Network traffic analysis for IR: Network mapping for incident response
Introduction to network mapping
The concept of network mapping is not a new one. Creating network maps in the design phase of a network and updating them throughout its life cycle is a crucial component of network architecture and cybersecurity. Understanding the potential connection paths through the network is necessary for debugging issues in the network and implementing network segmentation (which is necessary for compliance with many certifications, regulations and standards).
While the entire network map is useful for understanding the overall structure of the network, network mapping can also be useful for incident response. Humans tend to process information much better as visualizations rather than lists of data. It is much easier to understand traffic flows throughout the network in a diagram rather than a list of connection flows.
Learn Network Forensics
Network maps are useful for more than describing the network architecture for planning, upgrades and security reviews. A partial network map describing the communications flow between certain machines of interest can be invaluable during an incident response investigation, and a high-level visual representation of an incident can be an extremely useful tool.
Simple network visualization with PcapViz
There are several different tools available for network visualization, but an easy-to-use, no-frills one is PcapViz, which is available on GitHub. The tool is implemented as a Python script that can be run from the command line and uses graphviz to produce simple visualizations of network flows. It can process data in the packet capture file format used by tools like Wireshark (.pcap or .cap).
PcapViz will generate mappings at layers 2 (Data Link), 3 (Network) and 4 (Transport) of the OSI model. The syntax is simple. A request to generate a Layer 3 mapping is:
python <path to PcapViz directory>/main.py --layer3 -i infile.pcap -o mapping.png
The network maps in this section are generated based on a traffic sample from Malware-Traffic-Analysis.net.
Layer 2/3
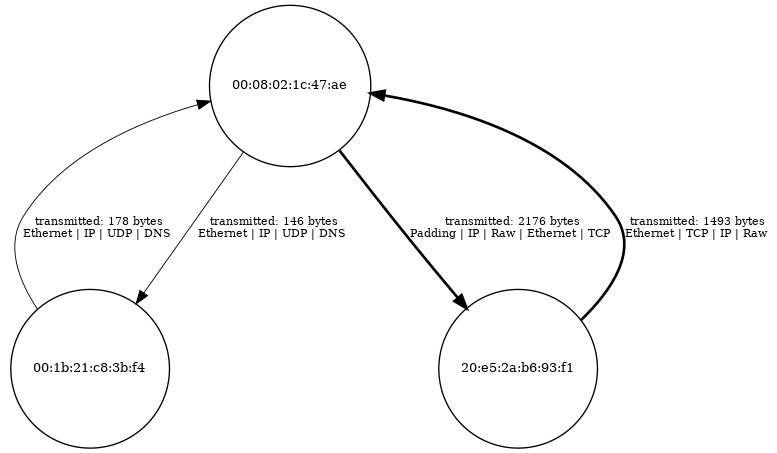
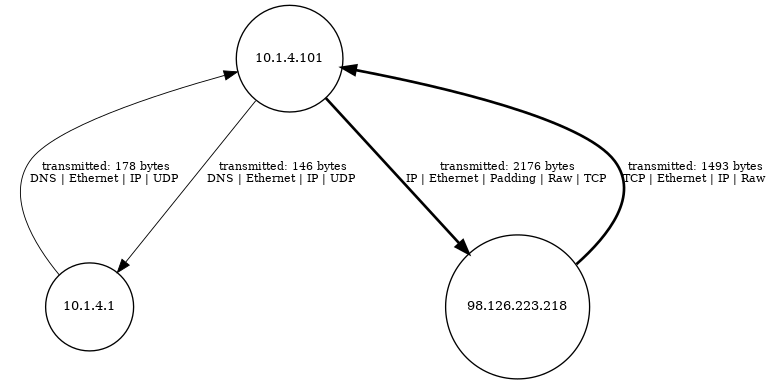
While PcapViz offers generation of Layer 2 and Layer 3 network maps separately, they often display the same overall structure. Layer 2 is the Data Link layer and identifies computers based on their hardware address (MAC address), while the Network layer (Level 3) uses IP addresses for identification. Differences between the network maps would arise if there is not a one-to-one matching of MAC addresses and IP addresses.
The images above show Layer 2 (left) and Layer 3 (right) network maps, as generated by PcapViz. As shown, the primary difference between the images is that the left image identifies machines by MAC address while the right one uses IP address.
Network maps at this level are useful for identification of anomalous connection paths within a network or understanding the communication paths between different computers involved in an incident. The images identify the computers that are communicating with one another, the protocols used, and the volume of data sent.
Based on this diagram, it appears that the IP address 10.1.4.101 made a DNS request to 10.1.4.1 and also communicated heavily with 98.126.223.218. It is possible (but not certain) that the DNS request made of 10.1.4.1 resolved to the 98.126.223.218 IP address.
Layer 4
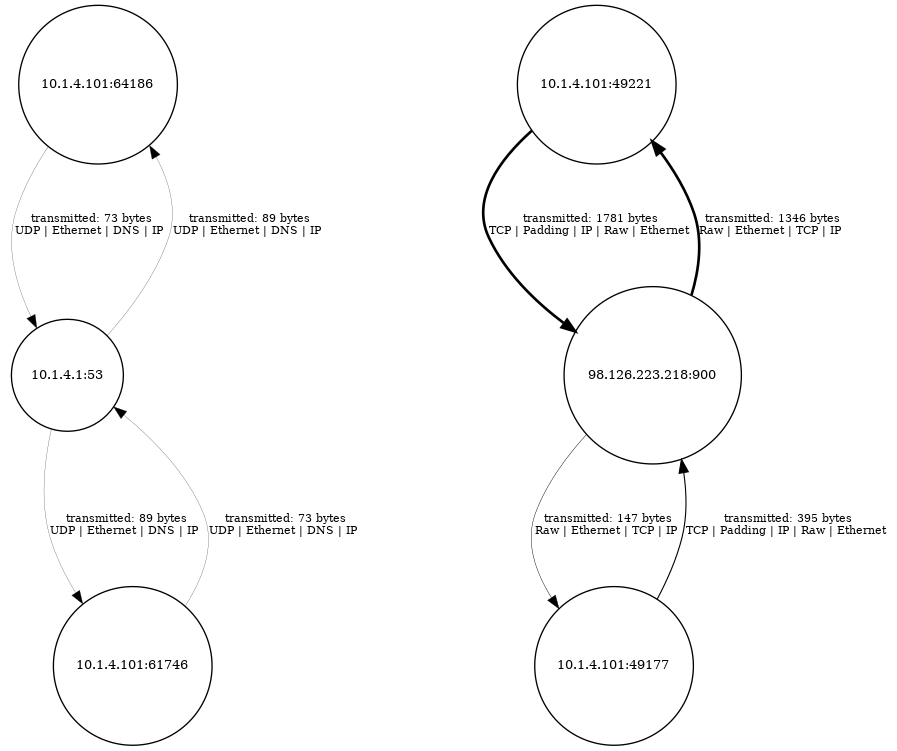
Layer 4 of the OSI model is where protocols like TCP and UDP come in. These protocols define the concept of ports and deal with the fact that a single machine can have multiple simultaneous outstanding connections.
A network map generated at Layer 4 of the OSI model shows information about the communications being performed at the port level. This map is less useful for understanding the overall landscape of communication flows within the network, since the same machine may appear multiple times within the diagram. However, it can be invaluable for extracting details about the particular applications that are communicating on the network.
For example, the left half of the map shows that 10.1.4.1 is a DNS server (based off of the fact that it’s operating on port 53). The right half of the map demonstrates that a machine is communicating on two different ports with 98.126.223.218 on port 900. Since 900 is not a standard port for a server, this may indicate a command-and-control server for malware. The affected machines should be investigated for possible infection, and the organization may wish to add the domain that is requested and resolves to 98.126.223.218 to a DNS blacklist.
Conclusion: Network mapping for IR
Network maps can be used to provide an approachable summary of the operations of a network or some subset of it. If an incident responder believes that a particular machine is acting oddly, it may be valuable to collect a traffic capture of all communications flowing to/from that machine and throwing it into a network mapper. The results make it easy to quickly achieve a high-level understanding of the communications being performed by the computer of interest and determine if further investigation is warranted.
Alternatively, a network map of the machines known to be associated with an incident under investigation can be helpful for planning investigative activities. The diagrams generated by PcapViz are easy to generate and assimilate and provide hints regarding the functions of various machines within an incident.
While a network map only provides high-level data (and the conclusions drawn from it can be incorrect), it can be a valuable tool for incident response due to the fact that it aids rapid processing of network data by an analyst. The massive amount of information that an analyst must process when performing triage of an alert or more in-depth investigation increases cognitive load and decreases efficiency. Employing network maps as an initial step during triage or investigation can help make incident response operations more efficient and effective.

Get your free course catalog
Sources
- PcapViz, GitHub
- What Is The OSI Model?, Cloudflare
- 2018-01-04 - MALSPAM PUSHING PCRAT/GH0ST, malware-traffic-analysis.net