MITRE Shield: An active defense and adversary engagement knowledge base
Introduction
When it comes to collecting tips, tricks and workarounds, it is easy to see quickly that certain concepts and methods are strong against particular setups, while others are weak. As a result, it is an excellent idea to have a large variety of tools available to do you when you are trying to do a specific task — just in case one does not quite do the job and you need to swap out.
Now you could either spend a great deal of time in the wilds of the internet, roaming the tall grasses of forum posts and various hangouts in hopes of catching them all, or you could trade with someone that already has a filled collection. Enter MITRE.
MITRE is best known for their MITRE ATT&CK collection — a wiki of offensive techniques that has proven to be a huge time-saver when trying to perform penetration testing. A sword, you might call it, if you were so inclined. Recently however, they launched the MITRE Shield program, a collection of techniques designed for defensive actions.

Intro to x86 Disassembly
Now some might say that it isn't really necessary, as you could just attack a target enough times to create a solid defense. However, quickly leveling up through best practices may be required if you have to get to a specific threshold quickly for a particular reason. How would we go about doing this? Let’s check out the MITRE Shield program.
First off, we need to head to the MITRE Shield homepage. The primary purpose for Shield is creating a guide to defensive strategies based around known attack methods — planning for what you know is always faster and more effective than planning for what you don't. How do they go about this?
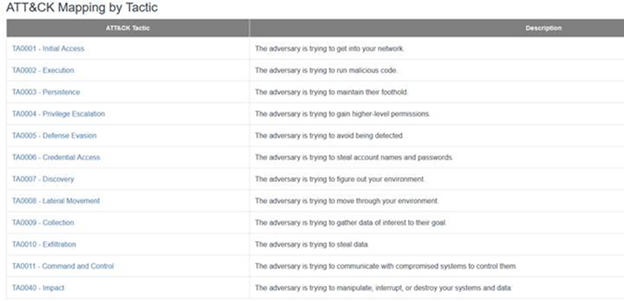
The main tool available for users to access the content of the Shield knowledge base is through the mappings that MITRE has provided between ATT&CK (offensive techniques) and Shield (defensive techniques). This can be accessed here.
Say, for instance, that we had a situation where we suspected that USB sticks were a possible threat to security. Users take a random piece of storage from the parking lot and plug it in when they get back to the desk — a very plausible and very dangerous threat. For this, we would start at the very top of the list with TA0001 - Initial Access: The adversary is trying to get into your network.
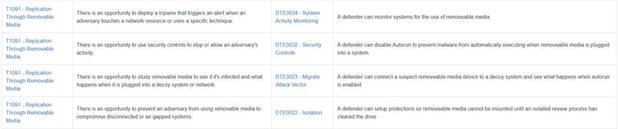
Once we have clicked on this option, we then are shown a list of possible concepts where we can see attack vectors, and potential defensive actions. We can click on one of these on the left to dive into the method further, such as (in our case) T1091 - Replication through Removable Media.
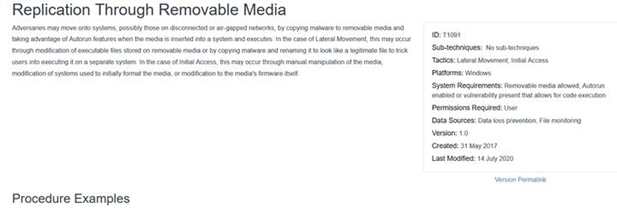
When we are here, we receive a short description of this attack type as well as several possible concepts of how the attack could be performed — this is a portion of the ATT&CK framework that we mentioned previously. After this however, they show specific examples of this form of attack, including pieces of software and historical evidence of groups that may have used the software in the wild.
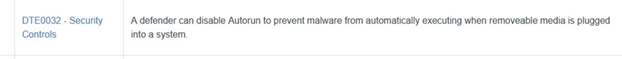
After we review the attack methods, we will want to return to the Mapping to check out possible defensive actions for us to take. We can see that one of the recommendations for this type of possible attack is disabling Autorun — a quick and effective method to continue to have access to storage for the time being, but still block possible malicious attacks from running automatically. However, this may not be the solution all that we need for our environment. We do see, though, that this is a description from DTE0032 - Security Controls.
Once we click on this link, we are brought to a full list of possible defensive measures relating to Security Controls — depending on whether we want to try to encourage an attacker to go in a particular direction via a honeypot, lock down our more sensitive areas from further attacks or both. These lists can help our organizations significantly in starting a conversation about improving our security posture in a particular direction.
MITRE has already said that Shield is a work in progress, and they have a number of modifications that they plan to roll out over the coming months. Given the quality and quantity of information available in the ATT&CK framework, this is clearly going to become a major tool for planning before an issue comes up, along with cleaning up after an issue occurs.

Send a free phishing test — right now!
Conclusion
Whether you are Red- or Blue-Teaming, MITRE Shield can be an asset for figuring out potential weak points in your organization’s structure and help to point out flaws that you may not have even thought about yet. While ATT&CK’s strengths lie in the implementation and testing phases, Shield’s strengths lie in the planning and conceptual stages.
Again, this may change as they add on additional content. But even in this current state, it is tremendously useful.