Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Methods for attacking full disk encryption

Introduction to Public Key Infrastructure (PKI)

Infosec Skills Author Jason Welsh shares his passion for Linux and Cybersecurity
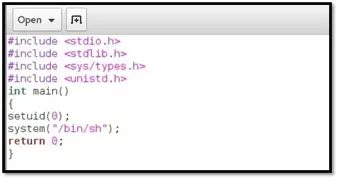
Exploiting NFS share [updated 2021]

CGEIT certification exam: overview of domains [Updated 2021]
Presidential: 1 CTF walkthrough part 1

Application sideloading in Windows 10

Phishing with Google Forms, Firebase and Docs: Detection and prevention

Web Browser Security in Windows 10

Microsoft’s Project OneFuzz Framework with Azure: Overview and concerns
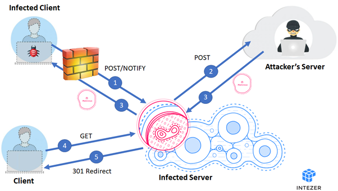
Stantinko Trojan: What it is, how it works and how to prevent it | Malware spotlight

How to control the flow of a program in x86 assembly

Top 25 vulnerabilities exploited by Chinese nation-state hackers (NSA advisory)

Mitigating MFA bypass attacks: 5 tips for developers

5 benefits of paying for an employee's professional certification

How to diagnose and locate segmentation faults in x86 assembly

How to use the ObjDump tool with x86

Deception technologies: 4 tools to help you identify threats and mitigate risks

Debugging your first x86 program

6 key elements of a threat model

Best cyber ranges for cybersecurity professionals and teams

How to build a program and execute an application entirely built in x86 assembly

Overview of common x86 instructions

Top threat modeling frameworks: STRIDE, OWASP Top 10, MITRE ATT&CK framework and more