2020 NIST ransomware recovery guide: What you need to know
Introduction
Over the past decade, a destructive piece of malware has grown from a novel concept into a digital epidemic. Now ransomware is causing a serious impact on organizations’ assets. This malware type is growing in popularity amongst attackers as a way to quickly extort money from its victims, which may include individuals, organizations and even governments.
In order to respond to this threat, the National Cybersecurity Center of Excellence (NCCoE) at the National Institute of Standards and Technology (NIST) introduced a project to help organizations to detect and respond effectively to data integrity attacks across multiple industries. This project includes a wide range of design rules and technologies to develop a best fit solution that can help the market fight this emergent threat.

Learn ICS/SCADA Security Fundamentals
According to the NCCoE, “ransomware, destructive malware, insider threats, and even honest mistakes present an ongoing threat to an organization’s infrastructure. Database records and structure, system files, configurations, user files, application code, and customer data are all at risk should an attack occur.”
Nowadays it is crucial to implement detection and response mechanisms that can prevent many types of data integrity attacks. Some of these risks can be reduced by using a group of capabilities, such as integrity monitoring, event detection, vulnerability management, reporting capabilities and mitigation and containment.
Risks and impact of a data integrity attack
The risk associated with destructive malware, ransomware or even any human mistakes related to valuable data is the reason why organizations need to quickly detect and respond to a data integrity event. There is not a single magic formula, but the basic advice is quite simple: detect fast and respond appropriately to each challenge.
A data integrity attack may target the following:
- Stored and sensitive information (PII)
- Emails
- Customers data/information
- Employee records
- Financial records
- Backups
- Reputation
For example, if a system is partially destroyed via a data integrity attack (e.g., ransomware), and the organization’s backups are also affected, this puts the organization in a bad place, impacting business operations, revenue and its reputation in the market.
One particularly destructive scenario is a ransomware attack targeting a healthcare organization. In this case, patient data integrity could be affected, impacting not only the organization but also the patients and their clinical data. Since some health entities still use old or out-of-date systems, the traditional recovery systems via data restoration might not be a trivial process. Notice that these types of attacks affect the daily operation of an organization.
In brief, a data integrity attack may include:
- Adding unauthorized or arbitrary data to an asset (e.g., database, specific operating system program, shared folders in the organization’s network, etc.)
- Deleting data
- Modifying data (e.g., corporate information, emails, employee records and financial data)
These types of attacks can be launched via ransomware attacks or simply by executing single and targeted attacks with the goal of changing some targeted data.
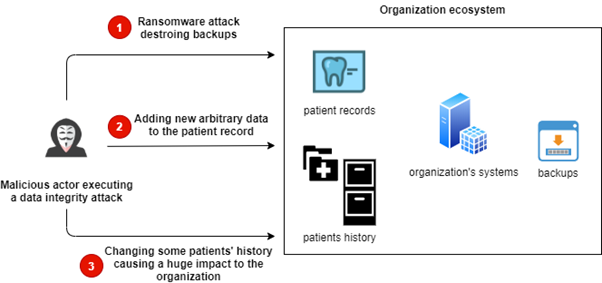
The illustration below demonstrates a scenario where three types of attacks can be performed against the same organization.
As depicted in the illustration:
- A ransomware attack can be executed, destroying some target systems or assets. This kind of attack often targets backup systems to avoid data restoration and to take advantage of ransom schemes in which the victim can get back its data by paying some money
- A malicious actor gets access to a valuable asset, allowing them to add arbitrary data and thus damaging or compromising sensitive information. This can be a challenging scenario to recover if detected in a later stage
- A malicious actor can change a patient’s history, thus compromising the organization, the patient data and diagnostics and further medical treatments
According to NCCoE, the most common types of vulnerabilities to consider in relation to these threats include:
- Zero-day vulnerabilities
- Vulnerabilities due to outdated or unpatched systems
- Custom software vulnerabilities/errors
- Social engineering and user-driven events
- Poor access control
Proposed architecture to fight data integrity attacks
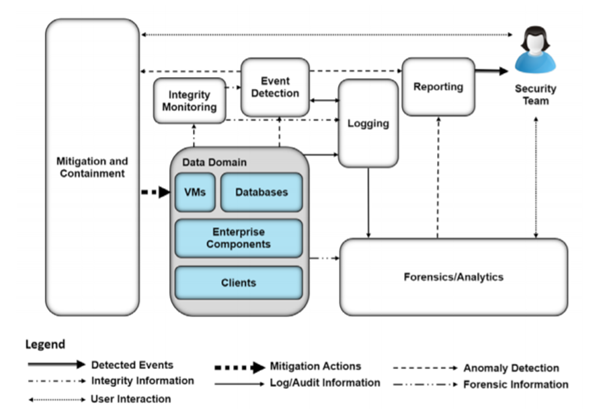
The NCCoE created a solution with different and existing technologies that provided the following capabilities:
- Event detection
- Forensics/analysis
- Integrity monitoring
- Logging
- Mitigation and containment
- Reporting
The data integrity solution is designed to address a wide range of functions and categories (see table 3-1 in the official draft). The architecture diagram is presented below.
In brief, this solution provides:
- Integrity monitoring: Comparing current system states with established baselines
- Event detection: Detection of real-time activities, providing mechanisms such as intrusion detection, malware detection, user anomaly detection and others, depending on the established threat model initially designed for the organization
- Logging: All the events and log files are recorded
- Forensics/analytics: Providing the ability to probe/analyze logs and machines to get knowledge based on the occurred data integrity events
- Mitigation and containment: Allow responding to data integrity events by containing and limiting the threat’s ability to affect the system
- Reporting: Providing the capability to report on all activities
Benefits of the NCCoE guide
Organizations must be equipped with tools to fight the current emerging threats within this field. With that in place, the NCCoE’s practice guide can help organizations to:
- Develop a well-designed strategy to detect and respond effectively to data integrity attacks
- Build an effective detection and response routine to facilitate handling these events, maintain operations and ensure the integrity and availability of data to support business operations and revenue-generating activities
- Defining and managing enterprise risk based on the NIST Framework for Improving Critical Infrastructure Cybersecurity
Final thoughts
With emergent threats growing, the process of creating mechanisms, routines and strategies to fight this challenge, as well as speedy implementation by organizations, should be one of the first priorities of this era.
This project focuses on detailed methods and potential tool sets that can detect, mitigate and contain data integrity attacks on an enterprise network. In addition, It also identifies tools and strategies to aid in a security team’s response to such an event. The scope of the project should hopefully answer specific questions concerning detecting and responding to data integrity events.

Learn Python for Cybersecurity