Hacking Implantable Medical Devices
Contemporary healthcare relies heavily on medical devices to help patients lead normal and healthy lives. Yet there are security problems ranging from cyber exploitation to common bugs in the software. This article focuses more on implantable medical devices (IMDs) — insulin pumps and pacemakers/defibrillators in particular — their security flaws and existing protective mechanisms.
Modern IMDs are entrusted with vital tasks in terms of medical care: delivering insulin or painkillers at proper rates, measuring and collecting data on the vital signs and passing it on to doctors and nurses, and direct stimulation of an organ's critical function, as the case is with pacemakers.

Send a free phishing test — right now!
IMDs are like microcomputers that not only have hardware but also have an elaborated software core at their disposal: "A pacemaker may depend on more than 80,000 lines of code to keep it going, and a magnetic-resonance imaging (MRI) scanner more than 7m lines."
Since these mechanisms are de facto essentially embedded PCs, the question of security pops up in an instant. In a way, their proximity to computing devices exposes them to all security flaws characteristic of mainstream technology. Incidents are inevitable. Sometimes they entail grievous and fatal consequences, as the case was in the 1980s when the bad software design supporting one kind of radiotherapy machine caused emission of massive overdoses of radiation rays on several patients, taking the life of at least five of them. In a more recent case, security researchers exposed software vulnerabilities in modern X-ray machines. On the other hand, sabotage is a possibility to be reckoned with, especially given how so many devices today are interconnected and remotely configurable.
Source: Controlling for Cybersecurity Risks of Medical Device Software
Source: Controlling for Cybersecurity Risks of Medical Device Software
Wireless Capabilities
Pacemakers as implantable medical devices have been around since the distant 1958, but their evolution took a dramatic turn in 2009 when they became part of the Internet of things. Implantable medical devices such as insulin pumps and defibrillators possess wireless connections for doctors and technicians to download data (e.g., timing of insulin doses; frequency of heart-shocks) or make updates or modifications without requiring surgery.
As specialists agree, the wireless feature of IMDs is useful from a medical point of view. Without it, these apparatuses cannot be fixed remotely, nor can they start up their warning function to alert a medical person if it is out of order; let's say there is a burned wire or short circuit.
Another reason why all implantable devices are open to the radio controlled systems is simple—alternative methods like passwords would not prove time-efficient in the event of emergency, for instance, if the person with the device is unconscious.
Although there is a clear security risk, the benefits outweigh the small chances of someone with bad intentions subverting the connectivity embedded in these life-sustaining gadgets.
IMDs as an Object of Research
Diagram 1
Continuous Glucose Monitoring System and Insulin Pump
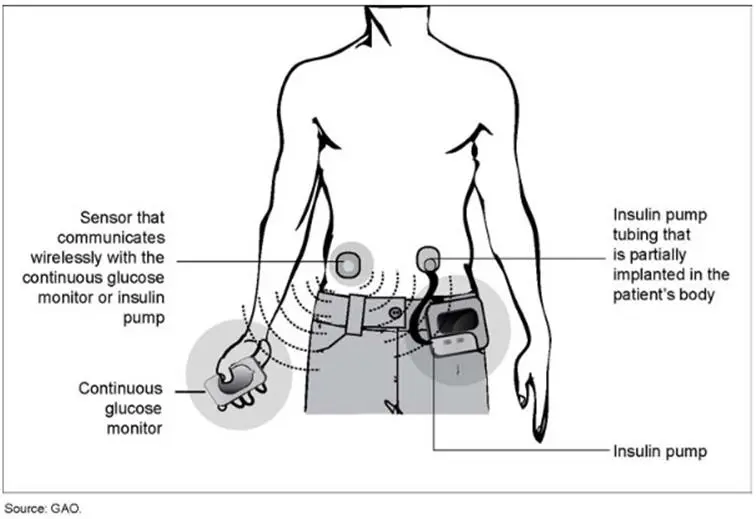
Medical hacking is a relatively new topic that entered the public space only recently. In 2011, IBM computer security expert Jay Radcliffe made a presentation on how an insulin pump can be manipulated to disperse a lethal amount of insulin.
As part of the reconnaissance phase, Radcliffe performed a check-up of the manual for his personal insulin device. From there he acquired the exact frequency and modulation method his apparatus operates on, the size of the packet, and the frequency of the transmissions. In addition, the Federal Communication Commission (FCC) ID of the device found also in the manual allowed him to obtain the patent documents for the device – an abundant source of invaluable data on the functionality and composition of the device.
His findings resulted in the purchase of the Arduino module, a wireless peripheral, which utilized similar frequencies to those of the insulin pump he owned. The command codes and message formatting were easily discoverable on Google, although the manufacturer had not disclosed this information. The wireless peripheral device can scan for insulin pumps in the vicinity of 100 to 200 feet. Once a pump is on sight, changing configuration settings would only take seconds. However, the attacker needs to know first the serial number of the targeted insulin pump and for that he would have to have physical access to the device prior to its wireless hacking.
A step forward in the evolution of hacking insulin pumps was made two months later. Initially famous for breaking into ATMs, Barnaby Jack from McAfee succeeded in taking control of both an insulin pump's radio control and vibrating alert safety mode. Jack's hacking kit included a special piece of software and a custom-built antenna that has a scan range of 300 feet and for which the operator does not need to know the serial number. Therefore, the latest models of Medtronic insulin pumps, equipped with small radio transmitters allowing medics to adjust function, can become easy prey to this hacking invention that scans around for insulin pumps. Once the hacker sets foot in the targeted machine, he can then disable the warning function or/and make it disperse 45 days worth of insulin all at once – a dose that will potentially kill the patient.
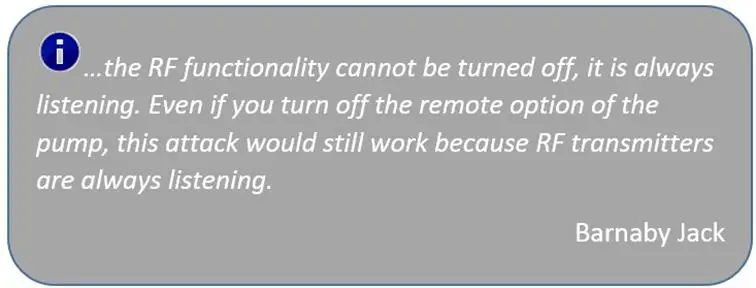
Source: McAfee's Barnaby on Medical Device Hacking
Diagram 2
Illustration of Barnaby Jack's Insulin Pump Hacking

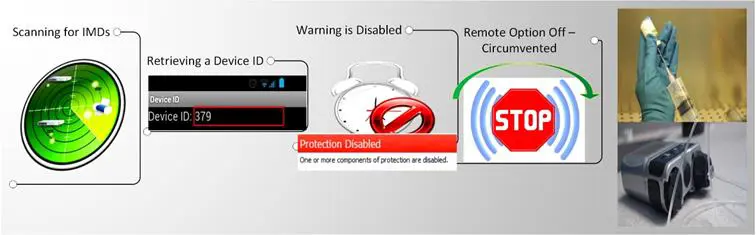
Diagram 3
Difference Between Pacemakers and ICDs
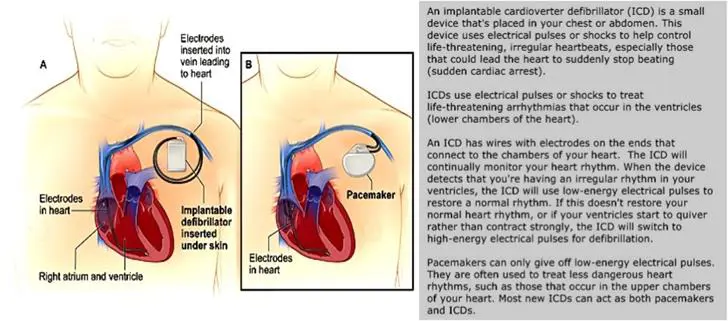
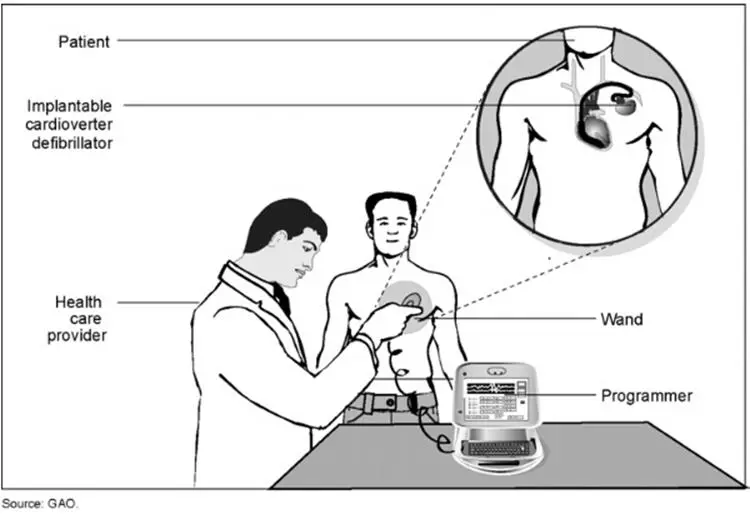
Previous versions of ICDs were reprogrammed by doctors via a wand that has to be slid near the patient carrying such a device (See Diagram 4). The wand starts up a software switch for passing on instructions. Nowadays ICDs manufacturers try to straddle the wireless technology. In 2006, full radio-frequency based implantable devices met the approval of the U.S. Food and Drug Administration (FDA) to operate in the 400MHz range.
Diagram 4
Wireless interaction between the Defibrillator, Wand, and Programmer
The topic of this type of hacking raised awareness after the show Homeland aired an episode in which the plot depicted how the U.S. Vice President was assassinated through a pacemaker hack. In real life, former U.S. Vice President Dick Cheney, who has had a serious heart condition throughout the years, had his medicine crew disable the wireless capabilities of his defibrillator implanted in 2007.
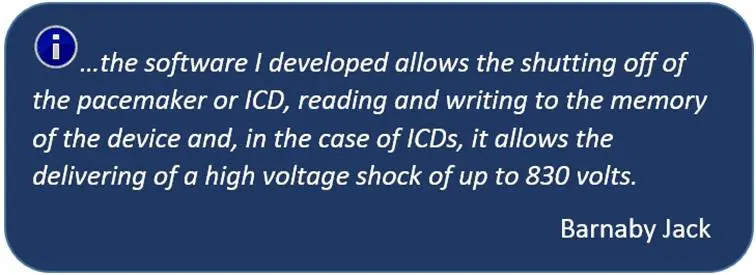
Barnaby Jack also demonstrated that a pacemaker and implantable defibrillator can be exploited to withhold therapy or deliver a deadly 830-volt shock, as the case is with the latter. It can be done via laptop from 30-50 feet away, whose specially-crafted software seizes control over the targeted device through its wireless transmitter.
Jack discovered how to make ICDs disclose their serial and model number during interception of the wireless signal, and use them to alter the factory program code of a transmitter so as to reprogram the ICD/pacemaker in a human body. According to him, the ease of this nefarious computer intervention comes in consequence of the fact that the FDA is focused primarily on the medical effectiveness of devices, not the robustness of the device's code.
Additionally, some personal data such as patients' names and doctors can be extracted from the targeted ICD as well.
In fact, due to the lowered standard of code's protection, Jack managed to find an access point to a company's remote servers used to engineer the software. He could upload there and then disseminate crafty firmware "that would infect multiple pacemakers and ICDs, spreading through their systems like a real virus."
"We are potentially looking at a worm with the ability to commit mass murder," Barnaby Jack added.
Source: Barnaby Jack Could Hack Your Pacemaker and Make Your Heart Explode
Diagram 5
Pacemaker — Shutting Off + Reading/Writing to the Memory
ICD — Shutting Off + Reading/Writing to the Memory+ Electric Shock of up to 830V
Why Don't We Know More About the Security Issues in Current Pacemakers/ICDs?
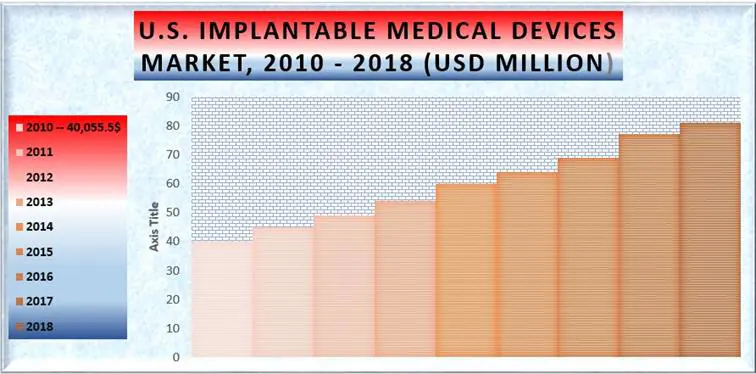
U.S. Industry Analysis, Size, Share, Trends, Growth And Forecast 2010 - 2018
The medical device market is a fast-developing, seemingly ever-growing business that brings considerable earnings. Yet most of the medical devices comes into being from the factory with little to no built-in security mechanisms. According to some critics, manufacturers do not search their products too hard for vulnerabilities because they don't want to admit there are any. Perhaps they fear that would be bad for business. Another thing that medical device manufacturers probably won't like is IT researchers like Barnaby Jack, whose brilliant work reveals serious security flaws existing in the products on the market, dissuading people from entrusting these devices with their life (well, if they can afford to do that). Many common people do not apprehend the concept of white hat hacking (See the two readers' comments below). They shudder at the thought that someone could remotely exploit an apparatus that sustain vital functions in their body, even if the person who performs it has good intentions to improve the defence system of what is next in the pipeline.
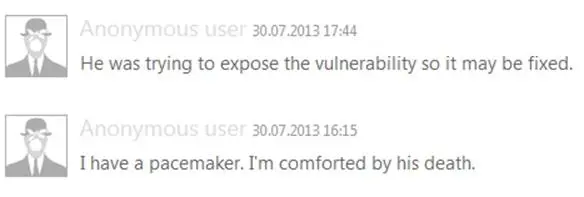
Source: Hacker dies days before he was to reveal how to remotely kill pacemaker patients (Comments)
The fact is that Barnaby Jack died only a week before his presentation on pacemaker hacking at the Black Hat in Las Vegas (2013). For his sympathisers, the official cause of death – drug overdose – sounds utterly implausible. Someone might say that both this case and the strange death of the journalist Michael Hastings merely awakens whistleblowers and conspiracy thrill seekers out of their slumber. Someone might also say that people in power prefer some secrets to remain buried and some words to be left unsaid.
Defensive Mechanisms for IMDs
Heart-to-Heart (H2H)
A partnership between teams of researchers from Rice University and the security firm RSA has created the heart-to-heart system, a measure that may protect IMDs. Based on a heartbeat reading, this new method serves as a biometric authentication to confirm that whoever is trying to download data or reprogram critical features of the devices is a real person authorized to do so, not a remote hacker.
For the heart-to-heart system to work, a doctor utilizes a device against the patient's body, which measures the heartbeat. This measurement of the patient's heartbeat is run against the reading relayed through a wireless signal coming from the IMD itself. If the signals match, then the handshake is completed and the medical personnel gains access to the implant. The H2H approach just marks off the pause between beats and matches the two readings, and as Ari Juels, one of the creators of the system, further explained: "Our approach doesn't rely on a registration of a biometric—all it does is check that the signals are identical."
Diagram 6
Comparing ECGs
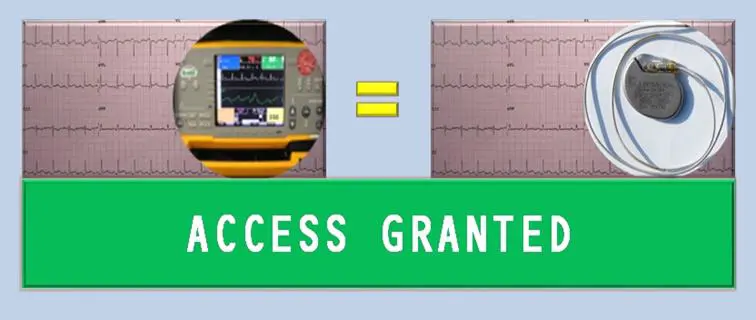
H2H can be particularly helpful in an emergency situation because is not unreliable or time-consuming, as the password methodology may prove to be. Manufacturers fear that passwords can be stolen, lost or merely forgotten, which can be fatal when the time for recovering them is limited or a matter of life and death. The research scientist at BBN Technologies Shane Clark attested that in the context of IMDs, traditional security methods "have the potential to endanger the lives of patients in an emergency situation where authentication fails."
The human heart constantly produces a unique rhythm, so the password or fingerprint is different in each measurement. At the same time, the graph depicted through human heartbeats – the ECG – shares up-and-down spikes common to each person. However, "the exact shape of ECG spikes varies from person to person. Everyone has his or her own unique shape, which remains even during heart rate changes caused by excitement or exercise."
Of significant importance is the fact that the heartbeat signal is encrypted in order to thwart any attempt of hijacking and exploiting that could be made in theory by black hat hackers. "[T]he fact that you are reading a random changing symbol means the attacker can't profile the heartbeat at one time and use the information later to attack the device." Juels adds.
Scientists contemplate that in near future, the heart beat authentication procedure will be implemented in PCs, smartphones, notebooks, tablets, etc. as a contrivance for identification. For now, the fingerprinting is still more accurate, but the heart beat biometrics is a good alternative or supplement.
Encryption
Theoretically speaking, encrypting the data/signal residing in the IMDs is effective protection. From an empirical standpoint, however, the processing power and time needed impact the functionality of these devices. Actually, implants and wireless transmitters possess AES (Advance Encryption Standard) encryption, but it is not enabled.
The MedMon Firewall
Another joint effort between Princeton University NJ and Purdue University led to the development of a prototype firewall that could safeguard present and future innovations in the medical manufacturing industry against information threats. It looks for:
Physical anomalies – abnormal characteristics of wireless signal can indicate the presence of a danger. An example of that would be signals beyond specific range or coming at different intervals.
Diagram 7
An Example of an Abnormal Wireless Signal
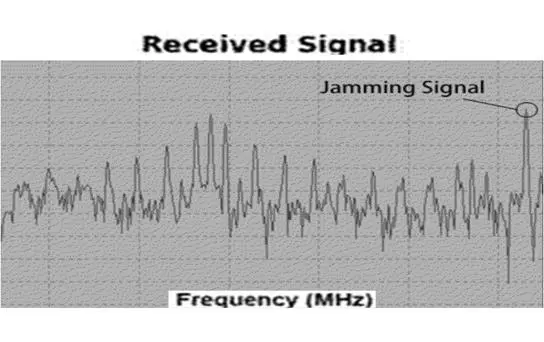
Behavioural anomalies – it fends off suspicious command and data irregularities. Again, by way of example, the MedMon firewall would intercept ill-natured deeds like when "someone is trying to cause multiple or higher dosages to be administrated to the patient that's beyond the [acceptable] range."
Sounds handy, but they should be aware of the security risks, too.
Conclusion
Thankfully, there have been so far no publicly known records of a cyber attack on IMDs in the real world. Without any doubt, patients benefitting from their invaluable help are better off with them, in spite of their security imperfections. Many people simply cannot live normally if these technical gears are not operating at their best 24/7. For them, having one is not a matter of choice, it is a matter of existence.
Source: McAfee's Barnaby on Medical Device Hacking
On the other hand, clearly there are technological vulnerabilities in these devices pregnable to interference by skilled programmers. It won't be a pleasant sight if every time you see nearby someone with a laptop or a smartphone, you almost have a heart attack. Then, you better have something powerful ticking inside you that will shock you back to life. Something you could really trust.
Reference List
Basu, E. (2013). Hacking Insulin Pumps And Other Medical Devices From Black Hat. Retrieved on 22/04/2014 from http://www.forbes.com/sites/ericbasu/2013/08/03/hacking-insulin-pumps-and-other-medical-devices-reality-not-fiction/
Bennett, D. (2013).
A Password Even a Hacker Supervillain Can't Crack. Retrieved on 22/04/2014 fromhttp://www.businessweek.com/articles/2013-09-26/heartbeat-based-passwords-could-protect-pacemakers-from-hackers
Caputo, I. (2014). Hacking To Improve Health Care. Retrieved on 22/04/2014 from http://wgbhnews.org/post/hacking-improve-health-care
Cherry, S. (2013). Hacking Pacemakers. Retrieved on 22/04/2014 from http://spectrum.ieee.org/podcast/biomedical/devices/hacking-pacemakers
Diep, F. (2012). Logging In with Your Heartbeat. Retrieved on 22/04/2014 from http://www.livescience.com/23656-logging-in-with-your-heartbeat.html
Dimov, D. (2013). Privacy Implications of Google Glass. Retrieved on 22/04/2014 from /privacy-implications-of-google-glass/
Dimov, D. (2013). Privacy Implications of the Internet of Things. Retrieved on 22/04/2014 from /privacy-implications-internet-things/
Ericson, J. (2013). Keeping Hackers Out Of Your Body: 'Heartbeat Password' Protects Pacemakers, Implanted Insulin Pumps From Cyber Intrusion. Retrieved on 22/04/2014 from http://www.medicaldaily.com/keeping-hackers-out-your-body-heartbeat-password-protects-pacemakers-implanted-insulin-pumps-cyber
Fu, K. and Blum, J. (2013). Controlling for Cybersecurity Risks of Medical Device Software. Retrieved on 22/04/2014 from http://www.csl.sri.com/users/neumann/cacm231.pdf
GAO (2012). Information Security of Active Medical Devices. Retrieved on 22/04/2014 from http://www.gao.gov/assets/650/647767.pdf
Kirk, J. (2012). Pacemaker hack can deliver deadly 830-volt jolt. Retrieved on 22/04/2014 from http://www.computerworld.com/s/article/9232477/Pacemaker_hack_can_deliver_deadly_830_volt_jolt
Leonard, S. (2012). Prototype Firewall Could Prevent Malicious Medical Device Hacking. Retrieved on 22/04/2014 from
http://www.qmed.com/mpmn/article/prototype-firewall-could-prevent-malicious-medical-device-hacking
Lewis, T. (2013). Medical Devices Vulnerable to Hackers, New Report Says. Retrieved on 22/04/2014 from http://www.livescience.com/39889-medical-devices-vulnerable-to-hackers.html
Maron, D. (2013). A New Cyber Concern: Hack Attacks on Medical Devices. Retrieved on 22/04/2014 from http://www.scientificamerican.com/article/a-new-cyber-concern-hack/
Talbot, D. (2013). Encrypted Heartbeats Keep Hackers from Medical Implants. Retrieved on 22/04/2014 from http://www.technologyreview.com/news/519266/encrypted-heartbeats-keep-hackers-from-medical-implants/
T.S. (2013). How vulnerable are medical devices to hackers? Retrieved on 22/04/2014 from http://www.economist.com/blogs/economist-explains/2013/06/economist-explains-5
Wadhwa, T. (2012). Yes, You Can Hack a Pacemaker (and Other Medical Devices Too). Retrieved on 22/04/2014 from
http://singularityhub.com/2012/12/09/yes-you-can-hack-a-pacemaker-and-other-medical-devices-too/
Diagrams and Charts
Diagram 1 and Diagram 4 are provided by GAO in their "Information Security of Active Medical Devices" report (page 6 and page 7). Retrieved on 22/04/2014 from http://www.gao.gov/assets/650/647767.pdf
Diagram 3 is based on information provided by National Heart Lung and Blood Institute and titled Implantable Cardioverter Defibrillator. Retrieved on 22/04/2014 from http://www.nhlbi.nih.gov/health//dci/Diseases/icd/icd_all.html

Learn Secure Coding Fundamentals
"U.S. implantable medical devices market 2010-2018" chart is based on such that can be found here. Source: Integrated Healthcare Association, National Center for Biotechnology, Office of Statewide Health Planning and Development, Transparency Market Research. Retrieved on 22/04/2014.







