US Presidential Elections: Hackers - the Third Actor Between Contenders
Introduction
In February of this year, Director of National Intelligence James Clapper told Congress that intelligence officials were already seeing targeting of the 2016 presidential campaigns.
"We already have some indications of that," he explained during a discussion at the Bipartisan Policy Center in Washington. "I anticipate that as the campaign intensifies, we are probably going to have more of it."

Learn Windows 10 Host Security
The news is not surprising, and the fact that the US Director Clapper made a public announcement suggests that the US intelligence has already detected a surge in the number of cyber attacks against the organizations of the contenders.
The Department of Homeland Security and the FBI are issuing multiple warnings inviting politicians to assume a proper security posture and avoid being hacked.
"There is a long-standing practice of briefing each of the candidates once they are officially designated, and that shifts into a higher gear in terms of details after the president-elect is known," Clapper said.
Clapper admitted that the US intelligence gathered evidence of several hacking campaigns targeting the campaigns of presidential contenders. The official highlighted the different motivations of the attackers citing the risk of exposure to cyber espionage campaigns operated by nation-state actors, to hacktivism, and financially motivated hackers.
"We're aware that campaigns and related organizations and individuals are targeted by actors with a variety of motivations — from philosophical differences to espionage," said the FBI spokesman Brian Hale.
The official explained that government experts detected several different kinds of attacks, ranging "from defacements to intrusions." According to US Intelligence, its experts tracked intrusions by foreign intelligence services into the campaigns for president back in 2008.
According to Clapper, the two candidates would receive "exactly the same" briefings that will be filed to avoid any interference with the programs of the candidates.
"We've been doing this for many years, it's not designed to shape anybody's worldview," Clapper added.
Russian hackers target the Presidential Elections
In June 2015, the security firm CrowdStrike conducted a detailed analysis of a cyber attack suffered by the Democratic National Committee (DNS).
The experts from CrowdStrike discovered not one, but two hacker groups that it considers "some of the best adversaries out of the all the numerous nation-state" groups the company encounters daily, the COZY BEAR and the FANCY BEAR. According to the Washington Post, the Russian hackers managed to steal an entire database of opposition research on the presumptive Republican nominee for President Donald Trump.
The breach of DNC servers is just one of many in a long list of attacks against government and political organization around the world.
COZY BEAR and FANCY BEAR are no newcomers to the cyber arena, these ATPs are considered among the most dangerous persistent attackers and have been involved in numerous cyber espionage campaigns in the past. In 2015, it was discovered that COZY BEAR, a.k.a. CozyDuke, had been hidden in the US State Department's email server for nearly a year having some officials close to the investigation, claiming the breach was the "worst ever" cyber intrusion against a federal agency. The breach forced the State Department shut down much of its unclassified email system to rid itself of the pervasive malware and made for an unfortunate backdrop for the Secretary of State, Hillary Clinton, embroiled a politically charged debate over her personal email server.
In April 2015, experts at Kaspersky Lab revealed the existence of the CozyDuke ATP that targeted several high-profile organizations in the second half of 2014. Security experts discovered many the similarities between the operations conducted by the CozyDuke and other campaigns managed by the APT groups such as CosmicDuke, MiniDuke, and OnionDuke.
"CozyDuke is definitely connected to these two campaigns, as well as to the OnionDuke cyberespionage operation," explained Baumgartner, Principal Researcher at Kaspersky Lab's Global Research and Analysis Team "Every one of these threat actors continues to track their targets, and we believe their espionage tools are all created and managed by Russian-speakers."
The experts at Kaspersky haven't linked the CozyDuke to the Russian Government, but media agencies and many experts believe that the State Department and White House attacks were carried out by Russian hackers working for the Kremlin, which could also be the government behind these APTs.
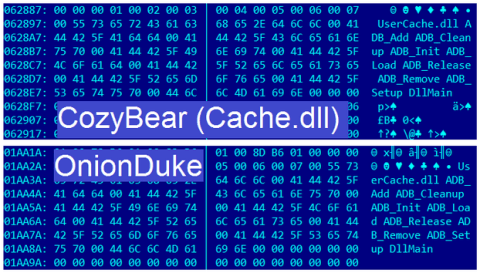
Figure 1 CozyBear code compared with OnionDuke code.
While CrowdStrike was making headlines with its breaking news, PaloAlto Networks was releasing its own report on FANCY BEAR, a.k.a. Sofacy APT, another well-known espionage group, believed to be Russian. According to the experts from PaloAlto Networks, spear phishing emails with weaponized attachments were being sent by a possible compromised server belonging to the Ministry of Foreign Affairs in an unidentified country. PaloAlto experts noticed that FANCY BEAR hackers are using source code from the infamous Carberp Trojan, a tactic they have already used in the past. Once infected, the victim's machine beacons to "google.com" to mask beacons to a C2 server hosted at 191.101.31.6.
The DNC hack doesn't surprise the experts, in the past other nation-state attackers hit politicians. In 2008, Chinese hackers compromised the computer networks of the Senators Barrack Obama and John McCain and later, in 2012, the hackers targeted the campaign networks of Obama as well as Mitt Romney.
Trump is considered a politician welcome to Russian authorities, Trump's fascination with Russia is not a mystery. Trump has made it no secret that he may be willing to rehabilitate the Putin's reputation on the world stage often saying,
"Wouldn't it be nice if actually we could get along with Russia." at many of his rallies.
Regardless of the political implications and fallout of the DNC breach, there is little doubt that Russian espionage actors most likely now have a comprehensive playbook on the DNC's strategy in defeating Trump in the November elections. How they use that playbook remains to be seen and many other questions about the breach remain unanswered.
Both COZY BEAR and FANCY BEAR groups are well coordinated, funded, and highly skilled in their tradecraft.
Were both groups acting alone, given the same target by their handlers, or were they acting in a coordinated effort on behalf of a single entity?
The reply is not simple, but security experts are aware that intelligence agencies rely on two or more hacker groups that are given overlapping objectives without any knowledge of each other.
"This scenario is likely, considering Russia's complex and often adversarial intelligence gathering operations as outlined in a recent paper released by the European Council on Foreign Relations (ECFR) titled, "Putin's hydra: Inside Russia's intelligence services." The paper describes a tangled web of bureaucrats, spies, law enforcement officers, and heads of military intelligence units all vying to please the Kremlin. The paper paints a grim picture of deceit, back stabbing, and one-upmanship that has weakened the intelligence community's ability to shape geopolitical strategy and policies,"
wrote the cyber security expert Rick Gamache.
DNC hackers' attack was deeper than previously thought
In June, the experts from CrowdStrike reported the security breach of the Democratic National Committee (DNS), but new evidence collected by investigators suggests DNC hackers accessed more information than previously thought.
The hackers that breached a Democratic National Committee consultant's personal Yahoo Mail account likely accessed private communications in the attempting to defeat Republican nominee Donald Trump.
Yahoo News confirmed the story, reporting that the DNC consultant Alexandra Chalupa received a notification warning from the Yahoo security experts that "strongly suspect that your account has been the target of state-sponsored actors."
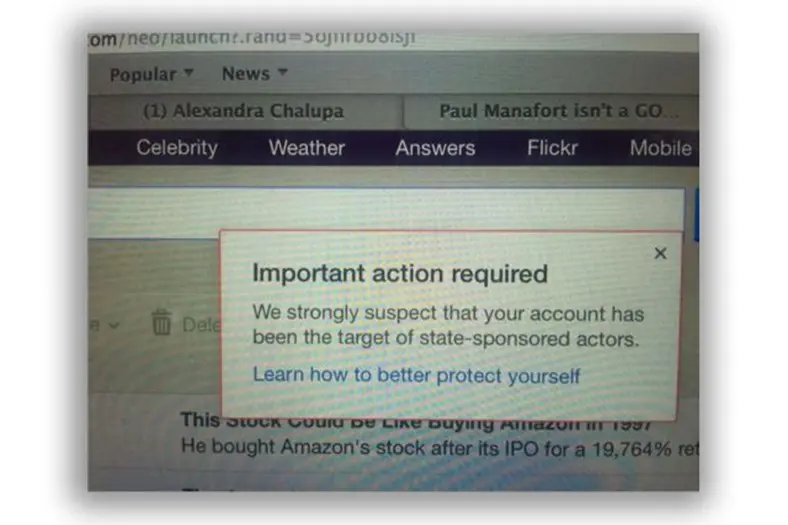
Figure 2 - DNC consultant Alexandra Chalupa received a notification warning from the Yahoo
A few weeks after the DNC officials announced the security breach alleged caused by Russian state-sponsored hackers more than 19,000 private DNC messages were leaked online by the WikiLeaks organization. The publishing of the messages led to the resignation of Chair Debra Wasserman Schultz.
Investigators believe hackers not only compromised DNC servers, the attacker likely compromised personal email account and stolen data from DNC officials' smartphones.
"But Chalupa's message, which had not been previously reported, stands out: It is the first indication that the reach of the hackers who penetrated the DNC has extended beyond the official email accounts of committee officials to include their private email and potentially the content on their smartphones," reported Yahoo. "After Chalupa sent the email to Miranda (which mentions that she had invited this reporter to a meeting with Ukrainian journalists in Washington), it triggered high-level concerns within the DNC, given the sensitive nature of her work." "That's when we knew it was the Russians," said a Democratic Party source who has knowledge of the internal probe into the hacked emails. To stem the damage, the source said, "we told her to stop her research."
"Two sources familiar with the breach said that the hackers' reach was far more widespread than initially thought and includes personal data about big party contributors and internal "vetting" evaluations that include embarrassing comments about their business dealings (as well as gossipy internal emails about the private affairs of DNC staffers)." continues the post published by Yahoo. "There are also signs that the hackers have penetrated the personal email of some Clinton campaign staffers—at least those who were in communication with senior DNC staff members."
How Wikileaks obtained the information from the alleged Russian hackers?
Media outlets speculate that the WikiLeaks founder Julian Assange has in the past hosted a talk show on RT, which is the Russian television network.
The Democratic Party organization continues to be under attack
Despite the news of the DNC, the hack is in the headlines; hackers continue to target the Democratic Party organization. Last week, experts discovered that the Democratic Party's congressional fundraising committee was hacked too.
According to the Reuters, the FBI is investigating a security breach of the systems of the Democratic Congressional Campaign Committee (DCCC).
"The FBI is investigating a cyber attack against another U.S. Democratic Party group, which may be related to an earlier hack against the Democratic National Committee, four people familiar with the matter told Reuters." states the Reuters. "The newly disclosed breach at the DCCC may have been intended to gather information about donors, rather than to steal money, the sources said on Thursday."
It is not clear what information has been accessed by hackers; it is likely they accessed donors' data including names, email addresses, and credit card details.
Visitors to the DCCC website were redirected to a bogus website mimicking the legitimate DCCC donation page, the IP address of the website resembled one used by Russian state-sponsored hackers allegedly involved in the breach of the DNC.
"That was when a bogus website was registered with a name closely resembling that of a main donation site connected to the DCCC. For some time, internet traffic associated with donations that was supposed to go to a company that processes campaign donations instead went to the bogus site, two sources said" continues the Reuters.
Disinformation and rumors on the DNC hack
While experts investigated the case, other actors appeared on the scene, such as Guccifer 2.0 and Detox Ransome. Who are they?
According to The Epoch Times, the notorious hacker Detox Ransome stole Democrat Databases in 2015. In September 2015, the hacker breached one of the services linked to the operations of the Democratic National Committee.
Detox Ransome accessed the database and stole user credentials, email and other data belonging people involved in the organizations connected to the Democratic National Committee (DNC).
The cyber security expert Edward Alexander provided to The Epoch Times evidence of the attack found on the dark web.
"I know he was sitting on those databases, I know he had them, and after he and I parted ways I'm sure he tried to monetize them somehow," Alexander said.
Detox Ransome was in the headlines in August 2015 when he hacked a server of the BitDefender security firm that hosted the cloud-based management dashboards for its small and medium-sized business clients. The hackers leaked a list of credentials for more than 250 BitDefender accounts, as reported by the HackerFilm.
He also threatened to leak more customer data unless the company paid $15,000.
Alexander was introduced to Detox Ransome by another notorious black hat hacker; Detox Ransome told him over an online chat that he had hacked a website containing data belonging "Obama and Hilary campaign people," the archive is a trove composed of "millions of emails."
Detox Ransome hacked the Rogue Global Solutions website that was operated by campaign staff of President Barack Obama "with the desire to bring the technical innovations of the campaign to other political, governmental, and international organizations."
Alexander tried to contact the Rogue Global Solutions, but he discovered that the site is no longer operative although the server containing the data was still online and open to hackers.
"We tried to alert Rogue Solutions, but that's when we found out they were no longer around and had folded up shop," Alexander said.
According to Alexander, Detox Ransome exploited the Heartbleed flaw to access the server that he found while he was scanning the web searching for vulnerable websites.
"The system contained more than 1GB of data in its databases that contained login credentials for key members of organizations and services connected to the DNC." reported The Epoch Times.
"When Detox Ransome was exfiltrating data from the networks of Rogue Global Solutions, he used a screen share program to show Alexander what he had found. Alexander recorded the session for evidence and had provided Epoch Times with the video."
The name of Detox Ransome isn't the unique one that was reported by the media in this period, a hacker using the pseudonymous Guccifer 2.0, claimed responsibility for the cyber-attack on the Democratic National Committee (DNC) too.
Shortly after the CrowdStrike's analysis was published online, a hacker going by the persona Guccifer 2.0, claimed responsibility for the DNC hack. Guccifer 2.0 is a play on a Romanian hacker calling himself Guccifer that hacked into Hillary Clinton's personal email server, compromising thousands of sensitive US State Department documents,
Guccifer 2.0 made his claims from his blog https://guccifer2.wordpress.com/2016/06/15/dnc/ ; he explained to be a lone hacker that is not linked to Russian Intelligence. The majority of security experts believes that Guccifer 2.0 is a character used for disinformation about the DNC hack.
"Worldwide known cyber security company CrowdStrike announced that the Democratic National Committee (DNC) servers had been hacked by "sophisticated" hacker groups.
I'm very pleased the company appreciated my skills so highly))) But in fact, it was easy, very easy.
Guccifer may have been the first one who penetrated Hillary Clinton's and other Democrats' mail servers. But he certainly wasn't the last. No wonder any other hacker could easily get access to the DNC's servers.
Shame on CrowdStrike: Do you think I've been in the DNC's networks for almost a year and saved only two documents? Do you really believe it?
Here are just a few docs from many thousands I extracted when hacking into DNC's network.
They mentioned a leaked database on Donald Trump. Did they mean this one?" Guffifer 2.0 wrote on his blog
As proof of the hack, the Guccifer 2.0 released several sensitive DNC documents including donor lists, strategy lists, and even a document titled "NATIONAL SECURITY TRANSITION PLANNING" detailing a timeline of activities of transitioning Secretary Hilary Clinton into the role of President after the November election.
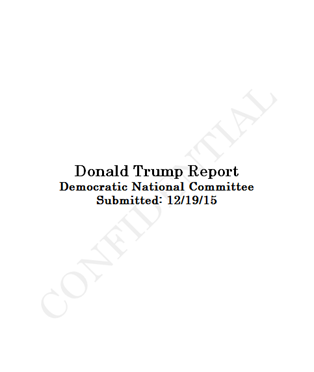
Figure 3 - Document published by Guccifer 2.0 ad a proof of the hack
Conclusion
The events raised the debate about the effective value of attribution and its accuracy.
There is no doubt that the DNC hack is likely going to be one of many cyber attacks in the coming months as we approach the elections later this year in November.
Whoever is behind the attack, the DNC hack demonstrates the potential influence of hackers on the politic of one of the most important governments of the world.
Once again, an attack from the immaterial cyberspace could have a severe impact on the event in the real world.
Back to the specific case, probably a good security posture of politicians could reduce their attack surface.
References
https://www.crowdstrike.com/blog/bears-midst-intrusion-democratic-national-committee/
http://securityaffairs.co/wordpress/49705/intelligence/dnc-hack.html
http://securityaffairs.co/wordpress/48428/cyber-crime/russian-hackers-spy-us-politics.html
http://securityaffairs.co/wordpress/47455/intelligence/hackers-target-presidential-contenders.html
http://securityaffairs.co/wordpress/49827/cyber-warfare-2/dccc-hacked.html
http://securityaffairs.co/wordpress/49811/breaking-news/democratic-national-committee.html
http://securityaffairs.co/wordpress/48475/intelligence/guccifer-2-0-lone-wolf-fancy-bear.html
http://securityaffairs.co/wordpress/47041/cyber-crime/guccifer-admits-hillary-clinton-hack.html
https://guccifer2.wordpress.com/2016/06/15/dnc/

Cybersecurity interview guide








