Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Dynamic Programming Tutorial

Phishing and social engineering techniques 3.0

Near field communication (NFC) technology, vulnerabilities and principal attack schema

IOS Application security Part 5 - Advanced Runtime analysis and manipulation using Cycript (Yahoo Weather App)

How USB Malware Works

Privacy Implications of Google Glass
.NET Application Domain Internal

Security Threats in Virtual World
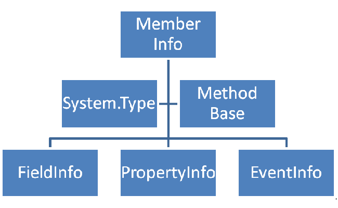
.NET Reflection

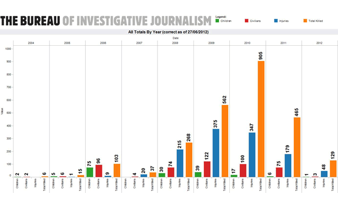
China vs US, cyber superpowers compared

iOS Application Security Part 4 – Runtime Analysis Using Cycript (Yahoo Weather App)

Data Exfiltration Techniques
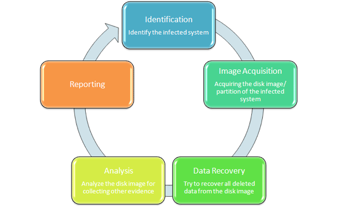
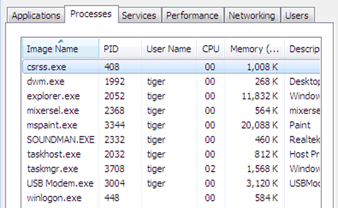
Linux and disk forensics

Calling NTDLL functions directly
LUKS and LVM
Hacking Drones … Overview of the Main Threats

Crypto building blocks
IOS Application security Part 3 - Understanding the Objective-C Runtime
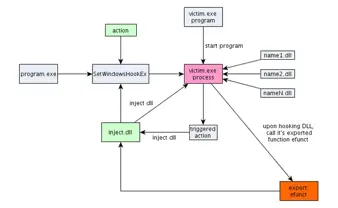
Using SetWindowsHookEx for DLL injection on windows

API hooking and DLL injection on Windows
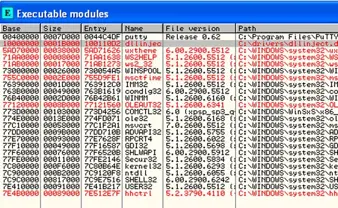
Using CreateRemoteThread for DLL injection on Windows

QR Code: USSD attack

Data Exfiltration Techniques
L-7 Protocol analysis