Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Infosec Skills author Vladimir de Turckheim explains the importance of hands-on Node.js security experience

Infosec Skills author Matthew Campagnola is forging a new path in ICS security

BAHAMUT: Uncovering a massive hack-for-hire cyberespionage group

Ask us anything about developing security talent and teams (session #2)
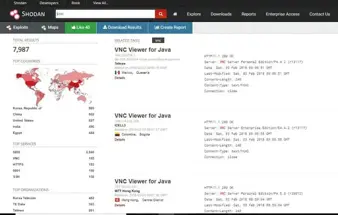
Top five open source intelligence (OSINT) tools [updated 2021]

Ask us anything about security awareness, behavior & culture (session #2)
RansomExx: The malware that attacks Linux OS

Protocol analysis using Wireshark

Wireless analysis

How to use Microsoft DirectAccess

Influencing security mindsets to build a culture of cybersecurity

How to protect a Windows 10 host against malware

Gamification — Cybersecurity’s turn to play

Log analysis

Network security tools (and their role in forensic investigations)

Developing security talent and teams: A roundtable discussion

Sources of network forensic evidence

Linux security and APTs: Identifying threats and reducing risk

Unpatched address bar spoofing vulnerability impacts major mobile browsers

Network Security Technologies

Infosec Skills author teaches people-process-technology approach for "secure software development"

Infosec Skills author Joseph South found "love at first sight" in cybersecurity
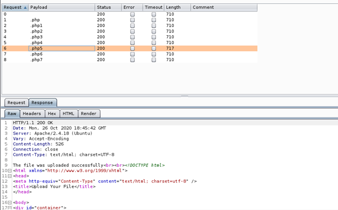
Hack the Box (HTB) machine walkthrough series: Vault

Flip the funnel: Fixing the cybersecurity talent pipeline challenge