Simple Mail Transfer Protocol (SMTP) with Wireshark
The Simple Mail Transfer Protocol (SMTP) is one of three protocols used for email. The other two are Post Office Protocol v3 (POP3) and Internet Message Access Protocol (IMAP).
SMTP is one of several internet protocols that are designed to be plaintext and ASCII printable. This means that traffic sent over SMTP is visible and easily readable by eavesdroppers. When running in plaintext mode, SMTP uses port 25. Port 587 is the official port that should be used by SMTP clients submitting traffic to be routed by a mail server.

Intro to x86 Disassembly
However, using traffic that is easily readable by eavesdroppers is not a good idea for email. As a result, SMTP traffic can be encrypted using Transport Layer Security (TLS). The officially accepted way to use TLS with SMTP is to use port 25 and send a STARTTLS message to indicate the beginning of TLS usage. However, port 465 was historically used for encrypted SMTP and some implementations use this.
Whether you use an email server hosted on-premises or a webmail service like Gmail or O365, there is a decent chance that SMTP is being used somewhere behind the scenes. Google and other services maintain SMTP mail servers, allowing users to interact with them programmatically. For example, a Google mail server can be reached by using Telnet to connect to gmail-smtp-in.l.google.com on port 25.
SMTP in Wireshark
SMTP traffic can be filtered in Wireshark using the built-in smtp filter. Alternatively, users can filter for ports commonly used in SMTP traffic (i.e., 25, 587 and 465).
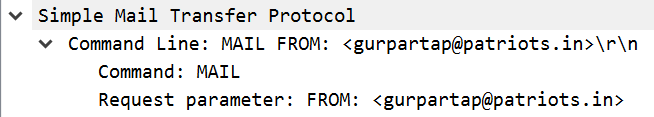
SMTP is a text-based protocol designed to be limited to printable ASCII characters. This is accomplished using a request-response structure. As shown in the image above, an SMTP request consists of a command followed by a set of optional parameters. In this case, the user is setting the sender’s email address.
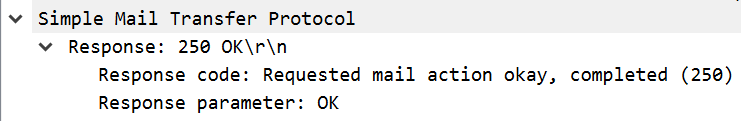
The image above shows a standard SMTP response. This consists of a response code, in this case 250, and optional parameters.
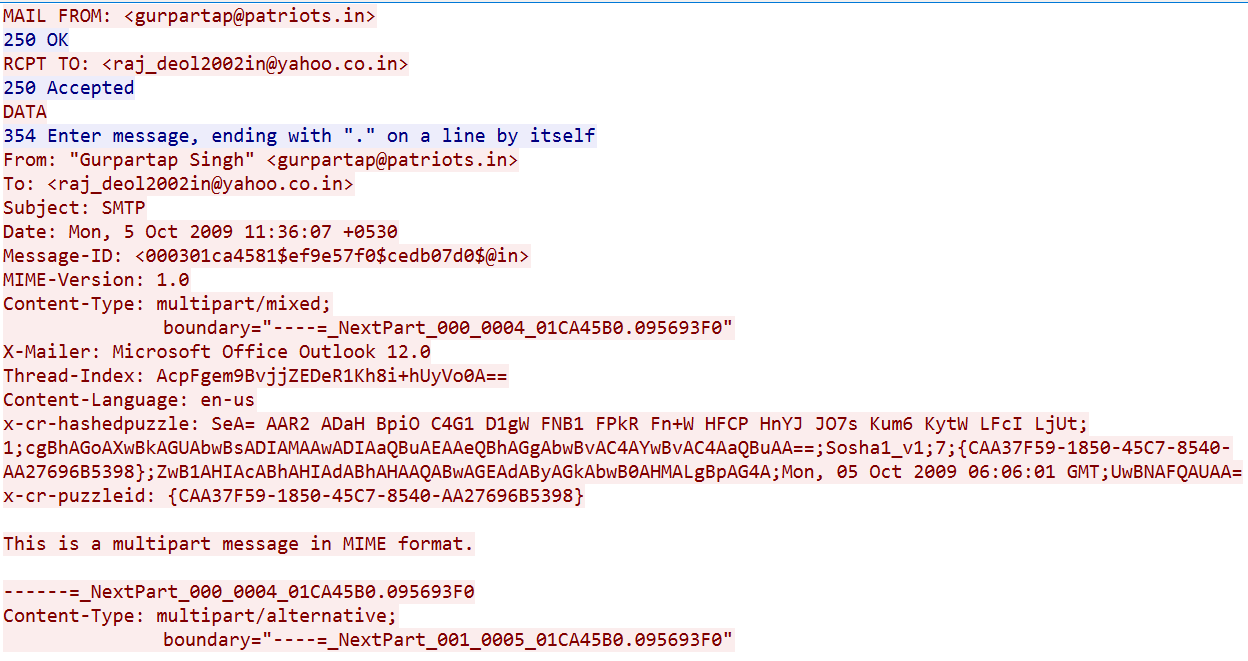
The image above is a sample of SMTP traffic that is collected in Wireshark using the Follow TCP Stream option. It shows the beginning stages of creating an email in SMTP.
As shown, sending emails in SMTP is a drawn-out process. Each field in a standard email requires a separate pair of commands and responses. This sample includes setting the sender’s and recipient’s email addresses and the text of the message.
The image above also demonstrates the risk of using SMTP in plaintext with TLS encryption. This email sample includes two valid email addresses plus any sensitive data included in the text of the email. Before sending the email, the user would also have to authenticate to the server, which can leak credentials in plaintext.
Since SMTP can be used programmatically by connecting to an SMTP server on port 25, it is possible to write programs or scripts that send emails. If these programs do not use TLS, they can leak sensitive information. Monitoring for insecure use of SMTP can be useful from an ethical hacking or network defense perspective.
SMTP analysis for incident response
As an email protocol, SMTP can be used for a few different malicious purposes. An obvious application of email is for phishing and spam email campaigns; however, the SMTP protocol can also be abused by an attacker as part of reconnaissance during preparations for an attack.
Credential extraction
SMTP is designed as a plaintext protocol. All of the information included in an SMTP packet must be printable ASCII characters. However, SMTP also includes the ability to force users to authenticate to the protocol. This means that user credentials are included in a plaintext protocol.
However, the user credentials in an SMTP session are not sent in plaintext. As shown in the image above, credentials are Base64-encoded before being sent over the network. However, Base64 is trivially reversible, making it easy for an eavesdropper to steal user credentials.
Protecting against compromise of user credentials requires using TLS to encrypt SMTP traffic. It is also wise to monitor for the use of unencrypted SMTP and force password changes for any leaked credentials.
Phishing and spam
As an email protocol, the most famous way that SMTP is misused is in spam and phishing emails. If an attacker can compromise an organization’s mail server, then it may be used to send spam email. This access can also be used to send phishing emails from the compromised user’s account. Since the emails originate from within the organization and are from a known email address, they are more likely to be trusted by their recipient.
Email is also used by some types of malware worms to spread itself. While mass-mailer worms have become less common, some are still active in the wild. In 2019, the MyDoom email worm was still running on autopilot 15 years after being launched. Many webmail providers, like Gmail, scan for and block mailer worms, but monitoring for indications of spam in the network is a good idea.
Reconnaissance
Knowledge of someone’s email address can be very valuable to a cybercriminal. With an email address, it’s possible to send someone spam or phishing emails or use credential stuffing to try to guess their password on online services.
SMTP has a few different built-in functions that can help an attacker gain useful information about valid email accounts associated with a mail server. By using Telnet to connect to an SMTP server on port 25 and sending the VRFY command, an attacker can check the validity of a specific email address. Scripting this to run automatically allows account enumeration. Alternatively, use of the EXPN command can help to determine if a specific mailing list exists on a server. Monitoring for use of these commands on an SMTP server can help to detect these enumeration actions.
Monitoring SMTP traffic in Wireshark
SMTP traffic is used for legitimate email but can also be employed for malicious purposes. Monitoring for a large volume of traffic from a single host is a good idea, since it may indicate that the computer has been compromised and is being used as a spambot. However, SMTP can also be used for reconnaissance and intelligence collection. In Wireshark, monitor for unencrypted SMTP and the presence of commands that can be used to collect data about user accounts.

Learn Network Forensics
Sources
- Simple Mail Transfer Protocol (SMTP), Wireshark
- Which SMTP Port Should I Use? Understanding Ports 25, 465, & 587, Mailgun
- SMTP Hacks and How to Guard Against Them, Dummies
- Notorious MyDoom Worm Still on AutoPilot After 15 Years, Bleeping Computer