Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

CRISC Domain #2 - IT Risk Assessment
DARKHOLE: 1 VulnHub CTF Walkthrough

CRISC Domain #1 - Governance
R-TEMIS: 1 VulnHub CTF walkthrough

Average CSSLP Salary in 2021

SOC 3 compliance: Everything your organization needs to know

Learn the 3 pillars of cyber security risk management and leadership
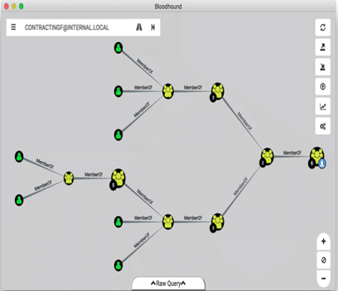
Red teaming tutorial: Active directory pentesting approach and tools

SOC 2 compliance: Everything your organization needs to know

Application security: Is AppSec the right career for you?

Cybersecurity Weekly: REvil shuts down, PowerShell flaw, iOS 15 hacked

SOC 1 compliance: Everything your organization needs to know

Cybersecurity professionals share career advice in celebration of Cybersecurity Career Awareness Week

Best CDPSE study resources and training materials
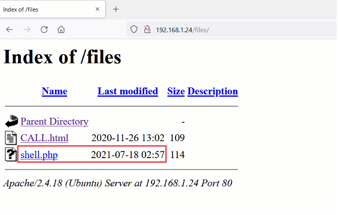
HACKABLE: II CTF Walkthrough

Online certification opportunities: 4 vendors who offer online certification exams [updated 2021]

Overview: Understanding SOC compliance: SOC 1 vs. SOC 2 vs. SOC 3

Best CSSLP study resources and training materials

JavaScript and web development are key skills for security pros, says Vladimir de Turckheim

Top 30 most exploited software vulnerabilities being used today
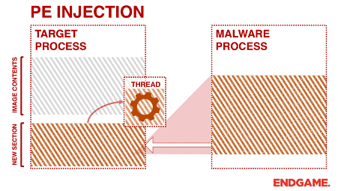
Red Team tutorial: A walkthrough on memory injection techniques

Threat intelligence researcher: Is it the career for you?
MOMENTUM: 1 VulnHub CTF walkthrough

The ransomware paper (part 1): What is ransomware?