Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Tabnabbing

Pentester Academy Command Injection ISO: SugarCRM 6.3.1 Exploitation

Virtual Machine Introspection in Malware Analysis

USV: 2017 Part 2 CTF Walkthrough

Interview With an Expert: How Does a CISO Learn to Be a CISO?

Vulnhub machines walkthrough series — PwnLab-Init

Important SQLMap commands

QRL jacking

Threat Hunting Methodologies

Threat hunting: IOCs and artifacts

How to Become a Threat Hunter

Threat-Hunting Process

The Ultimate Guide to Threat Hunting

Top 5 (deliberately) vulnerable web applications to practice your skills on

Women in Cybersecurity: More Credentials, Less Pay & Even Fewer Opportunities

The Gaming Industry: A Privileged Target for Crooks — The Fortnite Case

Spam vs. phishing: Definitions, overview & examples

How to Get Your Employer to Pay for Your IT Security Training — 10 Steps

BabaYaga and the Rise of Malware-Destroying Malware
BSides Vancouver: 2018 Walkthrough
Can you spot the phishing scams in 3 of our most popular templates?
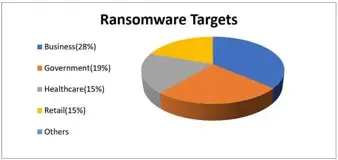
All about SamSam Ransomware
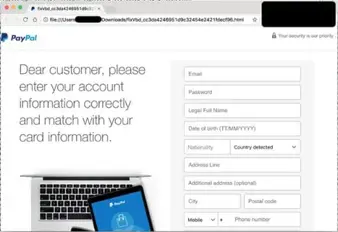
Five techniques to bypass Office 365 protections used in real phishing campaigns

Detecting Data Breaches with Honeywords