Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
API hooking

iOS Application Security Part 33 - Writing tweaks using Theos (Cydia Substrate)

Invoking Assembly Code in C#

Human-implanted RFID chips
Information Security Policies

Murdering Dexter

Information gathering using Metasploit

Jus in Cyber Bello: How the Law of Armed Conflict Regulates Cyber Attacks Part II

ASP.NET Website Optimization

.NET penetration testing: Test case cheat sheet

Putting Unstructured Data Into Context: What the Cosmos Can Teach Us About Unstructured Data
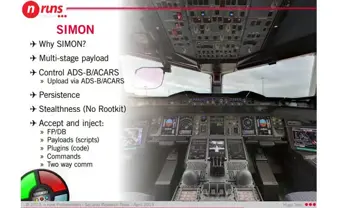
Cyber Threats against the Aviation Industry

8570 Certification and the Way Ahead to 8140 Certification
What Good is Tor?
Cookies with HttpOnly Flag: Problem in Some Browsers

3 Cyber Threats, One Simple Solution
Hunting Session Fixation Bugs

CompTIA Security+ SY0-401 vs. SY0-301 Changes [DECOMMISSIONED ARTICLE]

Server Side Includes (SSI) injection

SkypeFreak: A Cross-Platform Skype Forensic tool
Can My JavaScript Access Your Page Elements?

Android hacking and security, part 1: Exploiting and securing application components

Information Security Policy For SME
Exploiting by information disclosure, part 1