Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Evolution of Banking Malwares, Part 1

2015 Security Predictions: The Rise of Hacking Campaigns

Fast Flux Networks Working and Detection, Part 2

Pattern-Based Approach for In-Memory ShellCodes Detection

Cloud VPN Security Recommendations

Breaking Software Protection - RSA

New Developments in Net Neutrality

Cracking Android App Binaries
Fast Flux Networks Working and Detection, Part 1

User Behavior Modeling with Mobile Device Sensors

Legality of Jailbreaking Mobile Phones

Broken cryptography

The Importance of POS Threat Analysis for the Retail Sector

Website Hacking Part V
File inclusion attacks
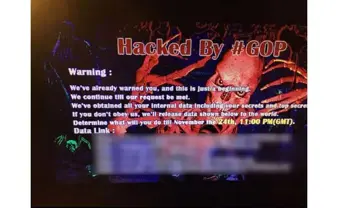
Cyber attack on Sony Pictures is much more than a data breach - updated

Privacy risks of beacons

Windows Azure Platform

How to Stop DNS Hijacking

Avoiding mod security false positives with white-listing

WebSocket security issues

A physical security policy can save your company thousands of dollars

Examining Android App Specific Data on Non-Rooted Devices
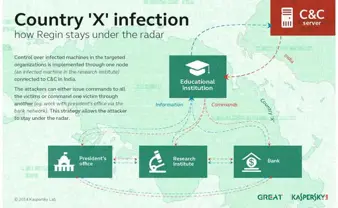
Regin: State-Sponsored Malware or Cybercrime?