MITRE ATT&CK vulnerability spotlight: Timestomping
MITRE Corporation is a non-profit and federally funded research and development center (FFRDC) that provides unbiased R&D and assessment services to the U.S. government. One of the research areas that MITRE pursues is cybersecurity.
Part of MITRE’s efforts in the cybersecurity field is the creation and maintenance of the MITRE ATT&CK matrix. This is a tool for classifying and organizing stages in a cyberattack and the various means that an adversary can accomplish them.

Implementing HIPAA Controls
One stage in the attack life cycle involves evading the defender’s attempts to detect or protect against potential intrusions. Timestomping is one method that attackers use to accomplish this.
What is timestomping?
Every operating system has the concept of timestamps. These tell you when a file was created, last modified and so on, and are useful for sorting files and performing change tracking.
Timestamps are also useful for determining which files may have been involved in a particular attack. If an IDS or other system raises an alert at 9:55 and there is a file on the system with a creation time of about the same time, then that file is probably where investigators will start their investigation. Malware authors know this, and they use timestomping as a means of making files’ timestamps blend in with the rest of the system.
In the Master File Table (MFT) on a computer, there are two different sets of four timestamp values. Each set stores the following values for the file:
- Creation time
- Modification time
- MFT time
- Last accessed time
One of these sets is called the Standard Information file attributes, and the other are the File Information attributes. The Standard Information attributes are user-modifiable, but the File Information attributes are designed to only by modified by the OS itself.
Despite this, there is a way to set the File Information Attributes manually. If a file is copied to another folder, its File Information attributes are set to the values of the Standard Information attributes. This allows timestomping with the following steps:
- Manually set the Standard Information attributes
- Copy the file to another folder
- Manually set the Standard Information attributes (some will change during the move)
The end result of this process is a file with timestamps that are set by the attacker. This can help disassociate a file from a malware attack or make a malicious file blend into the System folder (since many OS files have the same timestamp).
Examples of timestomping
On a Windows machine, open C:WindowsSystem32 and sort the contents of the file folder by Date Modified. A large portion of the files will have the same timestamp (the date of your last installation of Windows), and many of the others will be in chunks (as various updates were installed on the machine).
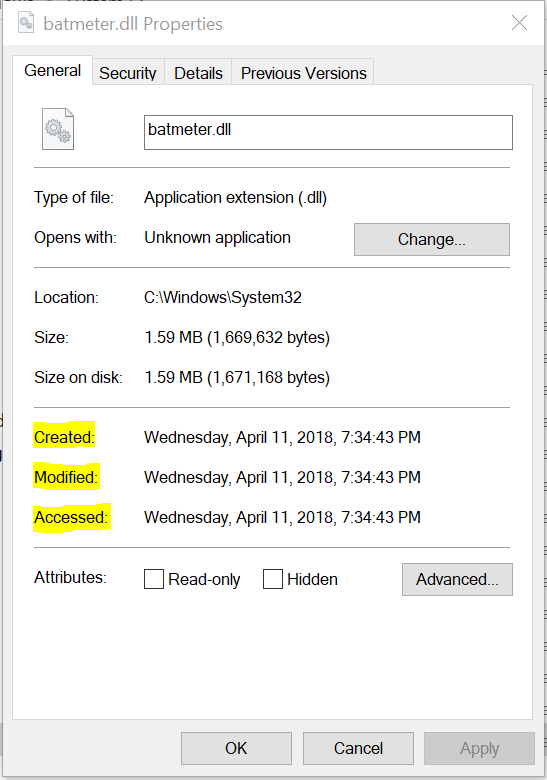
By right-clicking on a file in the folder, you can see one set of timestamps as shown in the image above. While I can’t timestomp the file timestamps with my current permissions level, I can copy the file out of the System directory and modify it elsewhere. This is shown in the PowerShell screenshot below.
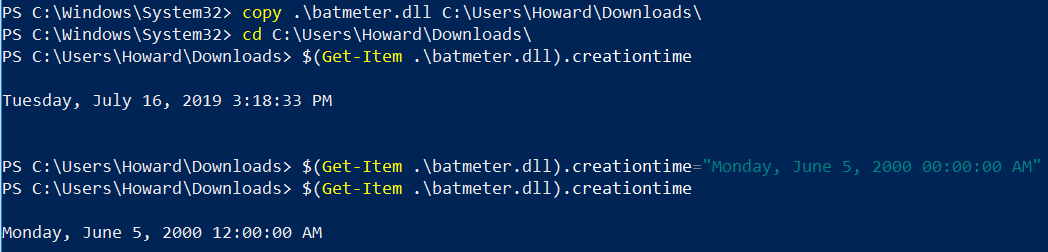
The PowerShell screenshot above shows five different commands involved in timestomping this file:
- Copying to a directory that I can control (Downloads)
- Moving to that directory
- Reading the Creation Timestamp of the file (which matches the copying timestamp of 07/16/2019 03:18 PM)
- Changing the Creation Timestamp of the file
- Reading the Creation Timestamp of the file again
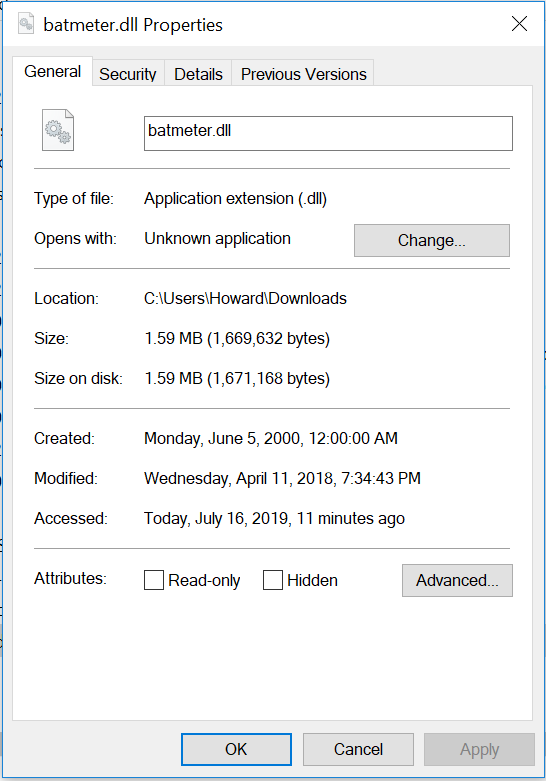
Another screenshot of the file’s properties is shown below.
As shown, the creation time is now from 2000. By modifying the other values (substituting lastaccesstime and lastwritetime for creationtime in the PowerShell command), I can make the file appear to have been untouched since 2000. By copying the file over to another folder, it’s possible to change the File Information attributes as well, making the new file much more difficult to detect.
Detection and mitigation
Timestomping is a difficult technique to detect, since files legitimately change timestamps all of the time. However, a successful timestamping attack requires:
- The ability to edit files in the target directory
- Moving files between directories
- Accessing files
By monitoring the contents of important directories (System32, etc.) and the attributes of the files inside (timestamps and hashes), it is possible to detect if a new file has been added, a file’s timestamps have been modified or a file has been modified. While all of these are legitimate actions, changes in important directories may require further investigation.
For timestomping that is designed to hide a file’s involvement in an attack, monitoring and recording file access requests and file handles may be wise. The file must be created before it can be timestomped. The original file handle can be correlated to the attack, and inconsistencies between file timestamps and previous handles opened to them can be a detection rule for timestomping activity.
Protecting against timestomping attacks
Timestomping attacks are designed to make incident analysis and response more difficult by removing obvious indicators that a particular file is associated with an attack. Timestomping itself is not a real threat to system integrity; however, a successful timestomping attack is capable of slowing down the incident response process, which can impact the scope of the incident and the cost associated with remediating it.
It is often difficult to protect against it (since the ability to update file timestamps is a core part of operating systems), so the best way to protect against this particular attack vector is to implement the monitoring necessary to ensure attempts to hide an attack via timestomping are easily detectable.

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
Sources
- Timestomp, MITRE
- How to edit timestamps with Windows PowerShell, Ghacks