Dropbox hack, TikTok’s user data confession and new Android VPN spyware
Dropbox discloses hack of 130 GitHub repositories, TikTok admits Chinese staff can access EU and UK user data, and a new Android VPN spyware. Catch all this and more in this week’s edition of Cybersecurity Weekly.
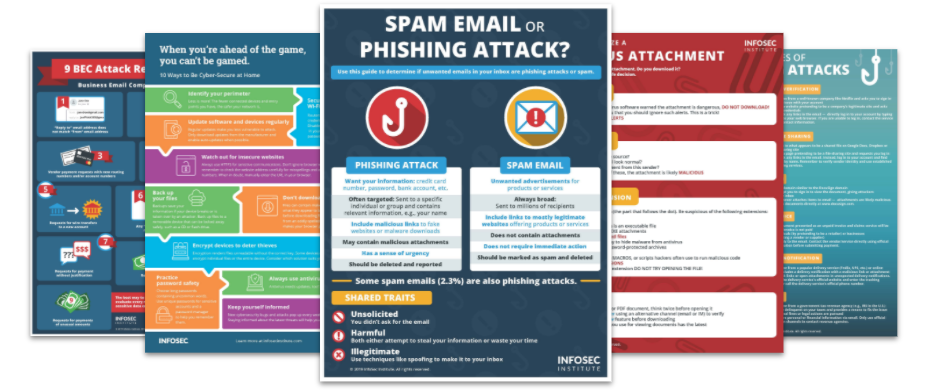
Top Security Awareness Posters
1. Dropbox admits 130 private GitHub repos copied after phishing attack
Dropbox disclosed it was a victim of a phishing campaign that allowed hackers to access 130 of its GitHub source code repositories. The threat actors impersonated the code integration and delivery CircleCI, which Dropbox uses for select internal deployment, to trick Dropbox employees into sharing their GitHub login details. The repos breached contain data mainly used by developers, such as API keys.
2. TikTok confirms Chinese staff can access UK and EU user data
TikTok has informed its European users that their data can be accessed by its employees in China and other non-EU countries. The social video giant revealed such access is necessary to ensure the app’s appropriate functionalities. The company has also updated its privacy policy to reflect how many personnel have this level of access, with the new rules applicable from December 2.
3. New SandStrike spyware infects Android devices via malicious VPN app
Cybersecurity company Kaspersky has warned about a malicious VPN app infecting Android devices with spyware. Dubbed SandStrike, the spyware helps threat actors siphon data from victims’ devices, including contacts and call logs, and even connect to a remote server to gather additional commands. The booby-trapped VPN app is said to be advertised on fabricated social media accounts to lure potential victims into installing the software.
4. Analysts track gift cards to see how scammers use them in BEC attacks
Analytics at Cofense conducted a five-week experiment to see if they could replicate how scammers utilize gift cards in BEC (business compromise email) attacks. In one instance, they found a scammer impersonating the firm's CEO to steal funds from a senior researcher who's spent many years raising awareness about BEC. The analysts were particularly surprised by the swiftness in which scammers moved funds after luring a victim, with most cards stolen, re-sold and used within 24 hours.
See Infosec IQ in action
5. Twitter brings on $8 fee, phishing emails target verified accounts
As Twitter rolls out its $8 blue tick subscription service, verified users have become the subject of email phishing attacks. BleepingComputer has come across several new phishing emails designed to steal information from verified accounts. Like most phishing emails, these emails relay a false sense of urgency, asking users to log into their Twitter account or risk suspension. The phishing workflow gathers the victim’s Twitter username and password, then proceeds to send them 2FA code via SMS.