Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Introduction to SIEM (security information and event management)
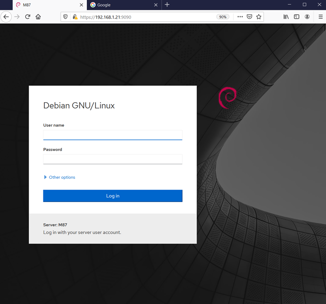
M87 1: VulnHub Capture the flag walkthrough

Phishing attacks doubled last year, according to Anti-Phishing Working Group

Introduction to Kubernetes security

Kali Linux: Top 5 tools for social engineering
Kobalos malware: A complex Linux threat

Threat Modeling 101: Getting started with application security threat modeling [2021 update]

VPNs and remote access technologies
What is Operation Dream Job by Lazarus?

The Phish Scale: How NIST is quantifying employee phishing risk

7 entry-level cybersecurity career questions, answered!

Cybersecurity Weekly: DarkSide quits, STRRAT attacks, Mercari data breach
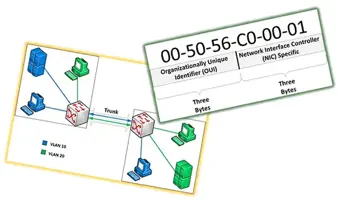
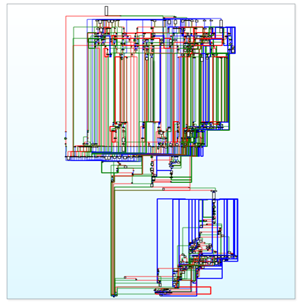
VLAN network segmentation and security- chapter five [updated 2021]
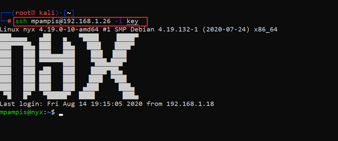
NYX 1: VulnHub CTF walkthrough

CCPA vs CalOPPA: Which one applies to you and how to ensure data security compliance

IT auditing and controls – planning the IT audit [updated 2021]

Cybersecurity Weekly: Favicon backdoor, triple extortion scheme, ransomware for sale

Quantitative risk analysis [updated 2021]

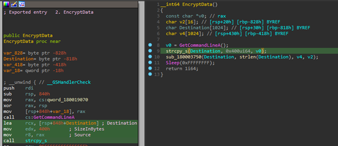
Trojan URSA malware: How it works and how to prevent it

Finding security defects early in the SDLC with STRIDE threat modeling [updated 2021]
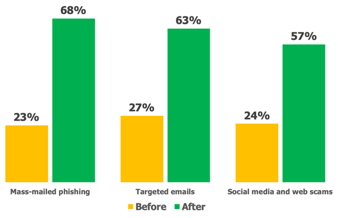
The ROI of security awareness training
Understanding DNS sinkholes - A weapon against malware [updated 2021]

GANANA: 1 VulnHub CTF walkthrough part one
TBBT: FUNWITHFLAGS VulnHub CTF walkthrough part 1