Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Protecting yourself from Social Engineering Attacks

Facebook Hacker Cup 2013 Qualification Round: Beautiful strings
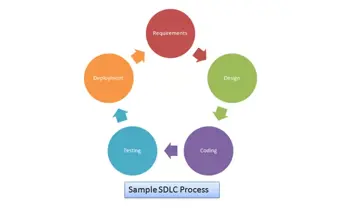
Introduction to secure software development life cycle

Social Media use in the Military Sector
MetaData and Information Security

Linux Hardening

Android Application Assessment
The Basics of ASP.NET

CompTIA Security+: SY0-301 Study Guide excerpt

Invoking Article 51 (self-defense) of the UN Charter in Response to Cyber Attacks – II
Introduction to Blackberry Balance Technology

Invoking Article 51 (self-defense) of the UN Charter in Response to Cyber Attacks - I

Restricting social media at work

Arbitrary file download: Breaking into the system

Using X5S with Fiddler to find XSS Vulnerabilities
Demystifying dot NET Reverse Engineering: Advanced Round-trip Engineering
Tips and Tricks for Using Two-Factor Authentication Technology
Security Assessment of Blackberry Applications:

LUKS: Swap, Root and Boot Partitions
AAnval - SIEM by Tactical Flex
Command line for Windows malware and forensics

Wordpress Security for Users
Using Technology To Enhance Public Safety
IDA: Jumping, searching and comments