Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

API hooking and DLL injection on Windows
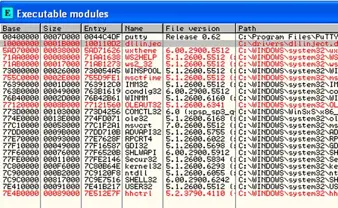
Using CreateRemoteThread for DLL injection on Windows

QR Code: USSD attack
Data Exfiltration Techniques
L-7 Protocol analysis

Visual Studio and Build Process

PayPal: Chargebacks and Dispute Resolution

The ASP.NET Internals

Phishing and Social Engineering Techniques 2.0
The Top 10 Internet Resources to Use After Suffering a Cyber Breach

Cyber Kill Chain is a Great Idea, But is It Something Your Company Can Implement?

OWASP’s 2013 Web Vulnerabilities List Will Shuffle the Top Ten
Delegates and Events: C#, Net 4.0

Vulnerability Assessment of SNMP Service – II
The Sysenter Instruction Internals

Stress testing your wireless network

Anatomy of a VB Virus

Open Source .NET: Platform-Independent .NET Application Development with MONO – part one

Pentesting distributions and installer kits for your Raspberry Pi

Vulnerability Assessment of SNMP Service – I
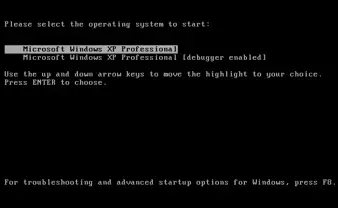
Introduction to Kernel Debugging with Windbg

E -Money Fraud

Form Authentication: ASP.NET Security Part 3
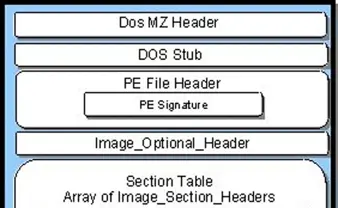
Presenting the PE Header