Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Capture the flag: A walkthrough of SunCSR’s Seppuku
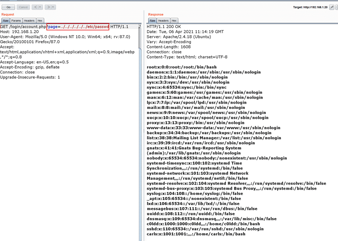
Colddworld immersion: VulnHub CTF walkthrough

How to become a CMMC Certified Third-Party Assessor Organization (C3PAO)

Kali Linux: Top 5 tools for sniffing and spoofing

How to design the best cybersecurity training program for your enterprise

How to become a CMMC Registered Provider Organization (RPO)

CMMC marketplace: Understanding C3PAOs, RPOs, LTPs and more

Snort demo: Finding SolarWinds Sunburst indicators of compromise

Top 19 tools for hardware hacking with Kali Linux

Kali Linux: Top 5 tools for penetration testing reporting
MoneyBox 1: VulnHub CTF walkthrough
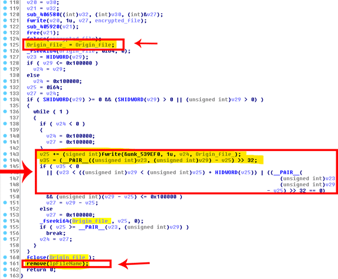
DearCry ransomware: How it works and how to prevent it

Cybersecurity Weekly: Ransomware affiliates, Cisco ASA flaws, Dell vulnerabilities

How to become a Certified CMMC Assessor (CCA)

Kali Linux overview: 14 uses for digital forensics and pentesting

Memory forensics demo: SolarWinds breach and Sunburst malware
Clover 1: VulnHub CTF walkthrough, part 1

Explore Python for MITRE ATT&CK persistence

How to become a Certified CMMC Professional (CCP)
GANANA: 1 VulnHub CTF walkthrough part 2

9 best practices for network security

Two ways to build a secure software team using the NICE Framework
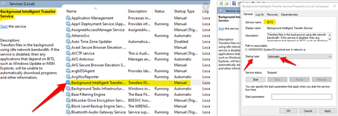
How criminals are using Windows Background Intelligent Transfer Service

Explore Python for MITRE ATT&CK defense evasion