Weapon of anonymous
Before starting, I would like to give a small preview about the topic. This article focuses on the world famous hacker group, known as "Anonymous." I will be describing their attacking methodologies and way of planning, but we will be focusing more about the weapons or tools they use. The word anonymous simply means having no name or identity. The group Anonymous is a faction of hackers or hacktivists. They have their own website and IRC (Internet Relay Chat) channel where they hold lax online gatherings that focuses on brain storming. Rather than giving orders, the group uses a voting system that chooses the best way in handling any situation. This group is famous for their hacks, one of which is Distributed Denial of Service (DDOS) attacks on government websites, well-reputed corporate websites, and religious websites. Their famous slogan is:
We are Anonymous
We are Legion
We do not forgive
We do not forget
Expect us

What should you learn next?
This is the signature of Anonymous that can be seen in their every attack.
Skills of Anonymous hackers

They are people with excellent hacking skills, but they use conventional black hat techniques and methods. In fact, their hacking techniques are familiar with other hackers. For example, they also use the same tools used by other hackers, like havij and sqlmap in performing an SQL injection attack on any website. In other words, they are able to take advantage of common web application vulnerabilities which can be found in many websites.
The Anonymous hackers are comprised of two types of volunteers:
- Skilled hackers –This group consists of a few skilled members that have expertise in programming and networking. With their display of hacking skills, one can surmise that they have a genuine hacking experience and are also quite savvy.
- Laypeople – This group can be quite large, ranging from a few dozen to thousands of volunteers from all over the world. Directed by the skilled hackers, their primarily role is to conduct DDoS attacks by either downloading and using special software or visiting websites in order to flood victims with excessive traffic. The technical skills required in this group ranges from very low to modest.
There was about a 10:1 ratio of laypeople to skilled hackers.
The Anonymous hackers' first objective is to steal data from a website and server. If it fails, that is the time they attempt a DDOS attack. They are a very well-managed group. Before selecting a target, they conduct a voting poll in the internet. After that, they name their operation.
They already organized many operations that became very famous, one of which is "Pay Back" which became famous all over the world back in 2010. In operation Pay Back, they stopped the services of well known e-commerce business solutions, such as PayPal, Visa, MasterCard, and Sony by performing D-DOS attacks on them. There are many other operations which were conducted by this group such as Operation leakspin, Operation Israel, Operation Facebook, Operation Gaza, etc.
In the figure below, we can see an example of their voting system for an operation.

After the voting poll, they decide what the next operation is.
In the figure below, we have shown a good example of their voting response.

After finalizing voting for the target, the operation process proceeds.
Their hacking operation consists of three different phases.
- Recruiting and communication phase
- Reconnaissance and application attack phase
- DDOS attack phase
1. Recruiting and communication phase: In this phase, Anonymous uses social media in recruiting members and promoting campaigns. In particular, they use popular social networking sites like Twitter, Facebook, and YouTube to suggest and justify an attack. This is really the essence of all hacktivism campaigns. Messages were spread via social media such as Facebook, Twitter and YouTube.
The content during this phase:
- Explains their political agenda for the campaign. In this case, a website was created that rationalized the attack. Twitter and Facebook were used to bring attention to the website and its arguments. In addition, YouTube videos further rationalizes the attack by denigrating the target and exposing perceived transgressions.

- Declared the dates and targets for protest in order to recruit protesters and hackers.

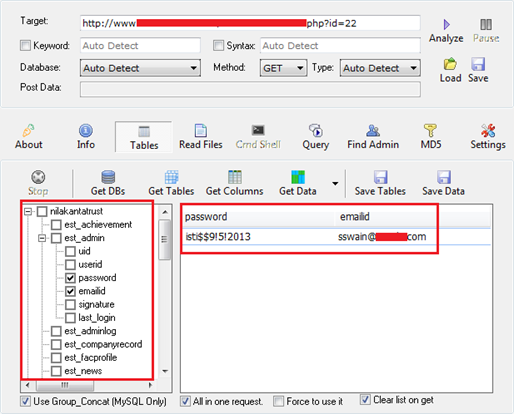
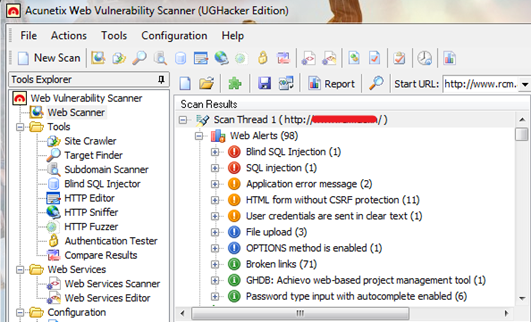
2. Reconnaissance and application attack phase: In this phase, the attackers have a sound knowledge on attacking tools. They use anonymity services to hide their identity and maintain a low profile. Their attack traffic levels during this phase were relatively low, especially when compared to the attack phase. However, the reconnaissance traffic was relatively high compared to ordinary days. An attacker tries to penetrate the web application by using famous tools like Havij, Acunetix Web vulnerability scanner, etc.
Example of tools used is stated below:
Havij- Havij is an automated SQL Injection tool that helps penetration testers to find and exploit SQL Injection vulnerabilities on a web page. By using this software, a user can perform back-end database fingerprint, retrieve DBMS users and password hashes, dump tables and columns, fetch data from the database, running SQL statements and even access the underlying file system and executing commands on the operating system.
Acunetix - The Acunetix Web Vulnerability Scanner is an automated black box scanner that checks websites and Web applications for vulnerabilities such as SQL injection, Cross Site scripting, and other vulnerabilities.
Once the attacker successfully exploits any of these vulnerabilities, Anonymous will deface the website by replacing their website's home page with their defaced page that looks like the figure below, with their slogan and a message to the world.

3. DDOS attack phase: DDOS attack it is the deadliest attack they use and is performed by their skilled hackers. If they fail to penetrate the web application then they go for this attack. They are also famous for this attack because whenever they perform this attack, they always succeed on their operation. But before conducting a DDOS attack, the anonymous group provides a list of tools in different social media like in an IRC channel, Facebook, pastebin, etc.
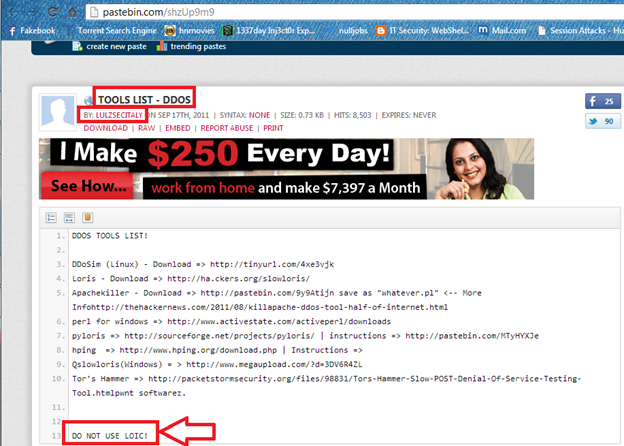
Some of the famous and powerful tools used by the Anonymous group are H.O.I.C, Pyloris, Qslowloris, Torshammer, etc.
I am going to show you some of the usage of the tools.
H.O.I.C- Also known as High Orbit Ion Cannon. It is a simple script launching HTTP POST and GET requests at the target server. It is a cross platform tool easily found for Windows, MAC and Linux platforms. As we can see in below figure Click on plus icon which opens a new small windows for adding targets.
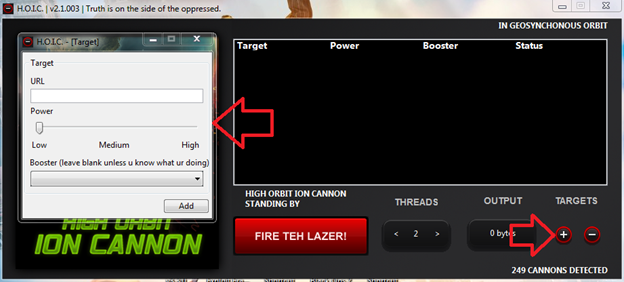
Input the target address in URL box then set the power level to Low, Medium and High as your requirement.
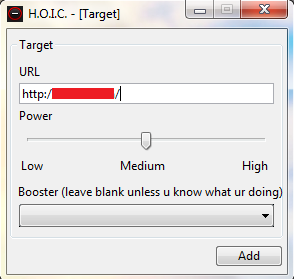
In the figure above, we can see the third option was left blank.
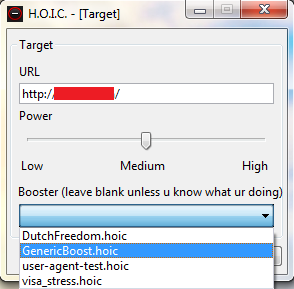
HOIC's boosters are used to tailor the HTTP requests sent by HOIC to the target for a specific type of attack. "HOIC is pretty useless," the documentation file that comes with the code says, "unless it is used in combination with 'Boosters.'" And that's putting it mildly—the attack code is generated based completely on what's in the booster file. When an attack is launched, HOIC compiles the booster to create the HTTP headers to be sent, and sets the mode of the attack.
After selecting the booster, it is ready for the attack, as we can see in the figure below.
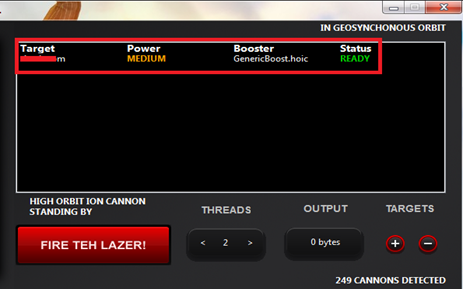
Now just click on "FIRE TEH LAZER" and wait for few minutes.
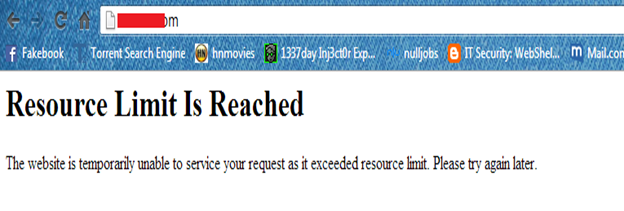
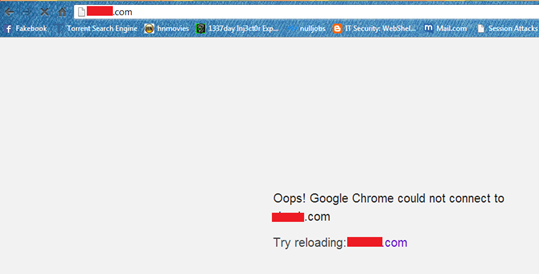
Now when you will open your target web page, you will see a message like the figure above. If you see the message "Resource Limit Is Reached", then it means the game is over.
PyLoris - It is a python based tool that works simultaneously on Linux and Windows platform. PyLoris also includes a feature called TOR Switcher, which allows attacks to be carried out over the anonymized Tor Network and switch between Tor "identities," changing the apparent location the attack is coming from at user-defined intervals. Before using this tool, it is required that TOR browser and Python is installed on the system. Now we can start the tutorial.
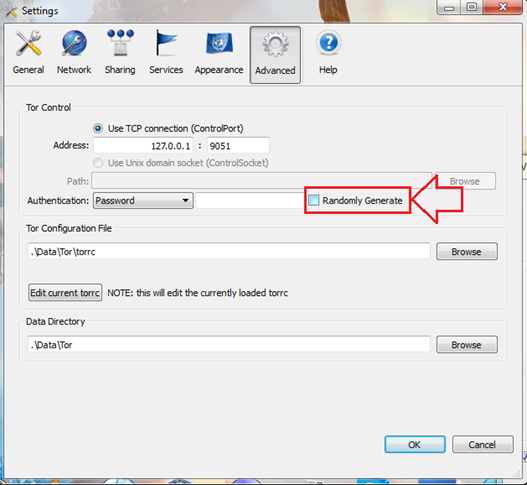
- First open Tor. In the Vidalia control panel, go to settings, then "Advanced", and from the drop down menu, choose password. Finally, deselect Randomly Generate.
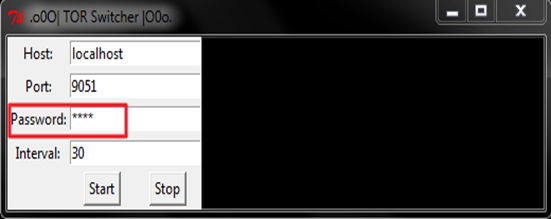
- Next, go to Pyloris folder and open the file Tor_Switcher.py and input the password you just set in Tor. You can lower the rate of interval if you want. If you are getting rejected connections, try lowering or raising the rate of interval.
- Leave Tor_Switcher.py running and open Pyloris.py. Configure it, by inputting your target website in the host under the general's menu. The port is usually 80. You can raise the limits depending on how fast your computer is. Once it's all set up, fire your laser, and click on the launch button.
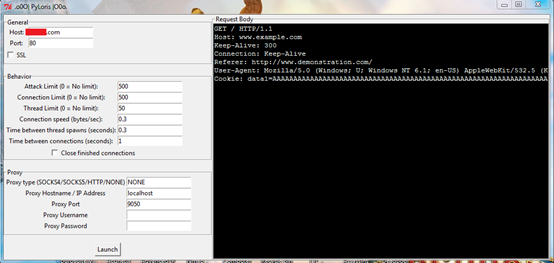
- After clicking the Launch button, a new window will pop up and will show the status of the attack. Please refer to the image.
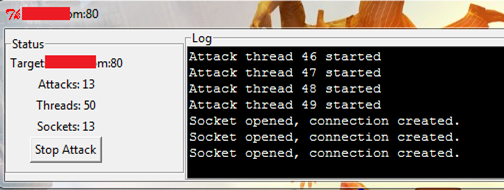
- It takes some time before all the target's sockets are filled, usually around 300 or so. Just wait and soon you will see that your target down.

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
Sources
High orbits and slowlorises understanding the anonymous attack tools