Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

How to Deal with Reverse Domain Name Hijacking

MOOSE Malware: Analysis

Social Engineering - A Case Study

The Top Five Cyber Security Vulnerabilities

Win32/Lethic Botnet Analysis

Office 365 Compliance Matrix

Content Security Policy

Introduction to Reverse Engineering
Cyberspace : A Fast-growing Area of Crime

Firefox Plug-ins a Security Engineer Needs to Know

Securely Managing Public/Private Keys for Cloud Services
Secure Your Application Using .htacess File

Interview: Chris Rouland

Identifying Vulnerable Code
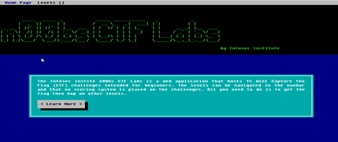
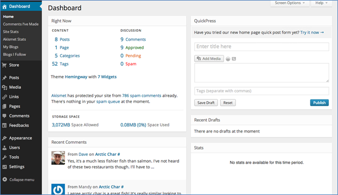
n00bz CTF Challenge #2: Practical Website Hacking

MOOSE Malware: Basics
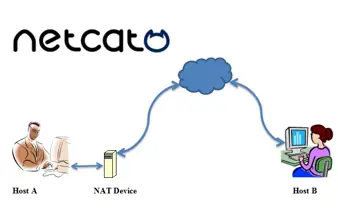
Netcat uses

Transition of ISO 27001: 2005 to ISO 27001: 2013

Interview: Darren Guccione, Co-founder of Keeper Security
Analyzing and writing a local exploit

Interview: Dr. Engin Kirda

Enhancements in Damn Vulnerable iOS app version 2.0

Malware Researcher’s Handbook: Introduction

Card fraud in the deep web