Blockchain and hash functions
Hash functions are cryptographic algorithms designed to protect the integrity of data. Hash functions have a few useful properties, including:
- One-way: Hash functions are one-way functions, meaning that it is possible to calculate a hash output from an input, but it is infeasible to reverse the calculation to derive an input from an output.
- Collision-resistant: Collision resistance means that it is difficult to find two inputs that produce the same output. This applies both to finding two matching inputs or finding an input that produces a certain output.

Get your free course catalog
Hash functions in blockchain
Hash functions are used in a variety of different applications. The integrity protection of a hash function is used in blockchain to create the chains that link blocks together and in the Proof of Work consensus algorithm.
The blocks’ chains
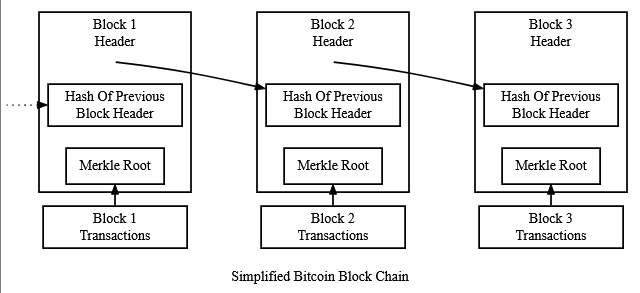
Blockchain’s name comes from the fact that it is created from blocks chained together. The chains that link the blockchain’s blocks together.
The chains in blockchain are implemented as hash functions. Each block in the blockchain contains the hash of the previous block’s header within its own header as shown above.
By incorporating a previous block hash into each block, the blockchain makes it harder to forge blocks in the digital ledger. Changing the contents of one block changes the value of its header. This would change the hash of that header, which changes the value of the next block’s header (and so on).
By making it necessary to change all following blocks to change a block, hash functions increase the security of the blockchain’s digital ledger. Creating a block is supposed to be relatively easy, but creating many is much more difficult. This makes building a blockchain easy but rewriting it difficult.
Proof of Work consensus
Control over the block creation process also grants a level of control over the contents of the blockchain. Blockchain uses consensus algorithms to decentralize control of the block creation process.
Consensus algorithms are designed to make control over the blockchain proportional to control over a scarce resource. In Proof of Work, the scarce resource is computational power.
Creating a block in a Proof of Work requires a miner to find a version of their block with a header value less than a certain threshold. They accomplish this by modifying a nonce value within the block header.
Since hash functions are unpredictable, the best way to find a valid version of a block is via a brute force search (i.e. guess and check). Since the more computational power a node has the more guesses it can make, control over computational power increases control over the blockchain.

Learn Web Server Protection
Conclusion
The blockchain is designed to be a decentralized system that maintains an immutable digital ledger. Without a centralized authority, there is no one to enforce the rules and maintain the integrity of the digital ledger. Hash functions and other algorithms make it possible to enforce the rules of the blockchain without an enforcement authority.
Sources