Incident Response and Computer Forensics
Introduction
With the number of devices connected to the Internet exploding in recent years, the incidences of security breaches have likewise become a hot and rather disturbing topic. Within this scope, it’s absolutely crucial for companies to know how to respond and deal with the consequences. All organizations should have an incident response plan that includes incident detection in addition to a response. We live in a disruptive digital era. Establishing an effective security strategy results in an effective response to unexpected but inevitable contingencies.

Two year's worth of NIST-aligned training
Deliver a comprehensive security awareness program using this series' 1- or 2-year program plans.
For instance, we can look at the “Internet of Things” (IoT) landscape, a term which describes one of the major revolutions in recent years. Everyday appliances ranging from coffee machines and digital cameras to your smartphone or tablet all have an IP address and are connected to the Internet. From a malicious perspective, this represents a "tempting landscape" as well also a concern for everyone.
Through incident response combined with a deep forensic analysis, the number of security issues and computer attacks can be reduced and detected at an early stage. This should be a mandatory role for all the digital ecosystems that can be audited, such as Cloud Infrastructures, mobile devices, operating systems, and so on.
Relevance of Incident Response
Corporations must mandate and assemble a rapid response team to handle security incidents. It can be composed of a single person or a group of people properly trained within the organization. That team has responsibilities in monitoring, incident handling and reporting when a security breach is identified or an attack has been detected.
The immediate response typically consists of classifying the incidents: critical, normal or minor impact, and labeling the priority of these incidents into high, medium or low; as well as assigning the incidents to the teams for further investigations. A bad or a good decision directly impacts the resolution of the problem.
During the forensic analysis, a set of considerations should be kept in mind. For example, systems with external influences should be isolated, avoiding further damage, or as a means of preserving the evidence. This is not a forensic analyst task, but rather a measure that must be taken by the incident response team soon after the incident is detected. In these cases, the forensic analyst should always work with the incident response team so that they can make containment decisions, such as disconnecting network cables, the power supply of the devices themselves, increasing physical security measures or even turning off the device. These decisions must be made on the basis of existing policies; these teams know the real the impact of the problem and are aware of the risk of reproducing certain actions on the system.
For example, leaving a system offline for long hours makes it impossible for an organization to operate normally. Significant downtime can result in substantial monetary loss. Therefore, care must be taken to minimize disruptions to an organization's operations. It is the responsibility of this team to protect the evidence regardless of the situation.
These procedures should be clear and part of the incident response emergency plan. Some of these procedures can be listed as follows.
Short term:
- Detect, isolate and contain the compromised device restricting network access (in real time);
- Acquire the evidence without altering or damaging the original;
- Verify that your recovered evidence is the same as the originally seized data;
- Catalog the evidence identifying your “family” and the manner how the attack was propagated;
- Document the evidence;
- Transport evidence and ensure the integrity of the evidence;
- Deliver all the produced documentation during the process;
- Communicate the incident to the respective entity.
Longer term:
- Analyze the data without modifying it;
- Deepen visibility into processes and actions that occurred on devices and operating systems (or where the incident has occurred);
- Mitigate gaps and vulnerabilities;
- Focus on a scientific approach;
- Extensive reporting features.
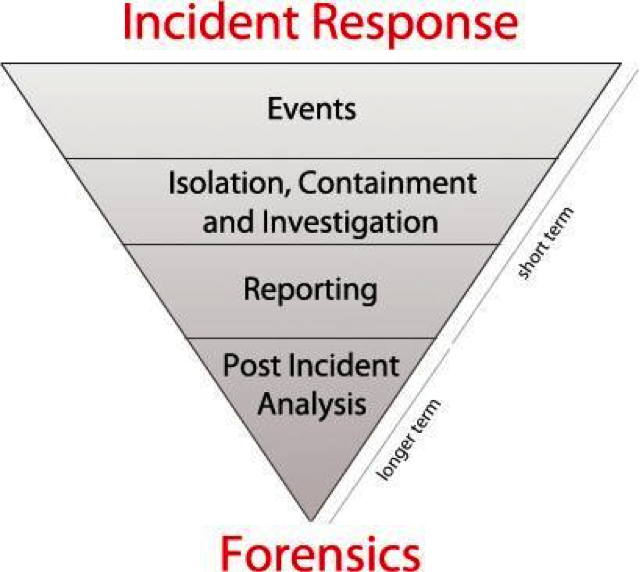
Figure 1 features a snapshot look at how the analysis of incidents is performed by incident response team.
Figure 1: Main steps of a security incident carried out by an Incident Response Team.
Looking for an official computer forensics course? Check out InfoSec Institute's award-winning training boot camp. Simply fill out the form below to receive course pricing details.
Incident Response Vs. Forensic Analysis
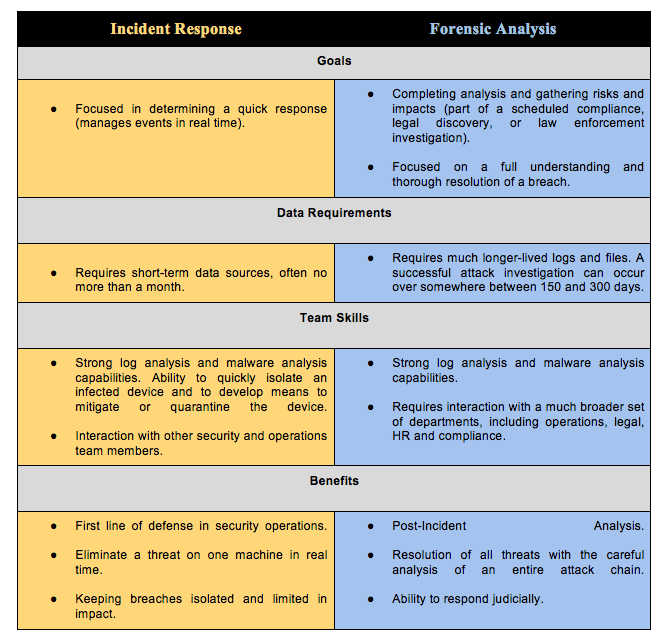
Incident Response and Forensic Analysis are two related disciplines that use similar tools. However, both have differences that are important to highlight:
- Goals
- Data Requirements
- Team Skills
- Benefits
Table 1 below shows in a brief manner the principal differences between incident response and forensic analysis.
Table 1: Differences between Incident Response and Forensic Analysis.
From the table above, we can see that an incident response specialist holds a particularly refined set of forensic skills. The inclusion of forensics as part of an incident response plan is crucial to understanding the true extent of a data breach.
References
[1] https://seguranca-informatica.pt/vulnerabilidades-em-2017
[2] https://www.infosecurity-magazine.com/opinions/the-importance-of-a-cyber-incident
[3] https://www.imf-conference.org/imf2007/2%20Freiling%20common_model.pdf
[4] https://pdfs.semanticscholar.org/ffec/5abb02dd451643b190c2bf0ffbd610666689.pdf
[6] https://www.giac.org/paper/gsec/569/computer-incident-response-computer-forensics-overview/101298
[7] http://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-86.pdf

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
[8] https://ziften.com/incident-response-versus-forensic-analysis