Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
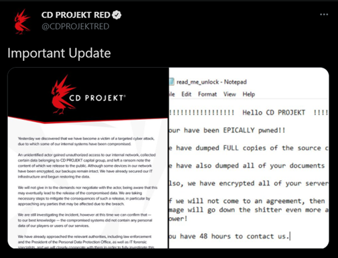
HelloKitty: The ransomware affecting CD Projekt Red and Cyberpunk 2077

Introduction to Secure Software Development Life Cycle

Security awareness manager: Is it the career for you?
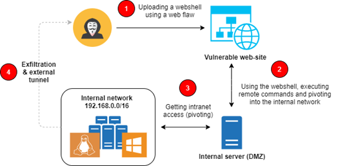
Whitespace obfuscation: PHP malware, web shells and steganography

Cybersecurity Weekly: DOJ prioritizes ransomware, CODESYS flaws, Realtek bugs

Top 18 tools for vulnerability exploitation in Kali Linux

Penetration tester salary

Explore Python for MITRE PRE-ATT&CK, network scanning and Scapy
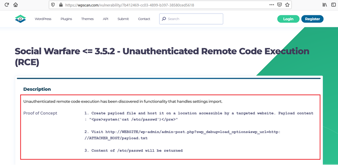
WPWN: 1 VulnHub capture the flag walkthrough
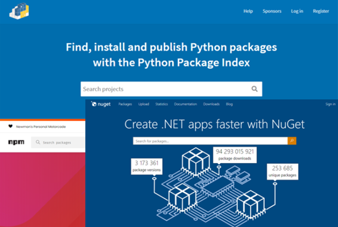
Dependency confusion: Compromising the supply chain

Become a cyber first-responder with this intrusion detection course

Role of digital signatures in asymmetric cryptography
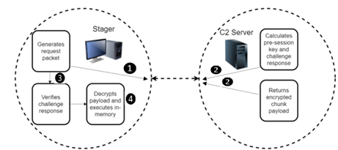
BendyBear: A shellcode attack used for cyberespionage

Android security: Everything you need to know [Updated 2021]

3 tracking technologies and their impact on privacy

Cybersecurity Weekly: Job offer ID theft, Bluetooth vulnerability, SolarWinds hackers target think tanks

Risks of preinstalled smartphone malware in a BYOD environment

In-game currency & money laundering schemes: Fortnite, World of Warcraft & more
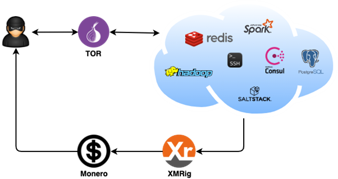
DreamBus Botnet: An analysis

Malware analyst: Is it the career for you?

How to run a software composition analysis tool

How to run a SAST (static application security test): tips & tools

How to run an interactive application security test (IAST): Tips & tools

How to run a dynamic application security test (DAST): Tips & tools