WSUS (Windows Server Update Services)
Introduction
Windows Server Update Services (WSUS) can be used to manage the deployment of the latest Microsoft Windows operating system updates. When using WSUS, we can fully manage the distribution of updates within the network, we can download software updates from Microsoft, and we can deploy them to computers in our own network [1].

Learn Network Traffic Analysis for Incident Response
WSUS comprises the following components:
- Microsoft Update—Microsoft website that distributes security updates.
- Windows Server Update Services (WSUS)—The server that is installed on the Windows Server 2003/2008, which can be used to manage and distribute security updates through administrative console. It can obtain updates from Microsoft Update or from another WSUS server.
- WSUS Administration Console—This is automatically installed on the WSUS server and can also be installed on other Windows operation systems and can be used to manage WSUS server inside the network.
- Automatic Updates—This is a service built into the Windows operating system that can be used to get updates from Microsoft Update or from a WSUS server.
Installation of Windows Server 2008 and WSUS
If we would like to have WSUS on our local network, we first need to install the Windows Server 2003 or 2008. We downloaded the trial version of Windows Server 2008 from the official Microsoft website and installed it; we won't describe the process in detail, since you probably should be able to install an operating system without too much hassle. The installation procedure for WSUS differs quite a lot, depending on whether we're installing it on Windows Server 2003 or 2008:
- Windows Server 2003: We must first download the WSUS from here and install it. Note that the installation executable is quite big—approximately 80MB. We need to download the 32 or 64-bit executable based on the operating system that we want to install WSUS onto. We also need to install IIS web server prior to installing WSUS. If you're already running Windows Server 2003, you can find detailed instructions at [3].
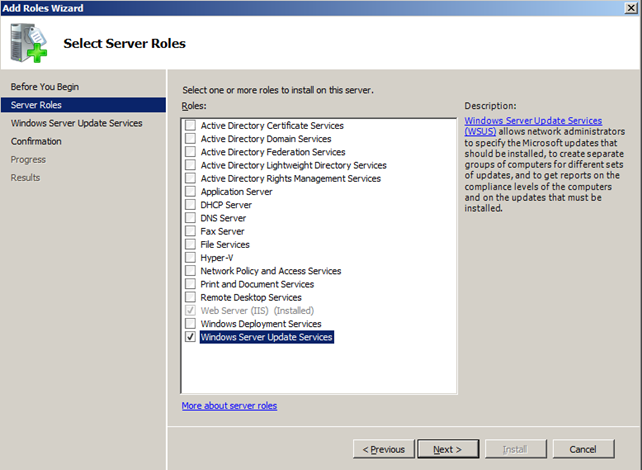
- Windows Server 2008: To install WSUS, we need to go to Start/All Programs/Administrative Tools/Server Manager and click on "Add Roles." After clicking next, we need to select the "Windows Server Update Services" as seen in the picture below. Note that by choosing the WSUS role, the IIS server role will be added automatically, which is also needed for WSUS to install and run successfully (this role was added in Windows Server 2008, and is not present in older windows versions, like Windows Server 2003).
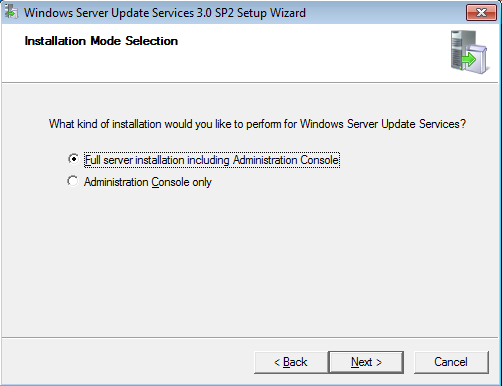
This will download the WSUS and install all appropriate roles/services, so we don't need to download WSUS or install "Web Server (IIS)" role manually; this will all be done automatically. When installing WSUS server, we need to choose "Full server installation including Administration Console" rather than "Administration Console only," as shown in the picture below.
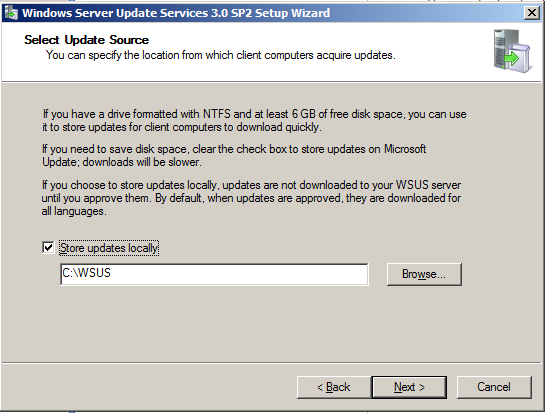
On the next step of the installation, we need to accept the terms and license agreement and click "Next." Then, we have to specify the local directory where the updates will be stored; we need to select "Store updates locally" and select the appropriate directory for updates. If we uncheck the "Store updates locally" checkbox, then the updates will be downloaded directly from the Microsoft website when needed. This can be seen in the picture below.
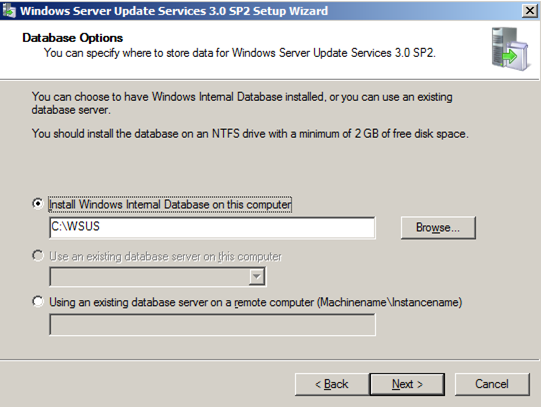
We also need to choose the method that will be used to manage the WSUS database. We can choose among the following options that are also presented below:
- Install Windows Internal Database on this computer—By choosing this option, the installation wizard will use the Internal Database and we won't need to have a running instance of the MSSQL database. But sometimes, it might be better to use an existing MSSQL database if we already have one in our network; this is because we would like to keep everything in the same place: in the database.
- Use an existing database server on this computer—We can choose this option if the MSSQL database server is running on the current computer.
- Using an existing database server on a remote computer—We can choose this option if the MSSQL database server is running on the remote computer.
In our case we'll choose the Internal Database option as presented in the picture below:
Before finishing the installation, we also need to select the website that WSUS will use; we can choose between two options:
- Use the existing IIS Default Website—By choosing this option, the WSUS will use the default website on port 80 (this can only be chosen if port 80 is not already in use).
- Create a Windows Server Update Services 3.0 SP2 Website—If some service is already using port 80, we have to choose this option, where the WSUS will create a website on port 8530 or 8531.
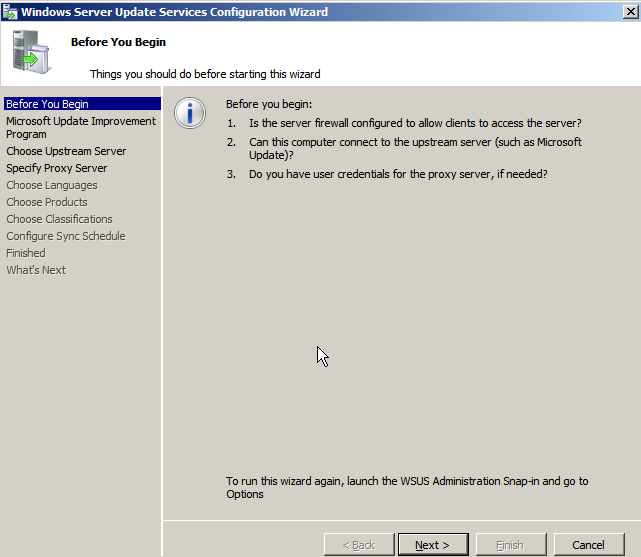
After the installation process, we need to follow a few configuration steps, as outlined below. The first step basically tells us what we need to do before configuring WSUS, such as properly configuring the firewall.
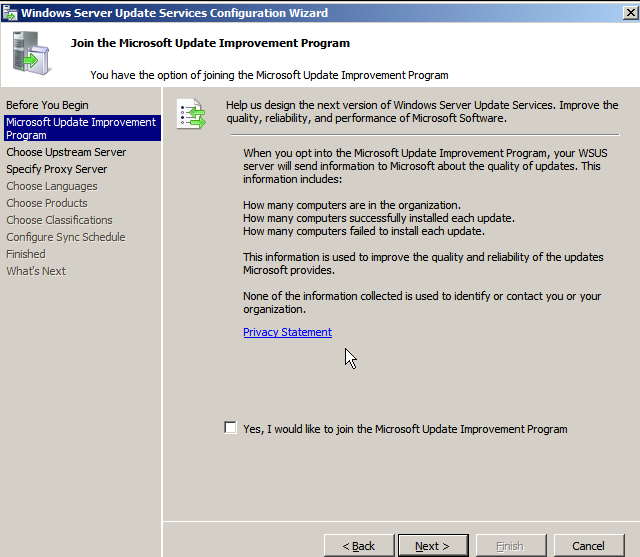
The next step is asking us whether we would like to join the Microsoft participation program, where we can safely uncheck the checkbox.
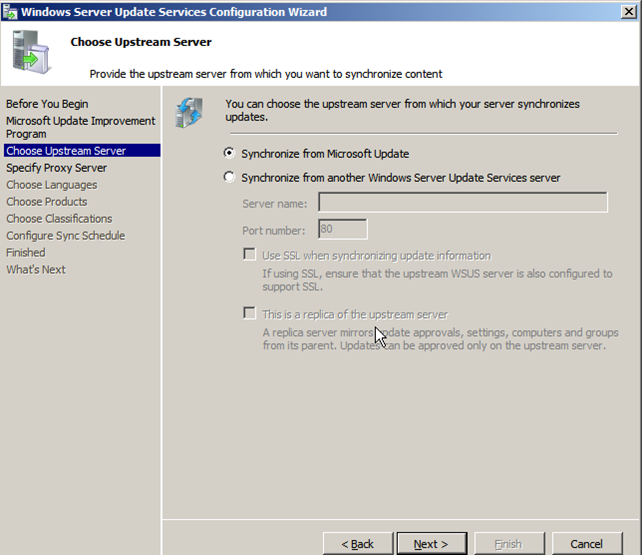
After that we need to select "Synchronize from Microsoft Update," which will pull the updates from the Microsoft website rather than from another WSUS server.
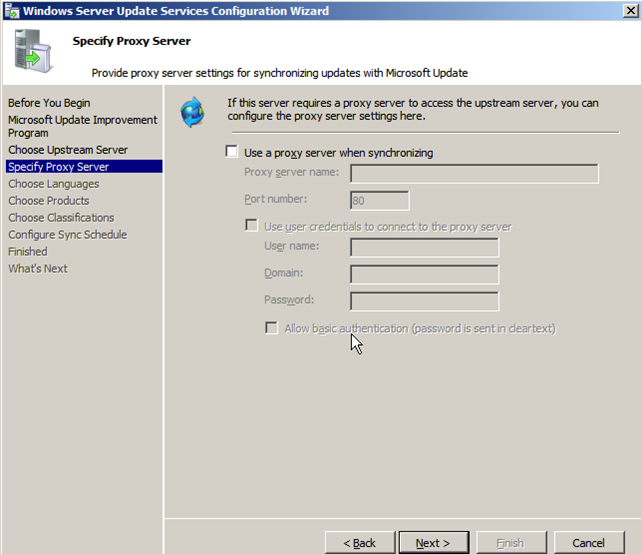
Now we can specify the proxy configuration options if a proxy is needed to connect to the internet; in our case it isn't, so we can leave those settings blank and click on the "Next" button.
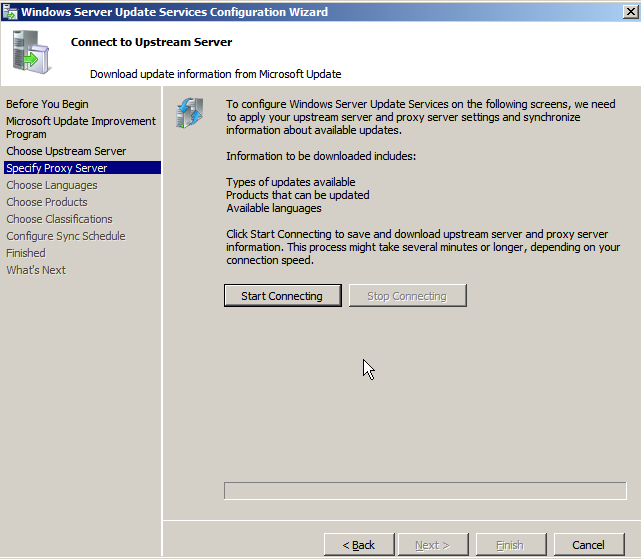
On the next screen, we need to click on the "Start Connecting," which will synchronize the information about available updates, languages and products that can be updated.
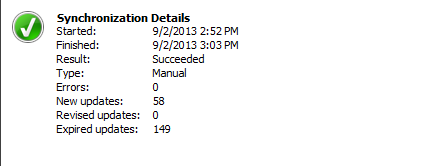
This process will actually start downloading the information from the Microsoft web server and saving them into the C:WSUS directory we selected when installing WSUS. The updating will take a few hours and, once done, it will display a message similar to this one:
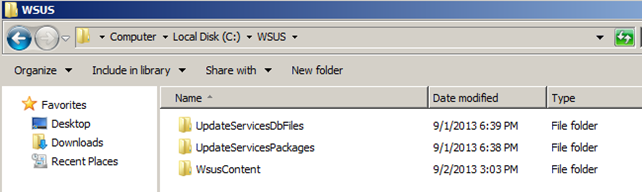
After that we can finish the installation procedure. The C:WSUS directory will now contain 2.09 GB of data and will contain the folders seen below.
Configuration of WSUS Server
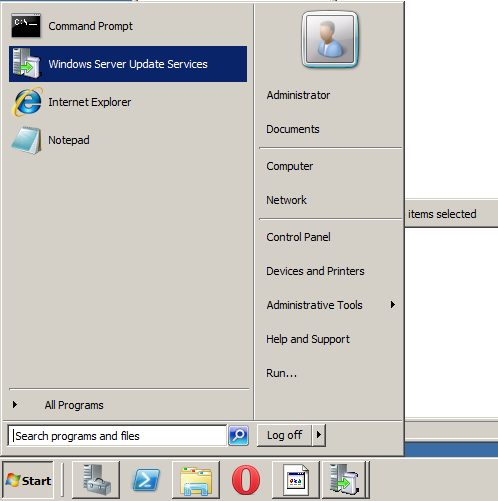
Then we can click on the Start/Windows Server Update Server as shown in the picture below to start the update services.
The WSUS is shown below:
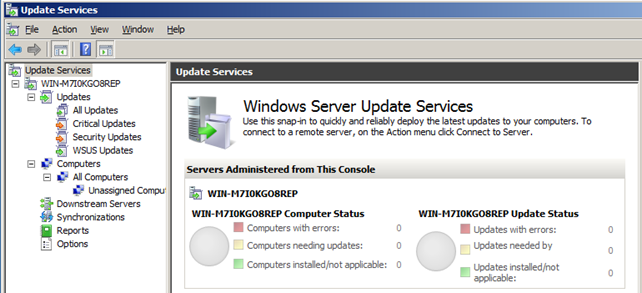
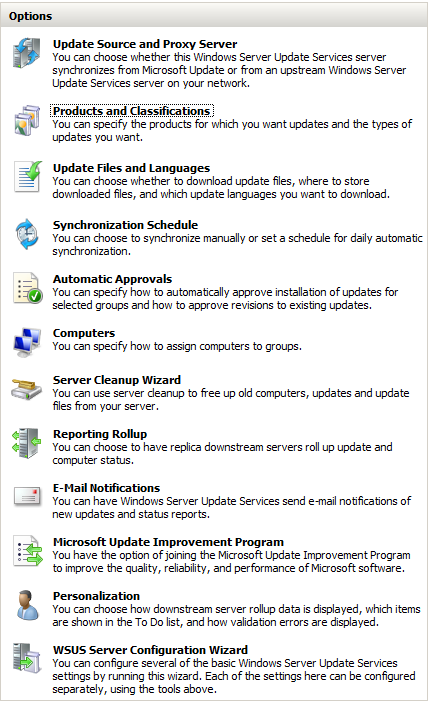
We can click on "Synchronizations" on the left side to check whether all updates have been successfully synchronized. One interesting entry on the left side is also the Options tab, where we can change most of the options we selected when installing WSUS. All of the options can be seen in the picture below:
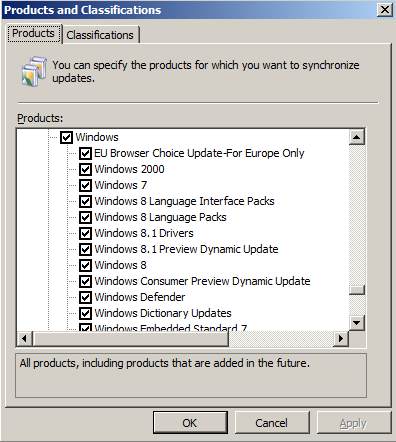
We can click on the "Products and Classification" to select for which products we would like to receive updates; we can select various product categories such as Windows or specific products like Windows 7. In the picture below, we can see that we had selected the Windows category, which includes all Windows operating systems and also some other products.
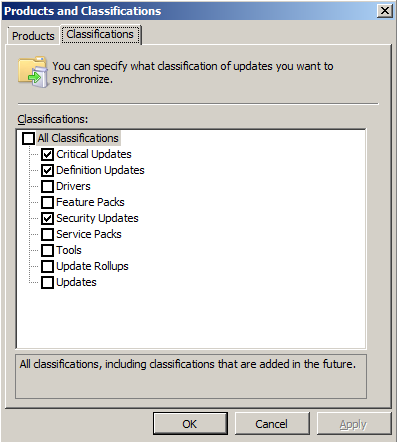
Under the "Classification" tab, we can select the update classifications that we want to obtain. Currently the "Critical Updates, "Definition Updates," and "Security Updates" are selected as seen below.
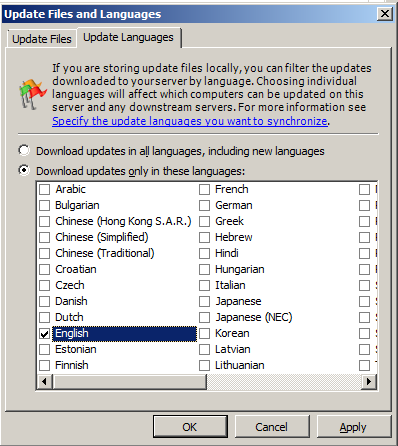
If we would like to minimize the amount of downloaded updates, we should select "Update Files and Languages" and select to update only the English version of updates; note that this is applicable if we're using only English Windows operating systems, because only those updates will then be distributed among clients. If you're unsure whether you need this option or not, keep the default option to synchronize all languages and you'll be able to update all computers in your network. We can see those settings in the picture below.
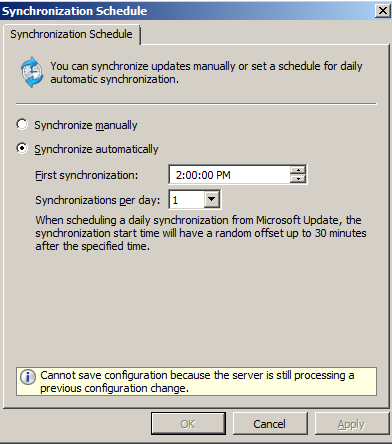
Under "Synchronization Schedule," we can select to download the updates automatically every night at 2AM, as seen below.
One great function of WSUS is the "E-Mail Notification" system, which can be used to automatically send email when new updates are synchronized. The settings can be seen below; they are disabled by default, but we can very easily enable them and fill out the email server settings in the "E-Mail Server" tab.

On the left side of the WSUS window, we can also select "Security Updates" and chose to select any security updates. When pressing the "Refresh" button, all appropriate security updates will be shown to us, as displayed below.
Configuration of WSUS Client
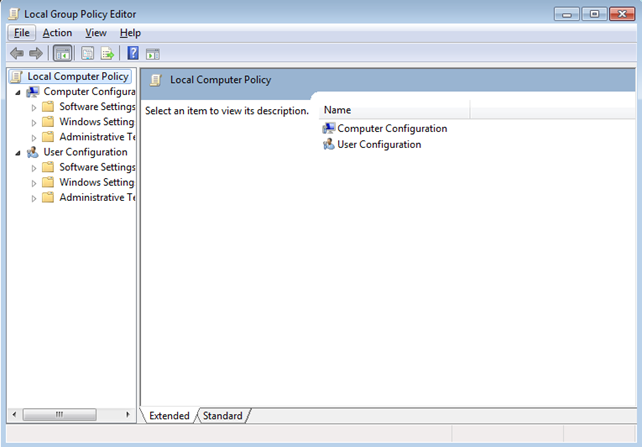
Now we've come to the point where we'll actually be doing something useful: updating the client computers. We introduced WSUS into our network because we want Windows clients to contact WSUS server over HTTP, which distributes updates to them to keep them secure. Here we'll take a look at how to force client to check in with the WSUS server when no active directory is present in the network. We can do that by using the Group Policy Editor. Group Policy is a Windows feature that is used to manage users' access to Windows features. We can start it by going to Start /Run/gpedit.msc. The Local Group Policy Editor will open, as shown below.
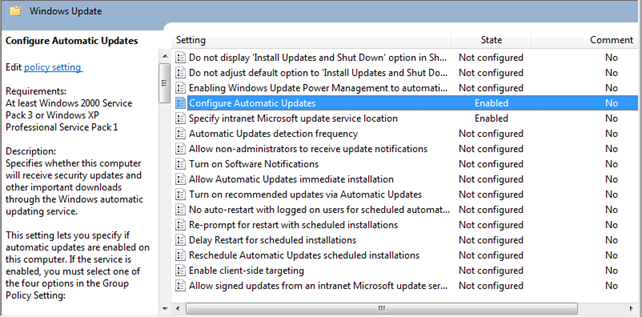
We have to navigate to Computer Configuration/Administrative Templates/Windows Components /Windows Update and change two configuration options:
- Configure Automatic Updates—We only need to enable this option.
- Specify intranet Microsoft update service location—We need to specify the http://win-m7i0kgo8rep/ as the value, which is the URL address of the Windows Server 2008 though which the updates are accessible.
Both configuration options need to be in "Enabled" state, as seen below.
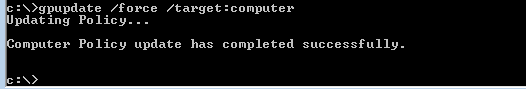
After that, we need to apply the configuration options we made to the local group policy with the gpupdate command, as seen in the picture below. We can see that the computer policy was successfully updated.
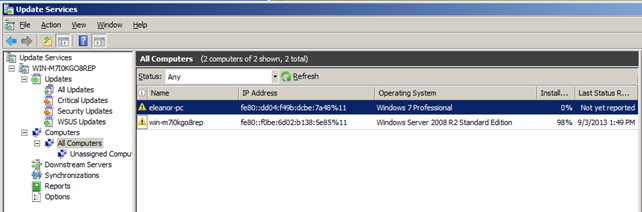
Soon after that we can then notice both computers in the "All Computers" tab in WSUS as seen in the picture below. Notice that the newly joined Windows 7 computer doesn't have any updates installed yet, as it hasn't yet reported anything back to the WSUS server.
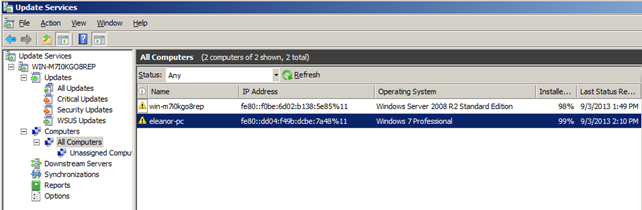
Soon the client will send over the details about its installed updates and the screen will be updated as follows, where the client has changed its "Installed" column to 99%.
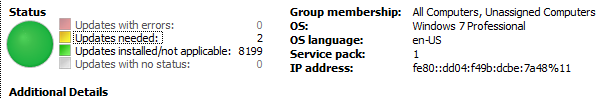
If we click on the client item, we can quickly determine which updates are missing from the system. At first, we'll see the following information, where it clearly states that two updates are still needed to completely update the system.
If we click on the "Updates needed:" link, we'll be presented with the window below; note that before this window will be available, we'll have to install "Microsoft Report Viewer Redistributable 2008" package, which can be obtained from the Microsoft website.
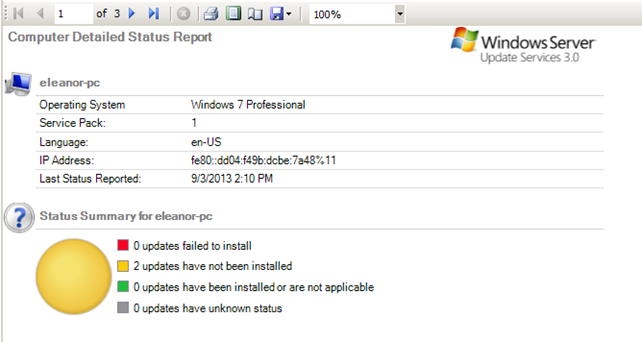
In the picture above, we can see that we're still on the first of three pages, so if we click on the left arrow to move to the next page, we'll see the exact updates that weren't installed on the system.
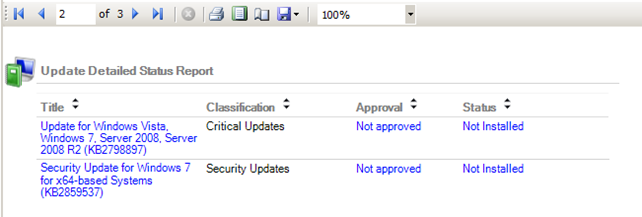
If we click on each of the missing updates, we'll get detailed information about the update and why it is important. Keep in mind that all updates should be installed as soon as possible to avoid potential risk of compromise.
Conclusion
In this article we've seen how we can install and configure WSUS server, which can be used in our own network to manage security updates for whole network. The main advantage of using WSUS instead of automatic updates on each client separately is the benefit of managing updates from one central location, which can offer an important overview over the installed updates in the network.
References:
[1] Windows Server Update Services, accessible at http://technet.microsoft.com/en-us/windowsserver/bb332157.aspx.
[2] Overview of Windows Server Update Services 3.0 SP2, accessible at http://technet.microsoft.com/en-us/library/dd939931(v=ws.10).aspx.

Learn Threat Modeling
[3] 2003 Server, accessible at http://www.edugeek.net/forums/windows-server-2008-r2/80624-how-setup-wsus-2003-2008-2008-r2-server.html.







