Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Types of cyber ranges compared: Simulations, overlays, emulations and hybrids

x86 basics: Data representation, memory and information storage

Cybersecurity Weekly: Cisco VPN flaws, Chrome zero-day fix, new DDoS botnet

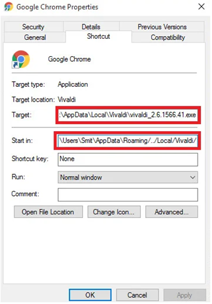
How to attack Windows 10 machine with metasploit on Kali Linux [updated 2021]

What is x86 assembly?

Introduction to x86 assembly and syntax
National Initiative for Cybersecurity Education (NICE) cyber range checklist
Vizom malware: What it is, how it works and how to prevent it | Malware spotlight

Nmap from beginner to advanced [updated 2021]

Using MITRE ATT&CK with cyber threat intelligence

Top 30 Microsoft Azure interview questions and answers

MITRE ATT&CK framework mitigations: An overview

Hack the Box (HTB) machines walkthrough series — Unbalanced

MITRE ATT&CK framework techniques, sub-techniques & procedures

Top 9 cybercrime tactics, techniques and trends in 2020: A recap

How to use Local Group Policy to secure Windows 10

KashmirBlack botnet targets WordPress, Joomla and other popular CMS platforms
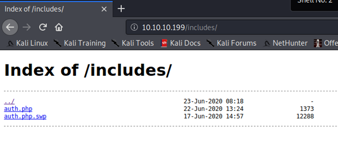
Hack the Box (HTB) machines walkthrough series — OpenKeyS

Introduction to the TLS/SSL cryptography protocol

Introduction to Diffie-Hellman Key Exchange

Exploiting built-in network protocols for DDoS attacks

Introduction to the Rivest-Shamir-Adleman (RSA) encryption algorithm

CloudGoat walkthrough series: EC2 server-side request forgery (SSRF)

Firewall types and architecture