30+ cybersecurity tips for travelers
The biggest cybersecurity threat to travelers is the risk associated with using Wi-Fi hotspots. But public Wi-Fi is not the only threat. The main problem is that travelers often do not always take even the most basic security precautions they should. This problem is a lack of security awareness; for instance, business travelers often assume their companies are solely responsible for safeguarding the traveler’s data and devices and that is simply not true.
In this article, we will look at how travelers can protect themselves from cybercrime starting from the day they start packing to the day they arrive home, and practice safe Wi-Fi in public hotspots.
See Infosec IQ in action
How are travelers at risk?
Travelers, both vacation-goers and executives on business, can be easy meat for cybercriminals. According to KnowBe4, travel is one of the top five most phish-prone industries. Below, some alarming security travel truths from a Kaspersky Labs survey which illustrate how travelers can be more vulnerable when away from their comfort zone:
- People travelling abroad are more likely to be robbed of their data (one in five generally, and three in 10 senior business managers)
- Old habits die hard and 44 percent of people go online by the time they leave the airport, regardless of security risks. 82 percent of travelers connect to unsecured public Wi-Fi networks (e.g. travel terminals, hotels, cafes, and restaurants)
- 69 percent connect after they land in order to let family and loved ones know they have arrived safely. Three in five survey respondents (61 percent) spend the same amount of time – or more – searching for information on the Web when they are abroad
- Almost three in 10 respondents (28 percent) admit they have left devices unsupervised in public spaces
- 41 percent expect their employers to have set strong security measures. “Indeed, the view from the top is that, if employers are to send staff overseas, they must accept any security risks that go with it.”
- Half of the respondents surveyed (54 percent) indicated they made no distinction between their online activities when travelling for work or leisure
Cybercrime is a global concern, but, as can be seen from the below graph, some popular holiday destinations are more prone than others are to attacks like phishing.
The twist in the tale for business travelers
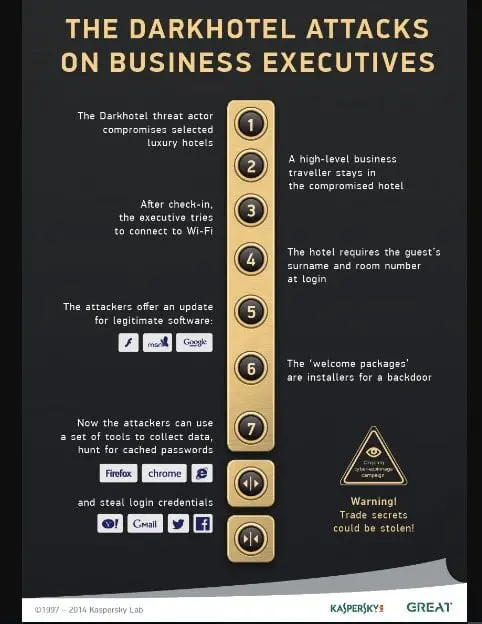
Besides the usual litany of cyberthreats Joe Public experiences at public Wi-Fi hotspots, business travelers face additional risks, theft of confidential company data and intellectual property. In a blog article Kaspersky Lab describes the Darkhotel threat – Malware (APT) Virus Threat – as “a combination of spearphishing and dangerous malware designed to capture confidential data.” It is aimed primarily at C-level executives.
Darkhotel was first reported by the FBI in 2012 but may have been operating as far back as 2009. The breadth and scope of the attack suggests the crime syndicate is a sophisticated one and well-heeled, prepared to invest heavily in time and technology. For instance, according to Kaspersky, the criminals even succeeded in forging digital security certificates for their malware. A particularly tasteless twist in the tale is that the malware is delivered as part of a RAR archive that “purports to offer sexual content,” making this a modern variant of the honey trap — the oldest scam in human history.
Below is an infographic of how Darkhotel works. Be very afraid.
(Source: Kaspersky)
The good news is that you can secure your data and devices to a large extent before you leave home, so there is less to worry about when you get to your destination. Below are three checklists to help you travel safe.
Before you leave – Secure your data
- Ditch any devices you really do not need to take with you. Besides weighing you down, additional devices create additional risks.
- Clear your device of unnecessary data, e.g. browser history or cookies, and remove software you won’t use or don’t need for your trip.
- Secure your device luggage bag with a combination lock against sticky fingers. Be wary of a backpack whose straps can be cut before you realize you’re traveling lighter than when you set out in the morning. At the risk of looking a little silly, hug your laptop bag to your chest.
- Change all your passwords before you leave and use a password manager.
- Update all software on all devices. Avoid updating software when traveling unless you are away a long time! Rather, check software websites for updates and make an informed decision about whether you really need to update an app; a security patch could be important, a new feature not so much.
- Enable multi-factor authentication for online accounts, e.g. Facebook, Dropbox, etc.
- Encrypt all data on devices. Encryption ensures your data, if stolen, is of no use to an attacker.
- Back up your devices. Schedule automatic backups while away; it will be one less thing to worry about
- Set up your own VPN. Experts suggest VPN providers may not keep your data quite as private as you imagine they are doing. Learn how to set up your own free VPN in the cloud or download a trusted VPN.
- Install a device finder and/or enable the Find My Device feature for Android, iOS or Windows.
- It is a common mistake to keep a list of important numbers, contacts and even passwords in a flat file on your computer. If you do, make sure you encrypt this file.
- Invest in a privacy screen to protect your device from criminals looking over your shoulder when you are working in public.
- Use Forget Network to remove all current Wi-Fi networks before you hit the road.
- Be aware of what sensitive company data you have that is vulnerable; this will help you to protect it effectively. For instance, confidential information can be stored in the cloud (using services such as Dropbox) rather than on your device. Accessing cloud storage using a VPN makes your data even more secure, so create an account before you leave.
- Consider creating a temporary email account, such as with Gmail or Hotmail, and set up encryption for all messages.
- Understand how spearphishing work. The more you know about cyber threats, the more alert you will be to your vulnerabilities.
- Make sure your protection software includes proactive defense against new threats, rather than just basic antivirus protection.
- Disable auto-connect to Wi-Fi and Bluetooth and minimize location sharing.
- Have a continuity plan in place in the event data is compromised.
- Consider using a “burner” phone or laptop.
Security tips for the journey
- Always verify executable files before running and be wary of attachments from both known and unknown sources.
- Limit software updates when travelling.
- Lock down your device.
- Do not use a hotel’s shared Wi-Fi lounge.
- Try not to use your personal devices for business and vice versa.
- Use your phone to verify email requests, e.g. if you lose a credit card and have to order a new one.
- Avoid sharing details of your trip on social (or business) media. Pick up the phone and let your friends, family and colleagues know where you are personally.
- Never leave a device unsupervised. That includes in a locked hotel room, where there may be an insider threat from cleaning staff.
- At public Wi-Fi hotspots, use a privacy screen, Be aware of people around you and do not share files or folders. If you must share, make sure data is password-protected. Try not to perform sensitive transactions, e.g. banking, online shopping and anything work-related, at public hotspots. Never use an “open” hotspot.
Back home – What’s next?
- Update your software again and apply any patches that may be pending.
- Do a post-trip backup of your data and delete any travel apps or information you used on your trip and no longer need. You can always do a restore if you need to.
- Change your passwords again. You may have been unknowingly compromised during your travels, with thieves in the wings waiting to pounce now that you are home.
- Get a financial statement to make sure no money has gone AWOL while you were traveling.
- Do a malware/virus scan on all devices .
Practice Wi-Fi safety and be security-savvy
Ironically, emphasis on data privacy, like the introduction of GDPR, has potentially opened a new market for cybercriminals. As reported by Travel & Meetings Buyer, Kris Budnick, the lead partner for PwC Cyber Africa, pointed out that if a hotel faces a fine of X amount if their guests’ data is breached, a criminal could offer to charge the hotel less not to disclose the information. There is little individuals or organizations can do to mitigate this risk first-hand which is why security awareness is so important.
Innovative food for thought: as reported by Business Insider’s Mark Abadi, Off the Grid CEO Zach Beattie takes a giant leap further down the security line: his travel company takes away vacationers’ smartphones before they start their trip and gives them "dumb phones" that can't take photos or access the Internet. It’s not only about security: “The goal is to encourage travelers of all ages to be more present in the moment on vacation.”
Security awareness is a habit. If you practice and prepare, you can travel in comfort and safety, with the peace of mind that a trip ought to give you.
See Infosec IQ in action
Sources
- Cybercrime Statistics Expose Five Industries Most Susceptible to Phishing Attacks, KnowBe4
- Kaspersky Lab International Travel Report: the urge to connect at any cost is putting international travelers’ data at risk, Kaspersky Lab
- Darkhotel: a spy campaign in luxury Asian hotels, Kaspersky Lab
- Darkhotel Malware (APT) Virus Threat, Kaspersky Lab
- Digital spring-cleaning tips to help speed up and secure your devices, Quartz
- How to Set Up Your Own Completely Free VPN in the Cloud, Lifehacker
- How to encrypt files and folders in Windows 10, 8 or 7, Comparitech
- What is a burner phone?, TechTarget
- How to Deal With a Data Breach of Your Personal Info, PrivacyPolicies.com
- 5 ways to lockdown your mobile device, CSO Online
- Increased legislation makes hotels bigger cybercrime targets, Travel & Meetings Buyer
- Millennials travel without a cell phone with Off the Grid, Business Insider