Infosec IQ release: 4 new training modules, Orchestration Center upgrades & more
November 02, 2020
The latest Infosec IQ release includes new Need to Know training modules, additional automation options within the PhishHunter Orchestration Center and more!
Jump ahead
- Need to Know training modules
- Reorder Orchestration Center Rules
- Update to API version 2
- What else is new
- See what’s coming next
Watch the new Need to Know modules
Four new Need to Know training modules are live in Infosec IQ, following your favorite cast of characters as they learn about malware, password security, removable media and mobile encryption.

Need to Know: Malware Forecast
A malware storm is rolling in, but don’t worry. Cecil is here to help!
Need to Know: Creating Strong Passwords
Anthony helps Harold create a new, strong password. Turns out what he really needs is just a little more...creativity.
Need to Know: Mystery of the Misplaced Media
It’s a media mystery as Anthony tries to track down the movements of a strange USB drive.
Need to Know: Mobile Encryption
Ivana learns to take cybersecurity with her and gets armored up with encryption.
Need to Know volume two now includes 16 training modules with additional modules and assessments coming soon! Log in to Infosec IQ to watch every training module.
Reorder orchestration rules to improve your threat response
You can now reorder Orchestration Center rules to specify PhishHunter’s order of operations when automatically assigning tags and malicious scores to employee-reported emails. This gives you more flexibility when building complex automation and ensuring the right action is taken on emails that match multiple rules.
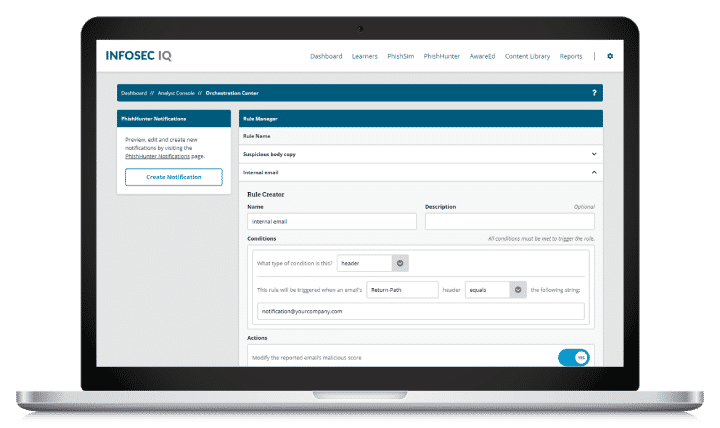
Because rules are processed in the Rule Manager from the top down, we recommend moving your strongest or most important rules to the bottom to ensure they are applied and not undone by competing rules.
Example: Modifying an email’s malicious score
Your employee reports an email that matches the following two rules.
Rule 1: Internal email
- Condition: Email header Return-Path equals: “notifications@yourcompany.com"
- Action: Set the malicious score to 0
Rule 2: Suspicious body copy
- Condition: Email body contains: “wire transfer”
- Action: Increase the malicious score by 20 percent
Rule 1 is your strongest rule, because it uses the email header information to verify an email was sent by your organization and should be categorized as safe with a malicious score of zero. Rule 2 searches for suspicious email body text such as “wire transfer” to influence the malicious score and encourage your security team to investigate.
If an employee-reported email matches both rules, the rules are processed from the top down. This means rule 1 will be applied first, setting the malicious score to zero. Next, rule 2 will be applied, increasing the malicious score by 20 percent. This is not your desired outcome because an email you know to be safe will be assigned a 20 percent malicious score.
Instead, you should reorder Rule 1 to the bottom of your Rule Manager, to ensure it is the last rule applied and the safe, employee-reported email is set with a malicious score of zero.
Update to API version 2
We released a new version of our API to improve performance and efficiency for retrieving the most commonly accessed information.
What changed
The List timeline events and List learner timeline events endpoints will now return data IDs. Additionally, new endpoints were added for querying the related details.
What this means for you
If you are currently utilizing our API, please replace “v1” with “v2” in the URI. If you are using the List timeline events and List learner timeline events endpoints will need to begin using the new additional endpoints to continue collecting additional timeline event details. Please refer to the documentation below regarding the following new endpoints:
- Retrieve quarantine email
- Retrieve a phishsim template
- Retrieve an assessment
- Retrieve a browser
- Retrieve a campaign
See the v2 API documentation here
Version 1 (V1) of our API has already been deprecated and we hope to fully disabled by the end of this year. If you have any questions about the new version, please reach out to customer-support@infosecinstitute.com
What else is new
November Newsletter: International Computer Security Day
November 30th is International Computer Security Day. Help raise awareness about the importance of cybersecurity with November’s Need to Know Newsletter and give your workforce four ways to adopt secure practices.
Delete Orchestration Center Rules
Along with the latest Orchestration Center updates, you can now delete rules created in the Rules Manager.
See what’s coming next
Want a preview of the training content and features coming soon? Read the LX Labs roadmap to see what our talented content team is working on and reference the Infosec IQ product roadmap for upcoming features.