Secure Your Application Using .htacess File
What is Wordpress?
WordPress is a free, open-source blogging tool and content management system (CMS) based on PHP and MySQL. Features include a plugin architecture and a template system. WordPress was used by more than 23.3% of the top 10 million websites as of January 2015, making it the most popular blogging system in use on the Web with more than 60 million websites. It was first released on May 27, 2003, by its founders, Matt Mullenweg and Mike Little, as a fork of b2/cafelog. The license under which WordPress software is released is the GPLv2 (or later) from the Free Software Foundation.

Learn ICS/SCADA Security Fundamentals
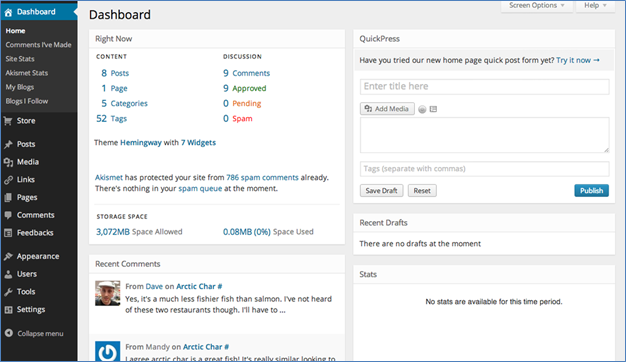
Fig: Display Wordpress login panel
Because WordPress has a large number of security vulnerabilities, it's essential to take some steps to secure your WordPress application. In this article, we will learn how we can secure the WordPress application by configuring .htaccess file. There are thousands of WordPress attack types, such as directory traversal, SQL injection, executable file upload, remote code execution, Cross-site scripting etc.
What is .htaccess file?
An .htaccess (hypertext access) file is a directory-level configuration file supported by several web servers that allow for decentralized management of web server configuration. They are placed inside the web tree, and are able to override a subset of the server's global configuration for the directory that they are in and all sub-directories.
Typically, the WordPress .htaccess file looks like the following:
# BEGIN WordPress
RewriteEngine On
RewriteBase /
RewriteRule ^index.php$ - [L]
RewriteCond %{REQUEST_FILENAME} !-f
RewriteCond %{REQUEST_FILENAME} !-d
RewriteRule . /index.php [L]
# END WordPress
Let's start with the basic function of .htaccess file, where we will limit the access your admin folder by IP address. Admin access page, for instance http://httpsecure.com/wp-admin to log into WordPress, from where you can access to any admin pages. Before starting with another configuration, this is basic security to secure your WordPress, it's really important to protect your /wp-admin directory with any brute force and guessable attack.
How to restrict?
You just need to copy the below codes and paste them into .htaccess file. Note that this goes in the /admin folder only NOT root folder .htaccess.
Restrict Admin Access from Your IP Only
# Limit logins and admin by IP
# this goes in the /admin folder only NOT root folder .htaccess
order deny,allow
deny from all
allow from 125.32.32.32
Above mentioned code denies all accesses to the admin folder, with the exception of your IP address. But, if you using a dynamic IP, you might have to alter this file regularly otherwise you will be denied.
Restrict specific IP address
If you have found that someone trying to access your content or brute force your admin pages or with a specific IP address, you can restrict that IP only instead of deny all.
order allow,deny
deny from 154.323.263.14
deny from 125.5.5.25
deny from 65.245.54.5
allow from all
Limit Directory Browsing
WordPress is widely used by millions of users as well as also developers. Due to this knowing the structure is not the hard part of a WordPress installation. An attacker can easily browse into your application, as they already knew where to discover what plugins you have used and find other information through your files. To prevent this, you can use following .htaccess code to prevent directory browsing.
# directory browsing
Options All -Indexes
How to protect wp-config.php file?
Wp-config.php is the file in your root directory which stores the important information about your application as well as databases credentials. It is private so that we can prevent the second person know it with the following code.
order allow,deny
deny from all
How to Prevent Access to wp-content?
The wp-content is a file that contains all themes, plugins and images so that it is important to the WordPress installation. You can allow everyone to see images, CSS, etc., but limit access to the important PHP files with the following code.
Order deny,allow
Deny from all
Allow from all
How to implement Individual File Protection?
Sometimes you may want to protect individual file instead of the whole folder. Adding the following code into .htaccess file, you can do that.
# Protect the .htaccess
order allow,deny
deny from all
In the above-mentioned code, we have taken .htaccess file example where if someone tries to access the same then, it throws a 403 error. You just need to replace the file name if you want to protect other files.
How to create custom directory?
You can easily change a default index file of directory by using below code in your htaccess file. Let's suppose if a user requested /abc/, Apache will serve up /abc/index.html, automatically.
#Custom Directory Index Files
DirectoryIndex index.html index.php index.htm
How to redirect to customized error page?
If you want to redirect your users to an error page, whenever 404 status occurs. You can use below code in htaccess file to map 404 error to error page errors/404.html.
#Custom Error Pages
ErrorDocument 404 errors/404.html
How to redirect http to https (ssl)
Add following snippet to your htaccess and redirect entire website to https.
RewriteEngine On
RewriteCond %{HTTPS} !on
RewriteRule (.*) https://%{HTTP_HOST}%{REQUEST_URI}
How to deny access to static file data
Denies any request for static files (images, css, etc) if referrer is not a local site or empty.
Use below code for the same
RewriteCond %{HTTP_REFERER} !^$
RewriteCond %{REQUEST_URI} !^/(wp-login.php|wp-admin/|wp-content/plugins/|wp-includes/).* [NC]
RewriteCond %{HTTP_REFERER} !^http://www.askapache.com.*$ [NC]
RewriteRule .(ico|pdf|flv|jpg|jpeg|mp3|mpg|mp4|mov|wav|wmv|png|gif|swf|css|js)$ - [F,NS,L]
How Specify Upload file limit for PHP using htaccess
2) Maximum size of the post data ,
3) Maximum time in seconds a script is allowed to run before it is terminated by the parser
php_value upload_max_filesize 2M
php_value post_max_size 2M
php_value max_execution_time 100
php_value max_input_time 100
How to Change Charset and Language headers
AddDefaultCharset UTF-8
DefaultLanguage en-US
How Set httponly and secure flag using htaccess
#Set Cookie with httponly and secure flag
php_value session.cookie_httponly 1
php_value session.cookie_secure 1
How to enabled X-XSS-Protection?
This header enables the Cross-site scripting (XSS) filter built into most recent web browsers. It's usually enabled by default anyway, so the role of this header is to re-enable the filter for this particular website if it was disabled by the user. This header is supported in IE 8+, and in Chrome.
Use the header X-XSS-Protection "1; mode=block".
# Turn on IE8-IE9 XSS prevention tools
Header set X-XSS-Protection "1; mode=block"
How to enabled X-Content-Type-Options: nosniff?
This header prevents "mime" based attacks. This header prevents Internet Explorer from MIME-sniffing a response away from the declared content-type as the header instructs the browser not to override the response content type. With the nosniff option, if the server says the content is text/html, the browser will render it as text/html.
# prevent mime based attacks
Header set X-Content-Type-Options "nosniff"
How to enable X-Frame-Options
The X-Frame-Options HTTP response header can be used to indicate whether or not a browser should be allowed to render a page in a <frame> or <iframe>. This can be used to avoid clickjacking attacks, by ensuring that your content is not embedded into other sites.
This directive is pretty similar to the frame buster code explained in "Double Trouble on Google Images" except that it is only supported in the following browsers:
- Internet Explorer 8+
- Opera 10.50+
- Safari 4+
- Chrome 4.1.249.1042+
There are three possible values for this header:
- DENY - This setting prevents any pages served from being placed in a frame even if it is on the same website it originates from. should be used if you never intend for your pages to be used inside of a frame.
- SAMEORIGIN - This setting allows pages to be served in a frame of a page on the same website. If an external site attempts to load the page in a frame the request will be denied.
- ALLOW-FROM origin - If the value contains the token ALLOW-FROM origin, the browser will block rendering only if the origin of the top-level browsing context is different than the origin value supplied with the Allow-From directive.
# Prevent from Clickjacking attack
Header set X-Frame-Options DENY
Reference
http://en.wikipedia.org/wiki/WordPress
https://whatswp.com/secure-wordpress-site-with-htaccess/

Learn Python for Pentesting
http://viralpatel.net/blogs/21-very-useful-htaccess-tips-tricks/








