Security+: Technologies And Tools - DLP [DECOMMISSIONED ARTICLE]
NOTE: This article reflects an older version of the Security+ Exam – please see the current Security+ Certification page for the most up-to-date information.
Introduction
To any business or corporation, information and data are the blood flow of daily operations. This consist of market intelligence as it relates to your competition, the sensitive customer information (such as contact info, credit card/banking numbers, etc.), and even your own internal data. Safeguarding all of this is a must, not only from it being hacked into but also making sure that only the authorized employees have access to it.
This is technically known as “Data Loss Prevention,” or “DLP” for short. A specific definition is as follows:
“It set of tools and processes used to ensure that sensitive data is not lost, misused, or accessed by unauthorized users. DLP software classifies regulated, confidential, and business critical data and identifies violations of policies -- typically driven by regulatory compliance such as HIPAA, PCI-DSS, or GDPR. Once those violations are identified, DLP enforces remediation with alerts, encryption, and other protective actions to prevent end users from accidentally or maliciously sharing data.” that could put the organization at risk.” (SOURCE: 1)
As a Security+ cert holder, you need to be aware of the basic concepts of DLP, as well as some of the latest technologies that are used.
See Infosec IQ in action
The Basic Concepts of DLP
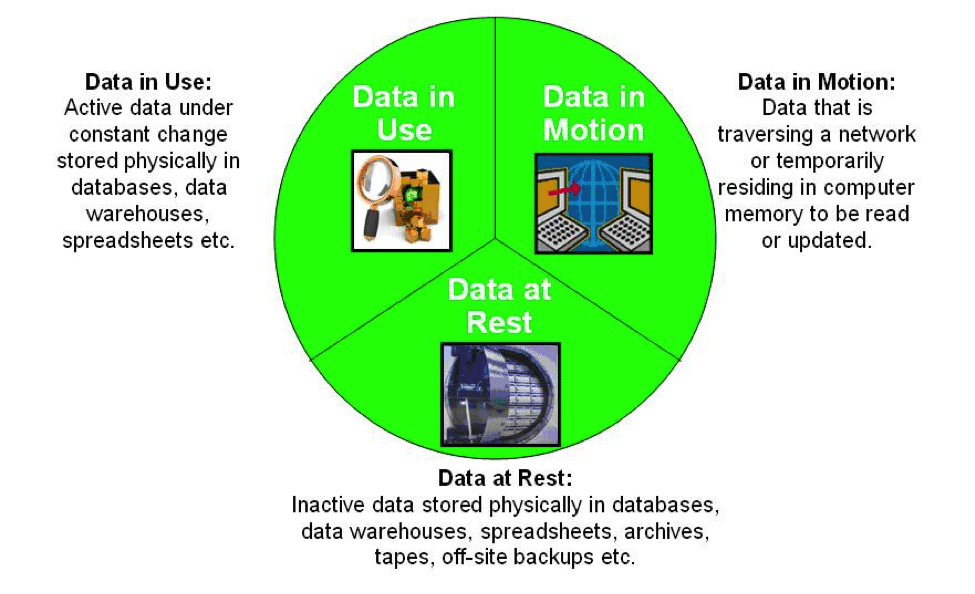
Three types of DLP Systems are used today in organizations, and they are as follows:
- In Use Protection:
This is the information/data that is generally used on a daily by authorized employees or even software applications within the organization. Typically, these types of datasets are used to deliver products and services to customers as they are being requested or purchased. This type of information is normally encrypted constantly so that if they were to be intercepted by a malicious third party, it would remain in a garbled and undecipherable state.
This is the information/data that is in transit across a particular network segment, and typically requires a higher level of encryption given this dynamic nature, to prevent against any form of Eavesdropping and Decryption related attacks. The basic rule of thumb here is that the more sensitive (or even more valuable) the information/data is, equally higher levels of encryption are needed as well.
This is the information/data that is not actively being used in any form, and as a result, it typically resides on a database server. These datasets still need to have some layer of encryption, but not to the level of the data that is In Use or In Motion. At this point, it is important to implement the principle of “Need to Know” access to those employees who must have access to these datasets.
The illustration below further illustrates these three concepts:
(SOURCE: https://en.wikipedia.org/wiki/Data_at_rest)
The Required Controls for Data Loss Prevention
Before any DLP technologies can be evaluated, it is first important to understand the controls that are needed for each focus area of the data described in the last section. Once this has been established, then the appropriate DLP software package can be selected and deployed. The following matrices depict the necessary controls for each type of data:
Data in Motion
(SOURCE: http://www.ey.com/Publication/vwLUAssets/EY_Data_Loss_Prevention/$FILE/EY_Data_Loss_Prevention.pdf ).
Data in Use
(SOURCE: http://www.ey.com/Publication/vwLUAssets/EY_Data_Loss_Prevention/$FILE/EY_Data_Loss_Prevention.pdf ).
Data at Rest
(SOURCE: http://www.ey.com/Publication/vwLUAssets/EY_Data_Loss_Prevention/$FILE/EY_Data_Loss_Prevention.pdf).
Important Features of DLP Solutions
Now that you have identified the right technological control that is associated with each focus area of the three data types, the next step as a Security+ cert holder is to evaluate the appropriate software package that can be used in the best way for your organization. There are many tools that are available, but whatever you select must contain at a minimum, the following features:
- Fingerprinting of documents and their file sources:
This where all copies of information and data are recorded upon, and thus each and every document in this regard must be “fingerprinted” to uniquely identify them. This could include an assortment of watermarks, numerical/alphanumerical naming conventions, etc. It is also important to keep a version history of any modifications, revisions, or edits that are made to these respective documents.
This is especially crucial for those datasets that fall under the category of “Data in Motion.” They need to be closely monitored across all network mediums, and any other associated network-based perimeters as they travel from point to point to the final destination.
All the information/data that fall under the three categories must also be uniquely identified as well.
This applies primarily to the information and data that falls under “Data in Motion.” There are various methods by which all of this can be transmitted, which are primarily using Internet-based applications, E-Mail, Instant Messaging, etc. As a Security+ cert holder, you must have the ability to block ultra-sensitive datasets that are either coming or leaving a questionable network segment.
In this regard, it is very important to have a central repository for the following, so it can be easily analyzed:
- The document fingerprints;
- The inspection modes;
- Anomalies in the pattern matching;
- All archiving and logging actions and behaviors.
It is important to remember that the best DLP software packages can monitor all of the network traffic and who is accessing what across all of the three information/data categories; as well as block any suspicious activity and keep the most sensitive datasets from leaked out to the wrong recipient(s).
The DLP Software Packages
These come in three main categories:
- Network-based solutions:
These are typically installed at the endpoints of a network perimeter and can identify/block any malicious incoming traffic that can affect the datasets.
These are deployed on all employee workstations, servers, and wireless devices. They monitor all sorts of electronic communications, and if any are deemed to be suspicious in nature, it will block access to the datasets of the employees in question. These solutions can also monitor and block any physical device that has any kind of sensitive information/data on them.
These make use of Artificial Intelligence, Machine Learning, and Neural Network mathematical algorithms to determine any anomalies or the most granular suspicious behavior when the datasets are being accessed.
The top-ranked DLP software packages are as follows:
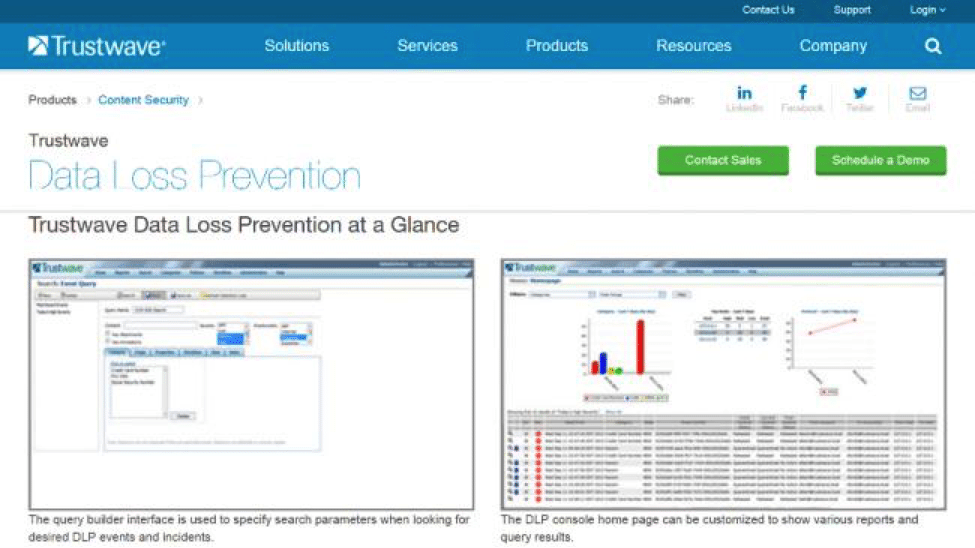
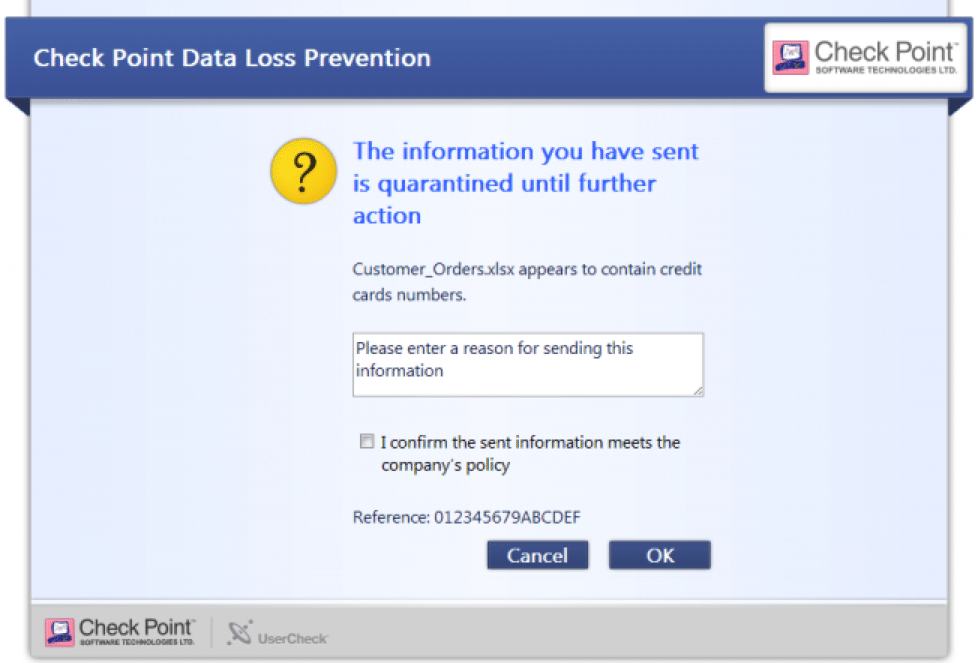
Trustwave Data Loss Prevention
McAfee Total Protection for Data Loss Prevention
Check Point Data Loss Prevention

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
Conclusion
Overall, this article has examined what DLP is about, the categories that information and data fall into, as well the criterion that you, the Security+ cert holder, need to apply when selecting the right software package for the organization that you work for.
If you are a candidate that is planning to take the Security+ exam, here are some free resources that are directly applicable to the CompTIA DLP exam objectives:
- https://www.professormesser.com/security-plus/sy0-401/data-loss-prevention-2/
- http://blogs.getcertifiedgetahead.com/data-loss-protection-dlp-and-security/
- https://www.lynda.com/Security-tutorials/Data-loss-prevention/601805/667304-4.html
- https://www.linkedin.com/learning/comptia-security-plus-sy0-401-cert-prep-compliance-and-operational-security/data-loss-prevention-dlp
Sources
- https://digitalguardian.com/blog/what-data-loss-prevention-dlp-definition-data-loss-prevention
- http://www.tomsitpro.com/articles/what-is-data-loss-prevention-dlp,2-473.html
- https://en.wikipedia.org/wiki/Data_at_rest
- https://www.techradar.com/news/top-5-best-data-loss-prevention-services
- www.ey.com/Publication/...Data_Loss_Prevention/.../EY_Data_Loss_Prevention.pdf