Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
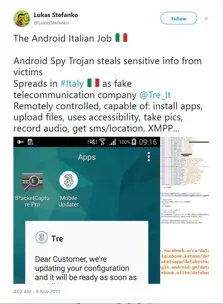
Powerful Skygofree Spyware Was Already Reported and Analyzed In 2017
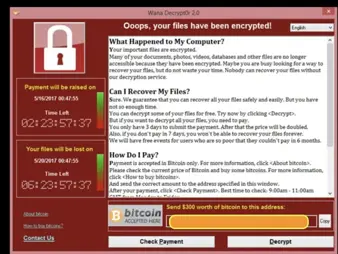
The Five Largest Ransomware Attacks of 2017

A Step-by-Step Guide to Data Security Compliance by Industry

Security Risk Management Considerations for Small & Medium-Sized Business

A cyber insurance policy checklist
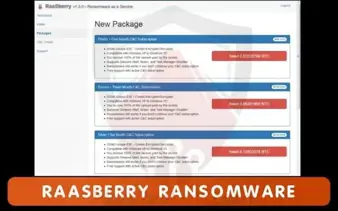
Malware in dark web

SQL Injection Protection in Cloud Systems

How to Select & Implement Effective Risk Management Standards & Frameworks

Security+: Types of Mitigation and Deterrent Techniques (SY0-401) [DECOMMISSIONED ARTICLE]

Security+: PKI, Certificate Management, and Associated Components (SY0-401) [DECOMMISSIONED ARTICLE]

10 Questions You Should Ask Vendors About Their Risk Management Program
How Security Awareness Training Can Protect Law Enforcement
How to Assess & Manage Third-Party Vendor Security Risks

Understanding the Link Between Business, Operational & Security Risks

5 best password auditing tools

5 Steps to Create a Security Culture within your Organization

Top 10 Threats to Healthcare Security

A Look at Data Security Compliance & Regulations by Industry

10 Ways GDPR Will Affect Data Collection and Use

How Cyber Insurance Can Safeguard Your Business - A General Guide
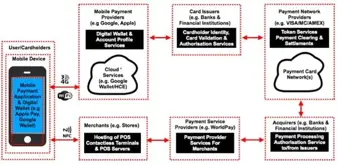
An Examination of the Security Threats Posed to a Mobile Wallet Infrastructure
An Overview of the Mobile Wallet and Apple Pay

Computer Forensics: Overview of Software Forensics

Certified Wireless Security Specialist (CWSS) Salary