The Current Job Outlook for Threat Hunters
Introduction
Demand for cybersecurity professionals is on the rise, and even specialized niche positions are seeing an increase in popularity. This makes threat hunting an especially sought-after job role, particularly in big corporations that are looking to identify and neutralize threats that are not easily detected by traditional security measures. This ensures that they keep their environment safe and secure.
We will take a closer look at the current state of demand for threat hunters, job titles and responsibilities, and potential earnings for individuals that choose to embark on this exciting career path.

Cybersecurity interview guide
What Is a Threat Hunter and What Do They Do?
We can think of threat hunters, also known as cyberthreat hunters, as IT professionals with a strong foundation in information security. They are responsible for searching their organizations’ IT systems, applications and data for security issues that are either known or unknown. They are able to do this by leveraging their considerable cybersecurity skills to find anomalies within their environment and then take corresponding actions to neutralize or mitigate any threat that they are able to find.
Using threat hunters greatly improves an organization’s ability to avoid downtime and data breaches, making them more competitive in their respective industries. The role is a mixture between programmer, analyst, security specialist and incident responder, and as such, blends in these responsibilities and requires that the candidate shows competence in all of those domains.
What Are Threat Hunter Job Titles and Roles?
Not all job roles are cut and dried when it comes to threat hunting, and there is usually some overlap in responsibilities depending on the size of the organization and how many systems there are to manage and maintain. What follows are some of the most common job titles, followed by some key job functions that a candidate would have to manage.
IT Security Specialist
Responsibilities include device and policy management; firewall configuration, deployment and management; SIEM solution management; security appliance maintenance; network device analysis; and intrusion detection.
Senior Cyberthreat Hunter
Threat-actor-based investigation; create new detection methodologies; provide expertise to incident responders; monitor environment and devices; detect, disrupt and remove threats; data analysis; threat intelligence; advanced security technologies.
Lead Cyberthreat Hunter
Coordinate incident response teams; respond to security incidents; support security operations center; apply analytics, threat intelligence and advanced security technologies.
Security Operations Analyst
Work from the security operations center; analyze network traffic; analyze large datasets; analyze data logs; establish normalized traffic and data flows; develop baseline analysis toolkits; develop technical theories; identify tactics, techniques and procedures used by malicious actors; develop alerting criteria.
As you can see, not all roles will explicitly state that the role is that of a threat hunter, but based on the skills that are required, as well as the job functions, you can tell where the role is mainly concentrated. There are many elements that need to be understood and mastered for a candidate to successfully land such a role, and a lot of experience in the field of IT security is advantageous as well.
Next, we will look at what required skills and certifications these roles typically require.
Required Skills and Certifications/Qualifications
Due to the dynamic nature of threat hunting, there is no exact qualification list guaranteeing a candidate will land a role as a threat hunter. The following certifications are some of the most commonly-requested certifications when these types of roles become available. Usually, the candidates are required to have only one, but more certifications can usually provide some advantage. These useful certs include:
- Certified Ethical Hacker (CEH)
- Certified Information Systems Auditor (CISA)
- GIAC Systems and Network Auditor (GSNA)
- GIAC Certified Incident Handler (GCIH)
- Certified Computer Security Incident Handler (CSIH)
Threat hunting also relies on data analytics, computer programming, scripting and, more recently, even machine learning and artificial intelligence, all of which have become must-have topics of familiarity for candidates. For this reason, it is often recommended that a candidate should possess a degree in computer science, although this is not necessarily the case for all threat hunting-related roles.
Specific required skills include knowledge of the following:
Monitoring Tools
There is a wide range of devices that need to be monitored by a threat hunter. Firewalls, antivirus software, DLP solutions, network logs, server logs and endpoint monitoring are just some examples of the kinds of monitoring tools that a threat hunter should be familiar with.
SIEM and SOC technologies
Candidates should be familiar with SIEM tools and the way in which they are used to collect data within an organization. When configured correctly, they are able to give security specialists an overview of the current state of the entire environment, including errors and warnings.
Tools and Analytics
There are many different approaches to data analysis, and threat hunters must be familiar with all of them. These techniques include searching, clustering, grouping, and stack counting. Each requires its own set of tools, ranging from the simple Microsoft Excel for data sorting to the more complex AI and ML platforms that compile huge selections of seemingly-unrelated data into threat models for further analysis.
Earning Potential for Threat Hunters
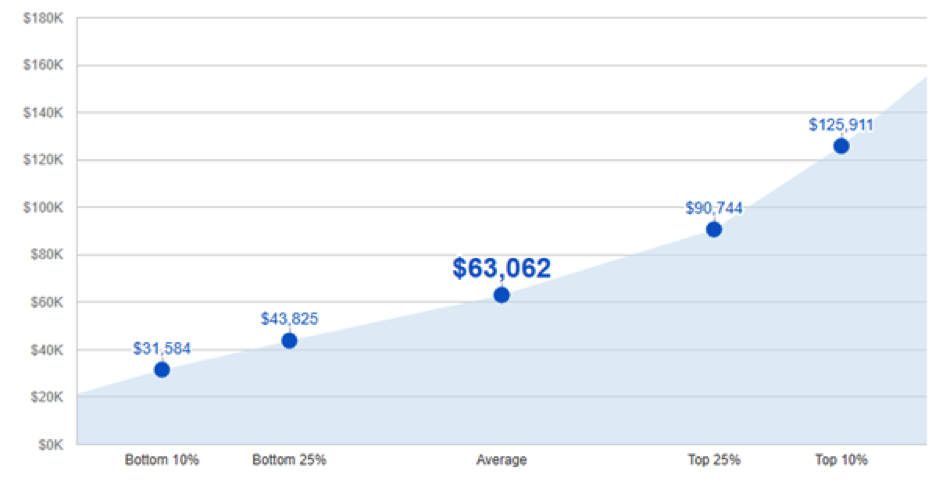
Threat hunters have some excellent earning potential, as shown in the following graph taken from here.
Experience and qualifications play an important part of the equation with earnings, as is the case with most IT-related positions. It’s encouraging to note that the scope for improvement in earnings rises by nearly four times when tracking the improvement trend from the bottom 10% to the top 10% of the graph. This means that taking on a junior role in a threat hunting-related role can offer growth to an individual if they choose to pursue it further.
Threat hunting roles are also growing in availability: per Cybersecurity Insiders’ 2018 Threat Hunting Report, the field is showing a 5% growth rate over last year’s stats. This reflects the importance of assembling a threat-hunting capability within a company, and how important this skill is to modern organizations.
Conclusion
If chasing down unknown threats while analyzing massive pools of data sounds like a job that’s too good to be true, then threat hunting could be just the line of work for you. It requires patience, attention to detail, and an excellent understanding of how IT systems work and collect data. Being a threat hunter puts you on the front line in the war against cybercriminals, and offers excellent opportunities for professionals to learn and grow while protecting infrastructure and networks safe from criminal elements.
For more information about any of the above qualifications mentioned in this article, be sure to check out InfoSec Institute to find the right course for you. Also take a look at InfoSec Institute’s exciting bootcamp offerings to help kickstart your training plans for 2018!
Sources
2018 Threat Hunting Report, Cybersecurity Insiders
What Does a Cyber Threat Hunter Do?, Digital Guardian

Learn Threat Modeling
Current and Future Trends in Threat Hunting, Cybersecurity Insiders