The Healthcare IT Stack
Any technological system depends on its design for its reliability and availability. The way the different layers of IT get set up and how they are meant to communicate with each other defines how well a system will perform; it also signifies how hard it will be for intruders to penetrate the system. In the healthcare department of the US, in general, the IT stack isn’t made as sophisticated as it should be. This not only means that there will be performance issues but it also makes the system inherently vulnerable to intrusion; only in 2015, 112 million healthcare records were compromised.
Data in a healthcare system travels through a layered architecture. It makes its way from the monitor screen of the administrator and into the database after passing through the network. During this journey, there are many possible points-of-attack that a hacker can look at and in this article we intend to discuss all of them. For starters, let’s list the layer demarcations that can be seen in a typical system:
Implementing HIPAA Controls
- Application layer: This is the layer that is presented to the user, who can be either the administrator or the patient. For the patient, the application layer will present a portal from where they can view pertinent information; for the administrator, the application layer can present another level of options. We will talk more about this in a while.
- Data integrity layer: This layer lies between the application and the network layer and is responsible for ensuring data integrity and proper session maintenance. In layman terms, since at any given moment there can be multiple users connected to the same portal, there is a need to keep the data of every user concrete and separate.
- Network layer: This layer exists beneath the data integrity layer and is responsible for transporting data safely to the layers underneath. The majority of IT systems use data encryption techniques at either the network or the data integrity layer.
- Utilities layer: This layer is not necessarily a part of the IT stack but is still connected to it. It’s comprised of the various devices that are on the same network and can be fed the data retrieved from either the database or the application layer. Examples of devices on this layer are printers, helpdesk information monitors, etc.
- Database/backend layer: This is the most important layer in any IT stack, regardless of the industry we are talking about. All the data gets stored in the database (or the cloud) after passing through the various layers mentioned above. The ultimate objective of any hacker is to get access to the database and normally, to do so, they exploit the vulnerabilities present in the aforementioned layers.
- DevOps layer: This layer is once again not necessarily a part of the IT stack but is in direct relation with it. It is comprised of the developers and the IT professionals that deal with the overall system and are responsible for maintaining its security, availability and performance.
Now that we have introduced the layers briefly, let’s discuss how they can be potential points of attack and how hackers have been continuously compromising healthcare systems through them:
The Application Layer
- For the patient/end-user: The application layer is normally presented in the form of a web portal or a smartphone application to the users. Traditionally, they present users with information regarding time tables, the availability of doctors, etc. Because these applications are normally available to the general public, a hacker won’t have a hard time getting access to one. Take for example, a website, which is just a few clicks away from getting viewed by a potential intruder. In the recent years, web portals have been used heavily by hackers to gain access to the system. This is because not many healthcare developers are aware of the potential attacks that can take place on a website that doesn’t comply with the infrastructural security standards of the modern IT dogma. In 2014, the healthcare.gov insurance website got compromised and there have been many more such instances since then.
- For the administrators: The application layer is presented to the administrators normally in the same way as the end-user but often with many additional features. A bad practice is to use the same applications (web based and smartphone based) for the administrators as the users, unless remarkably rigorous security is in place. Once the hackers get access to administrative privileges (via using different hacking methodologies), they can manipulate the system to their discretion. Another possible security breach at this layer can be caused by misuse of privilege. This would involve a person, entrusted with access to sensitive material, looking where they shouldn’t be. A report compiled by Verizon on how healthcare breaches occur indicates that around 20 percent of the total data breaches occur via privilege misuse.
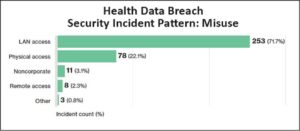
Image courtesy: Calyptix security
- Suggestions- In order to make the application layer more secure, the following suggestions can be considered:
- Upgrade your application scripts periodically. Outdated web scripts can significantly add vulnerabilities to the system.
- Host the administrative portal on a local IP address that can only be accessed via the company VPN.
- Keep a very strong administrative password.
- Run vulnerability tests on your web portals to ensure that they are safe enough.
The Data Integrity Layer:
The data integrity layer is responsible for ensuring that data stays concrete as it makes its way to the end of its journey. Session maintenance is performed at this layer which ensures that every user’s session is maintained separately. If proper maintenance for running sessions isn’t provided, it can be seen as a potential point of attack. Additionally, at this layer, data encryption techniques have to be employed to ensure that upon transmission, even if data gets intercepted, it isn’t decipherable. Again, many healthcare systems don’t use sophisticated encryption techniques which make hacks like a man-in-the-middle attack a viable one.
Suggestions:
- Use the latest version of Kerberos to secure your IT infrastructure.
- Change your encryption keys as often as possible.
- Don’t provide unauthenticated access to the main organizational network.
The Network Layer
If and when a hacker intrudes a network, it’s not long before they get complete control of everything. Getting into a network is a lot easier than it seems; hackers normally employ social engineering tricks if simple script-running doesn’t give them access. Even though most hospitals nowadays have password-protected Wi-Fi connections, breaking the passwords for these connections is as simple as running a command on a terminal for experienced hackers. Last year, the network of University of California, Los Angeles got intruded and resulted in 4.5 million victims.
Suggestions:
- Make use of hidden Wi-Fi networks.
- If you absolutely have to, then make a guest connection that’s available to anybody that visits but doesn’t have anything connected to it.
- Don’t connect the database with the main network; rather, tunnel the traffic via a proxy.
- Only provide the main network access to trusted people who are routinely monitored.
The Utilities Layer
As already mentioned, this layer isn’t necessarily a part of the IT stack but because it consists of devices that are actually connected to the network, it has to be considered. The printers, the fax machines and the helpdesk information monitors normally have to be in communication with the database and the hospital network in general to be able to function. A lot of hackers have identified this layer as a great point of attack because not many people think that it would be causing any vulnerabilities (Wrong!).
The US Food and Drug Administration issued cybersecurity recommendations earlier this year in which they highlighted the security guidelines that need to be abided by all the medical devices that are used in the healthcare industry. Norse, a state-of-the-art security intelligence company, in association with SANS, released a report that contained results worth mentioning. They highlighted that among other things, a hacker can add routing to a printer that is connected to the network (remotely) which will allow them to receive any documents sent to the said printer. They can also upload their hacking tools on the device and try to take control of the whole network via the printer as well.
Suggestions:
- Make sure that all the devices connected to the network pass the security tests.
- Try to add some authentication on the devices to ensure that a hacker can’t intrude and gain access.
- Make the devices physically inaccessible for everybody except administrators.
- Log the actions performed by the device and monitor the logs periodically.
The DB/Backend Layer
This is the most important layer in the complete system as it’s responsible for holding the actual data (and is the ultimate destination for it). It’s every hacker’s dream to have access to the database but most of the time, they have to breach the layers present above to gain access to it. When your whole database gets compromised, you are left with nothing but regret because you didn’t maintain your security well enough and hopelessness if you didn’t have well-maintained backups.
In order to protect the backend (the cloud or the DB) from hacking, you are normally obliged to make the layers present above secure enough. There is DB level security implemented in sophisticated systems but at the end of the day, when you query a database, it will return you whatever you want. As already mentioned, misuse of privileges can also lead to a database getting compromised but apart from that, there have been many instances where hackers made their way to the database one way or the other. A few months back, around 9.3 million records were sold on TheRealDeal market by a user named thedarkoverlord (trdealmgn4uvm42g.onion/profile/32184) after the hacker got access to all the records of a healthcare database.
Suggestions:
- Only provide database access to IT administrators and monitor their activities.
- Ensure that the layers above the database are concretely safe from intrusion.
- Implement database-level security to further strengthen the overall integrity of the system.
The DevOps Layer
This layer is worth talking about because it consists of people that are in direct connection with the overall system. The developers and the IT professionals that monitor the whole system can also become possible points of attack. The Verizon report highlights that around 45 percent of the total hacks are caused by the loss of assets (USBs, laptops, etc.) that contain data relating to the system and many times, the pertinent data isn’t encrypted. Apart from this, as already talked about, if a person performs a misuse of privilege then it will be a DevOps layer vulnerability too.
Suggestions:
- Hire experienced developers that have proven track records.
- Keep the data on important devices such as USBs and laptops encrypted.
- Perform continuous monitoring of people that have unprecedented access to the system.
Final Thoughts
No matter how hard we try, we can’t make a network or a system “categorically free of vulnerabilities.” Still, if proper precautions and steps are taken, we can prevent hackers from making healthcare systems an easy target. We tried to cover the major points of attack in a healthcare IT system and also presented suggestions to improve the levels of security; hopefully, healthcare organizations will realize these issues and allocate spending wherever necessary.
Implementing HIPAA Controls






