Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

An asset management guide for information security professionals
What is the difference between business continuity planning & disaster recovery?

Risk treatment options, planning and prevention

DNS analysis and tools
ICMP reverse shell

Average Computer Forensic Investigator Salary

Top 5 Password Managers in 2017

The Top 10 Ways to Protect Your Intellectual Property from Unscrupulous Remote Employees

Computer Forensics: Overview & Types of Database Forensics

Average MCSE Salary 2018

Computer Forensics: Web, Email, and Messaging Forensics

Average VMware Certified Professional Salary (VCP6)

Average CCDA Salary 2018

Average CCENT Salary 2018

Penetration Testing: Career Path, Salary Info, and More
Intellectual Property Investigations

Top 10 Tips for Keeping Your Smartphone Secure

Mobile CTF Challenge Contest Details - Win up to $1,000!

Computer forensics certifications

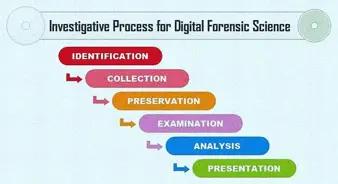
Mobile forensic process: Steps and types

Phishing Attacks in the Hospitality Industry

The Unattended Use of Stingray Devices Finally Gets Noticed

Top 10 Questions to Ask Developers About Customer Data Security

Computer Forensics: Digital Forensics