Panama Papers - How Hackers Breached the Mossack Fonseca Firm
Introduction
The Panama Papers are a huge trove of high confidential documents stolen from the computer systems of the Panamanian law firm Mossack Fonseca that was leaked online during recently.
It is considered the largest data leaks ever, the entire archive contains more than 11.5 Million files including 2.6 Terabytes of data related the activities of offshore shell companies used by the most powerful people around the world, including 72 current and former heads of state.

Learn Python for Pentesting
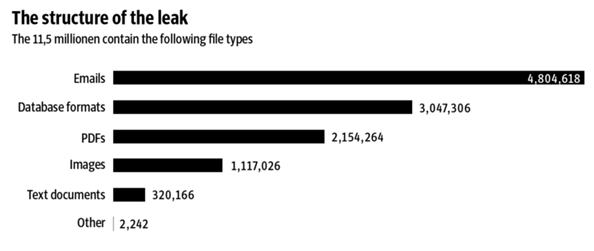
Figure 1 - Data Leaked (Source: Süddeutsche Zeitung)
To better scale the dimension of the data leaks, let's compare the dimension of the stolen data to the size of archives disclosed after other incidents occurred in the past.
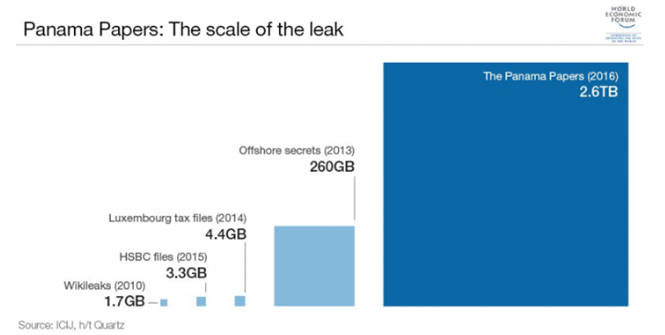
Figure 2 - Panama Papers - Scale of the data leak (WEF)
Despite the great clamor on the case, most of the clients of the Mossack Fonseca weren't breaking any law because the services offered by the firm are legal. The problem is that the service offered by the Panamanian firm could be abused by a part of its client to evade taxes and launder money.
Mossack Fonseca states it conforms to anti-money-laundering, it states it could not be condemned for failings by intermediate that consist of financial institutions, legislation companies and also accounting professionals.
Mossack Fonseca is the globe's fourth greatest company of overseas solutions. Even more compared to fifty percent of the firms are signed up in British-administered tax obligation places, as well as in the UK itself.
The Panama Papers case is exposing the offshore activities of hundreds of politicians and public figures around the world, including Vladimir Putin and the Iceland's Prime Minister David Gunnlaugsson.
At the time I was writing, despite the Vladimir Putin's name does not appear in the leaked documents, $2 Billion route leads right to Vladimir Putin. The Russian head of state's buddy, Sergei Roldugin, is the link between the Russian leader and the financial operations managed by the Panamanian firm.
The leaked documents also revealed the existence of an overseas mutual fund run by the dad of the British head of state David Cameron that allowed him to avoid paying tax obligation in Britain by employing a little military of Bahamas citizens to authorize its documents.
Amongst national leaders with overseas wide range are Nawaz Sharif, Pakistan's head of state; Ayad Allawi, ex-interim head of state as well as previous vice-president of Iraq; Petro Poroshenko, head of state of Ukraine; Alaa Mubarak, child of Egypt's previous head of state; as well as the head of state of Iceland, Sigmundur Davíð Gunnlaugsson.
Figure 3 - Panama Papers
Bloomberg first confirmed the authenticity of the leaked archive, citing the declaration of Ramon Fonseca, the co-founder of the Mossack Fonseca firm.
The Panama Papers documents were shared with the German newspaper Suddeutsche Zeitung by an anonymous source and the International Consortium of Investigative Journalists (ICIJ) that includes the Guardian as well as the BBC.
The journalists of the ICIJ have analyzed the documents in the huge archive for an entire year and now are sharing their findings.
The Panama Papers archive includes emails, bank records, and invoices belonging to the clients of the Mossack Fonseca firm.
Who is the anonymous source and how did it exfiltrate the data from the computers of the company?
According to Ramon Fonseca, the confidential documents had been obtained illegally by hackers; likely the data breach affected an e-mail server of the company last year.
The media agency El Espanol confirmed this hypothesis; Mossack Fonseca firm sent an email to its clients announcing that it was investigating the causes of the data breach and that it's taking "all necessary steps to prevent it happening again."
"This firm, considered the largest platform figureheads of Latin America and has a large portfolio of Spanish customers, said in a statement that it has opened an investigation after confirming that "unfortunately" has suffered an "attack on your server email."" reported the El Espanol.
"Mossack Fonseca says it is taking "all necessary steps to prevent it happening again"; which has "reinforced" its security systems; and is working with "expert consultants" to determine the exact information they have accessed "unauthorized persons". The firm, through its Director of Marketing and Sales, apologizes to its customers and offers an email to clarify any further questions."
The ICIJ has identified more than 214,000 organizations for a total turnover of several billion dollars.
Who and how Hacked the Mossack Fonseca firm?
Let's start trying to understand how hackers breached the firm. After the attack, security experts started testing the systems of the company trying to discover the presence of alleged flaws exploitable by attackers.
How is it possible that a company that keeps secrets of thousands of the world's leading organizations and men have been hacked in the so simple way?
The tests conducted by security researchers revealed the existence of flaws in the systems the company exposed on the Internet.
One of the first assumptions made about the alleged hack is that the hackers exploited a flaw in a plugin called Revolution Slider used by the WordPress-based website used by the company.
Sources on the Internet state that Mossack Fonseca has been compromised by hackers that run a SQL Injection attack on one of its sub-domains used for payments.

Figure 4 - Mossack Fonseca's Domain alleged breached by hackers
An unknown researcher that used the Twitter account @1x0123 claimed to have found a SQL injection flaw on one of the corporate systems belonging to the Panamanian lawyers Mossack Fonseca firm.
"They updated the new payment CMS, but forgot to lock the directory /onion/," he said via the "1x0123" Twitter profile.
In the past, the same hacker has discovered many other security issues in the systems of major media outlets, including the LA Times and New York Times. He also offered for sale the access to insecure systems at NASA.
@1x0123 also contacted Edward Snowden, notifying him of some bugs on one of his projects. Snowden acknowledged the bug report on the Freedom of the Press Foundation website.

Figure 5 - @1x0123 claims to have discovered a SQL Injection in the MossackFonseca Systems
Giving a close look at the image shared by the hacker, it seems that system is based on an Oracle database. Of course, it is not possible to be sure if this is the flaw exploited by hackers. Anyway, the presence of similar bugs is worrying if we consider the secret information contained in the database of the Panamanian firm.
Experts at WordFence security firm also provided an interesting analysis of the incident, describing how the hackers may have violated the email servers of the company via the WordPress Revolution Slider plug-in.
They also explained how attackers likely accessed the documents of the Mossack Fonseca firm exploiting the vulnerabilities affecting an outdated version of the Drupal CMS.
The hack of the email server, confirmed by the firm in an email sent to its customers, occurred by exploiting a vulnerability in the version of Revolution Slider that the company was running.
Once the attacker gained access to the WordPress website, he was able to view the contents of wp-config.php which contains the database credentials for the WordPress instance, and these credentials are in clear text.
The attacker would have used the credentials to access the database.
Experts at WordFence discovered that the www.mossfon.com is running two plugins in addition to Revolution slider, the WP SMTP plugin and the ALO EasyMail Newsletter plugin.
The WP SMTP plugin stores email server address and login information in plain text in the WordPress database.
Once the attacker had access to WordPress database credentials in the wp-config.php file, he was able to access the mail server.
The ALO EasyMail Newsletter plugin offers list management functionalities and needs access to read emails from the email server. Also, in this case, the plugin stores email server login information in the WordPress database in plain text.
"Once the attacker also had access to this data, after gaining access to the WordPress database via Revolution Slider, they would have been able to sign-into the email server and would be able to read emails via POP or IMAP." Reported Wordfence.
Summarizing, it is likely that an attacker gained access to the WordPress website by exploiting a known vulnerability in the Revolution Slider; then he accessed the database where were stored information on the email systems.
The experts highlighted that the firm did not enforce the principle of least privilege for the hacked systems, allowing the WordPress plugin email accounts to have the access to resources that they don't need.
The experts at WordFence also explained how hackers probably gained access to corporate client documents by accessing the web portal a thttps://portal.mossfon.com/,
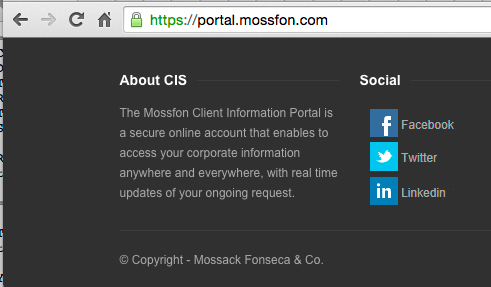
Figure 6 - Mossack and Fonseca web portal
Unfortunately, the portal was running an unpatched Drupal version, the 7.23, that was affected by dozen vulnerabilities.
The experts at WordFence were also able to access the changelog.txt file on the web portal that confirms the firm's website was running a flawed version of Drupal.
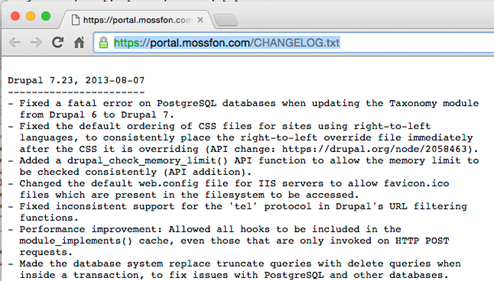
Figure 7 – Drupal 7.23 Changelog.txt
Once the attacker is compromised "the client login permissions system," he could access any information stored on the portal.
Embed this video
<iframe src="https://player.vimeo.com/video/161966079" width="640" height="360" frameborder="0" webkitallowfullscreen mozallowfullscreen allowfullscreen></iframe>
Now we have a clear idea of possible hacking techniques adopted by hackers in the Mossack Fonseca breach, anyway, it is quite impossible to understand who is behind the attack.
The attackers appear politically motivated; they operated with the specific intent to disclose secret information, likely to destabilize political context in various countries.
Unfortunately, the cyber security posture of the company failed in protecting the precious information highlighting the importance of security when dealing with confidential information.
References
http://panamapapers.sueddeutsche.de/en/
http://securityaffairs.co/wordpress/45998/data-breach/panama-papers.html
http://www.elespanol.com/espana/20160403/114488656_0.html
http://securityaffairs.co/wordpress/46216/breaking-news/panama-leaks.html
http://www.techeconomy.it/2016/04/11/panama-papers-ecco-come-stati-hackerati-dati/
http://www.theregister.co.uk/2016/04/11/hackers_pwn_mossack_fonseca/
http://www.forbes.com/forbes/welcome/#13fbd7c71df5
https://www.wordfence.com/blog/2016/04/panama-papers-wordpress-email-connection/

Learn Container Security
https://www.wordfence.com/blog/2016/04/mossack-fonseca-breach-vulnerable-slider-revolution/








