Access Control Models for ICS/SCADA environments
Introduction
Access control for critical infrastructure requires moving the perimeter to workloads and managing access based on context. This zero-trust approach ensures access based on user/device characteristics, target workloads and associated risk. In this article, I give an example of one of two general approaches to achieving zero-trust ICS networks.

Get your free course catalog
Microsegmentation
Zero-trust network (ZTN) design begins with microsegmentation. Usually controlled with software, microsegmentation creates security zones based on risk. These zones have stronger access controls than those we traditionally create with VLANs and VLAN access control lists.
Software-defined perimeters like Cisco’s Application Centric Infrastructure (ACI) use VXLANs and a software-defined network solution. This is an excellent approach for organizations with resources to protect that were designed with security and controlled access in mind. This is not true of many ICS/SCADA networks.
We must consider that many ICS networks were implemented 30 years ago … or more. They were implemented with little effort at controlled network access. This is why using next-generation firewalls designed for microsegmentation is a good approach: use of firewalls enables segmentation across any network infrastructure. Microsegmentation begins by defining the various layers of an ICS network.
The Purdue model
The Purdue model is the basis for our segmentation design. The Purdue model, adopted from the Purdue Enterprise Reference Architecture (PERA), is a widely adopted ICS framework that shows how the various elements of an ICS architecture interconnect.
The Purdue model consists of three zones and five levels.
- Enterprise zone
- Level 5: Enterprise network
- Level 4: Site business and logistics
- Industrial DMZ
- Manufacturing/Industrial zone
- Level 3: Site operations
- Level 2: Area supervisor control
- Level 1: Basic control
- Level 0: The process
Enterprise zone
The resources in this zone include applications and infrastructure used to manage the business overall, including ERP, HR, financials and customer relationship management. This is done at Level 5. It is not part of the ICS network, but it requires input from the ICS network for billing, planning and other business activities.
Level 4 includes the IT services and infrastructure that support the production processes, including database servers, email, supervisor desktops and so on. Level 4 interfaces with Level 3 to provide business information to Level 5.
Industrial DMZ
The industrial DMZ is a layer between the enterprise zone and the manufacturing/industrial zone. It is like a traditional network DMZ, providing the first layer of defense against the enterprise zone, which includes internet access.
Manufacturing zone
The systems that support plant-wide operation reside in Level 3. “Think of centralized control rooms with HMIs and operator terminals that provide an overview of all the systems that run the processes in a plant or facility.” (Source: Packt). It is these systems that collect data aggregated from across the plant floor and provide them to Level 4 systems. It is in Level 3 where operators monitor operations and perform centralized control tasks.
Level 2 includes controls similar to those found in Level 3. However, controls at this layer apply to specific areas of the production environment.
Basic controls are in Level 1. Devices here directly enable production equipment operation. This includes activities like opening and closing valves. PLCs typically exist at this level, although some exist at Level 2, providing general controls over a wider area.
Level 0 includes the equipment we are controlling: the devices that produce or deliver a product, power, gas and so on.
Controlling zone access
Figure 1 shows a simple approach to segmenting the zones. Segmentation is based on zones and levels within the manufacturing zones.
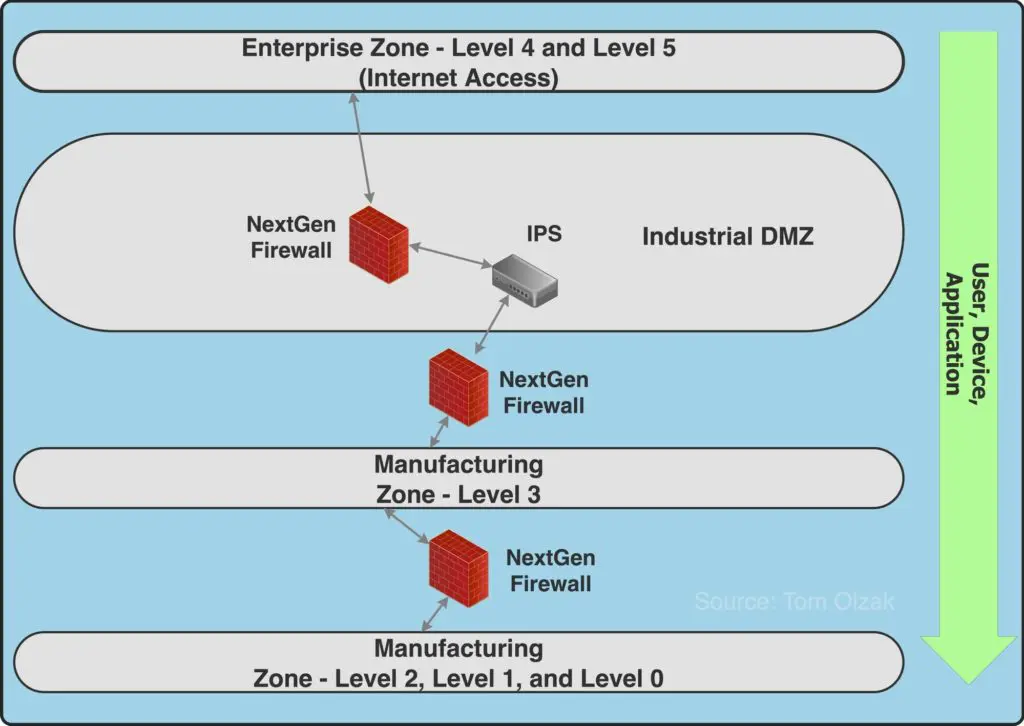
Figure 1
Enterprise zone access
The enterprise zone is assumed hostile. Consequently, no traffic should flow between the enterprise zone and the manufacturing zone Levels 0, 1 and 2. Access between the enterprise zone and manufacturing zone 3 should be limited to:
- Providing data to databases in the enterprise zone used by management for production planning, fulfillment management and so on
- Allowing external entities to access HMI and other systems at Level 3 to perform support services
Note that all traffic is allowed or blocked based on the user/application-seeking access, the device used and the target application/resource. Because reliance on user identity verification is an essential piece of this process, access to manufacturing zones should require multi-factor authentication.
Manufacturing Level 3 access
Level 3 is provided access to Levels 0, 1 and 2. Access is still controlled by user, device and application/resource.
Levels 0, 1 and 2 in this example are all on the same network segment. This helps ensure business continuity if a network failure occurs between Level 3 and the lower levels.
Conclusion
A zero-trust approach assumes that all network segments and users/resources on those segments are hostile. This translates into the business network being a hostile environment when planning access to ICS.
The industrial DMZ manages traffic between the business network and the ICS by applying policies based on user/application identity, source device and the target workload. Network architects must work closely with security teams to define traffic absolutely necessary, who and what is involved in that traffic, and block everything else.

Send a free phishing test — right now!








