fundamentals of wireless networks: the common types of wireless devices, terminology used, WLAN security types, 802.11 frame types and wireless traffic analysis using the aircrack-ng suite of tools.
In this article, we will discuss how that foundational knowledge can be used in analyzing wireless attacks. Let us begin by discussing various common wireless attacks that a network forensic investigator may come across during investigations and then let us analyze traffic captured during an attack.

Learn Secure Coding Fundamentals
Common wireless attacks
Successful network forensic investigations often rely on the understanding the investigator has around possible network attacks. This section discusses some of the most common attacks possible in wireless networks.
WEP/WPA2 cracking
Wireless encryption key cracking is a common attack in wireless networks. While many see it as an attack to gain unauthorized access to someone's internet, attackers can use the compromised keys to decrypt traffic captured over the network.
When wireless networks are configured to use WEP encryption, it is easy to obtain the key just by capturing enough traffic on the network. In the case of WPA/WPA2, four-way handshake is usually captured and used for offline cracking.
Sniffing
Sniffing using ARP spoofing is one of the most commonly seen attacks before SSL/TLS is embraced. Even after the introduction of SSL/TLS, sniffing was commonly seen combined with other techniques like stripping SSL off and then capturing traffic.
Even in today’s world there are open wireless networks commonly used in public places such as hotels and cafes. They use a captive portal for authentication and once the user is connected, the wireless traffic is not encrypted in many cases. In such cases, if users access sensitive data via clear text protocols such as HTTP (without SSL), wireless sniffing is still a danger. In addition to ARP spoofing, sniffing all the wireless traffic by putting the card in monitor mode is possible.
Rogue wireless access points
Rogue wireless access points are one of the most common security threats, and they are very easy to set up. While malicious actors can plant wireless access points to bypass firewalls, these rogue access points are often set up by employees for their own convenience without realizing the risk they bring to the organization.
Some companies deploy wireless intrusion detection systems to detect rogue access points, while some companies also perform war walking to detect malicious access points possibly set up by malicious actors.
Evil twin attacks
Rogue access points are usually set up with an SSID of the attacker's choice to lure the victim’s to connect to the network — providing free internet for instance. While evil twin attacks work the same way, an attacker sets up an access point with the same SSID as one that of the target organization.
When a client or station sees more than one SSID with the same name, the client will associate with the access point providing the strongest signal. Once a victim connects to a malicious SSID, an attacker can eavesdrop on all the traffic coming from the victim. Many organizations use wireless IDS software to detect such malicious SSIDs. This is usually done by looking for SSIDs with the same name but a different mac address.
Analyzing a wireless attack
In this section, let us go through packet analysis of a simple discovered attack. The assumption is that a victim has encountered a denial-of-service attack against the laptop. The laptop keeps disconnecting from the router even though all the other devices are working fine. This is reported and traffic capture was provided for further investigation.
The mac address of the victim is e6:23:0e:4b:2b:fd.
While analyzing the packet capture using Wireshark, it was observed that there are several packets of IEEE 802.11 Deauthentication type as shown below.
5236 16.355215625 Tp-LinkT_2a:b5:8c e6:23:0e:4b:2b:fd 802.11 39 Deauthentication, SN=1448, FN=0, Flags=........
Selecting one of the packets in Wireshark shows full details as shown below.
Frame 5236: 39 bytes on wire (312 bits), 39 bytes captured (312 bits) on interface wlan0mon, id 0
Radiotap Header v0, Length 13
802.11 radio information
IEEE 802.11 Deauthentication, Flags: ........
Type/Subtype: Deauthentication (0x000c)
Frame Control Field: 0xc000
.... ..00 = Version: 0
.... 00.. = Type: Management frame (0)
1100 .... = Subtype: 12
Flags: 0x00
.000 0001 0011 1010 = Duration: 314 microseconds
Receiver address: e6:23:0e:4b:2b:fd (e6:23:0e:4b:2b:fd)
Destination address: e6:23:0e:4b:2b:fd (e6:23:0e:4b:2b:fd)
Transmitter address: Tp-LinkT_2a:b5:8c (50:62:c1:2b:c5:8d)
Source address: Tp-LinkT_2a:b5:8c (50:62:c1:2b:c5:8d)
BSS Id: Tp-LinkT_2a:b5:8c (50:62:c1:2b:c5:8d)
.... .... .... 0000 = Fragment number: 0
0101 1010 1000 .... = Sequence number: 1448
IEEE 802.11 Wireless Management
It is clear that the router is sending the Deauthentication packets to the client device with the mac address e6:23:0e:4b:2b:fd. While one packet doesn’t give any indication of an attack, we can navigate to Wireless > WLAN Traffic in Wireshark to better understand the patterns.
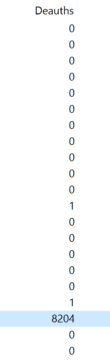
A quick look in this window shows the following.
Clearly, there is only one entry with a large number(8204) of Deauth requests. This is the entry with source as the router and destination as the victim’s device. This is clearly an abnormal number and indication of a denial-of-service attack.

Learn Threat Modeling
Conclusion
This article has shown an example of how we can analyze a simple denial-of-service attacks attempted on a client device. Wireless attack investigation often requires a good understanding of 802.11 frame types and structure at a minimum.
While we discussed a simple deauthentication attack, network forensic investigators may come across any other attacks that were discussed in the beginning of the article.
Sources
Network Forensics, Ric Messier
Internet Forensics: Using Digital Evidence to Solve Computer Crime, Robert Jones
Network Forensics: Tracking Hackers through Cyberspace, Sherri Davidoff