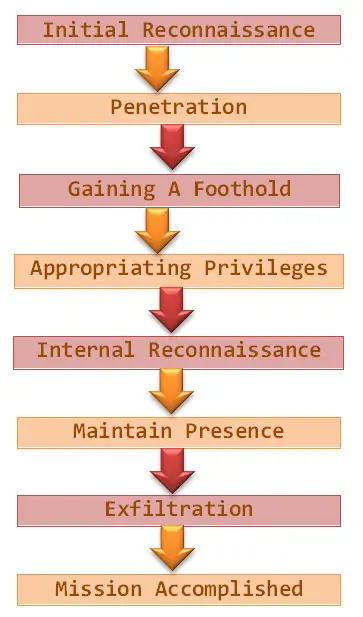
The cyber exploitation life cycle
For the purposes of this article, the term "cyber exploitation" will represent all the subversive activities that include interstate "breaking and entering" somebody else's computer and network. For further explaination on the subject, read the first part of my previous work "Cyber Exploitation".

Learn Secure Coding Fundamentals
The current contribution follows the progress of cyber exploitation process as an evolving occurrence, which like every similar act, has an inception, development, main activity/culmination, outcome, and eventually consequences. The act itself is split up into stages, and each one of them follows the natural course of these events as described above. Nevertheless, it worth mentioning that the stages in cyber exploitation may occur in different order.
This article is based on a figure titled "Mandiant's attack Lifecycle Model" posted on page 27 in "APT1Exposing One of China's Cyber Espionage Units" report. The model used here (the figure below "Life Cycle Stages of Cyber Exploitation"), however, has some modifications.
Initial reconnaissance
There is one significant difference between common cyber criminals and actors involved in cyber exploitation activities. The first group usually have no preferences considering the victim selection, disseminating freely malware across the Internet. In many cases, they employ passive attack in order to compromise computer systems and networks.
Passive attacks consist of analysing traffic, decrypting the unsophisticated traffic, monitoring weakly protected communications, and intercepting authentication information and credentials such as passwords. While it is disputable whether all these activities are always illegal, these attacks may capture victim's information (e.g. credit card number) without his consent. As a result, the data obtained can be used in various illicit activities (Schreier,2002).
On the other hand, the targets of cyber exploitation frequently are specifically attacked. As it may seem, these tactics and tools are not well suited for targeted attacks, especially against well-protected international corporations. However, it is not improbable for cyber criminals to direct their strikes at concrete individuals or organizations. Therefore, the different approaches can give us an insight into the perpetrator's intent.
Perhaps the most important fact to be noted when it comes to the initial reconnaissance phase is the attacker's aptitude for"exploiting of the human element" incorporated virtually everywhere where there is a human presence (Nolan & Levesque, 2005). For instance, attack planers may employ digital traces left behind by company employees into creating a seemingly trustworthy ways to manipulate the victim to execute the wanted action.
As a whole, the first reconnaissance consist of two basic layers: 1) Target Selection 2) Target Research. These two encompasses information gathering activities from sources such as social networking websites, internet search engines, conferences, lectures, academic material, underground repositories, etc., providing enough intelligence much needed to profile the targeted organization or person (Smith &Toppel, 2009). Furthermore, the planner could broaden the scope of the research, thus including branches, departments, subsidiaries/daughter companies, filiations, related companies, or even colleagues and associates—approaches a.k.a. horizontal, vertical, geographical exploitation opportunities (Deloitte, 2011).
Initial reconnaissance
Target selection & research
- Social networking websites
- Internet search engines
- Conferences
- Academia
- Illegal sources
- Horizontal exploitation opportunities
- Vertical exploitation opportunities
- Geographical opportunities
Additionally, before launching the cyber exploitation, hackers often conduct "quality-assurance" probes to decrease the numbers of anti-virus software which can detect the intrusion (Grow & Hosenball, 2011).
Regardless of the hacker's actual intention, whether to change, damage, delete, or just to steal data, the next and most difficult step is getting inside. For this reason, the first stages of both cyber exploitation and cyber attack are more or less identical (Schreier, 2011).
Penetration
This stage represents the methods intruders use to compromise the targeted organization's network. Although there are other ways, such as software updates mostly for system files, containing deeply buried trojans (Kak, 2012), the most prominent technique is spear phishing. This method uses e-mail massages targeting specific individuals as high ranked employees. These e-mails frequently look normal, and the sender or subject even may seem familiar to the recipient. According to the content of these corrupt e-mails, the spear phishing is divided into:
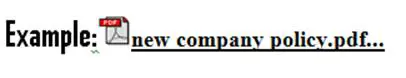
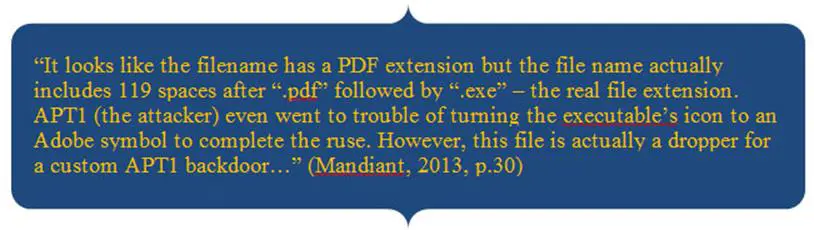
Spear phishing (malicious attachment) —Contextually meaningful messages with attachments like PDF (see the example below) or DOC files, which, once executed, create back doors that initiates stealthy line of connection between the infected computer and a control server(Information Warfare Monitor & Shadowserver Foundation, 2010).
Spear phishing (malicious link) — the e-mail may contain a link leading to a malicious file (Mandiant, 2013).
Spear phishing (malicious website) — Web compromise is another common tactic in which the attacker will be able to exploit numerous infection vectors. The exploiter may devise web pages, containing "drive by" exploit code that will compromise the visitor's computer system if vulnerable to this exploit code (Information Warfare Monitor & Shadowserver Foundation, 2010). Another option at hand is uploading webshells to vulnerable Internet-facing web servers which would grant access to the targeted internal network (Mandiant, 2013).
Given the importance of the secrecy factor, the intruders utilize a number of ways to disguise their moves:
Gaining A Foothold
Gaining a foothold is important because it ensures that the intruder has complete access and control over the victim's computer. In order to establish firm presence, he has to set up a backdoor and create command and control infrastructure.A backdoor is a program feature allowing a remote execution of numerous arbitrary commands—useful tool for assuming control of targeted computers.
Types of backdoor software
A person may acquire such software through different ways. Gh0st RAT and Poison Ivy are common instances of public backdoors, whereas hacker community and websites may prove useful source for "underground" backdoors (Mandiant, 2013).
If the person who wants to conduct cyber exploitation is skilful enough, he could create custom-made backdoor software. Of course, a 0-day vulnerability would be the utmost achievement in this department. However, writing such programs requires the skills of the most advanced programmers, having substantial resources and superior IT knowledge.
The passive backdoors are more persistent mechanisms. The traditional network traffic analysis tools and standard forensic techniques will not always succeed in finding them.As a result they may remain undetected for a very long time. First of all, they "do not always use traditional persistence mechanisms, and they are frequently deployed outside of the known attackpath (Surdu, 2012, p. 4)." Furthermore, this sort of backdoor does not generate network traffic, because they do not initiate network connections. They just sit idly, hidden from victim's attention, until the attacker decides to connect to them. Web shells and port listeners are two examples of passive backdoors.
Covert connections
The purpose of the backdoor software is to establish outbound connection from the victim's network to the attacker's "command and control" server or another computer in control. The methods of communication may vary—plain text, simple encoding, or sophisticated encryption. In some cases, a backdoor may attempt to mimic the legitimate Internet traffic different than an HTTP protocol (Mandiant, 2013). Hence, the malware may utilize a protocol for standard web traffic (HTTP) in order to blend into the regular network activity as if was part of routine Internet browsing (Information Warfare Monitor, 2009).
Appropriating privileges
Obtaining somebody else's privileges is one of the options which the intruder has at disposal once he has managed to pave the foundation stone of his stealthy presence. Obtaining usernames and passwords are most desirable, but acquiring access to privileged computers, VPN costumer software, or PKI certificates might be also a tempting alternative (Mandiant, 2013).
Sometimes stealing usernames/passwords could be the leading motive for the perpetrators, or these items might come along with the other acquisitions. Reportedly, "between April and October, hackers successfully stole 50 megabytes of email messages and attached documents, as well as a complete list of usernames and passwords from an unspecified (U.S. government) agency (Grow & Hosenball, 2011, p.4)."
Passwords can be retrieved from password hashes. In a nutshell, password hashes are unique values generated through mathematical algorithms with which the system can refer to a specific password. Basically, the hacker can either try to hack orcrack the password hash in order to steal the original password or use the entire hash (execute "passing-the-hash" operation) to get access (Mandiant, 2013).
Once the hacker succeed in fooling the system that he has the rights of systems administrators, he may further continue to explore other computers from the same network and even lay hands on privileges that other users enjoy (Schreier, 2011).
Internal reconnaissance
Following the cycle of cyber exploitation, after the initial reconnaissance, the penetration, the solid malware establishment, and escalating privileges to (unlimited) access, the next step is conducting internal exploration of the infected system.
At this stage, the purpose is to collect more information regarding the system's internal environment The attacker may execute commands to inquire the system information, thus getting to know the current network connections, programs installed, list of recent documents, and hardware statistics (Information Warfare Monitor, 2009).
Supposedly, data of interest may have many forms and be in various places, but primarily encompass sensitive files and documents, databases, or contents of e-mail accounts which are stashed in files or e-mail servers and domain controllers (Mandiant, 2013).
Lateral movement
In addition, it is possible the compromised computer to does not contain the targeted data. In these situations, the attacker has one extra ace up his sleeve. He may further expand the process of exploitation to other computers within the same network -- the so called "lateral movement". Already gained, credentials and privileges could provide new such (Mandiant, 2013).
Eventually, the process may spill further:
With each successful infection the attacker(s) may use any contextually relevant data to further exploit the targeted community and may also impersonate the initial target in order to infect all the targets' contacts. Finally, the targets themselves may infect others by forwarding infected documents to their contacts. In this way, the network of infected computers grows organically.(Information Warfare Monitor, 2009, p.39)
Maintain presence
In this stage, the exploiter aspires to ensure prolonged presence and control from outside over key systems components within the network environment of the targeted object. For attaining this goal, three methods may be in use:
- Installation of additional backdoor malware—Simply put, more malware, easier access. Besides, if the existing backdoors are discovered-deleted, the newly planted will keep the continuation of the cyber exploitation process intact.
- Usage of legitimate credentials—Valid VPN or PKI credential would allow the intruder to disguise as a legitimate user, gaining access to the targeted corporate network and internal resources.
- Log into web portals— Having stolen credentials, exploiter can also use them to log into web portals existing within the same network (e.g. web-based e-mails such as Outlook Web Access or restricted websites) (Mandiant, 2013).
The malicious code frequently is polymorphic, it alters shape every time when it is executed, and as to avoid discovery, burrows deep into computer networks (Grow & Hosenball, 2011). Cyber exploitation is persistent because of its clandestine nature, and rarely neither the malware nor the intruder's actions are detected. Moreover, "they are challenging to detect and combat because they can covertly embed themselves into your environment and establish a way to come back later, to steal additional data, to remain undetected by their victim (Deloitte, 2011)."
Exfiltration
Attaining valuable data such as intellectual property, know-how, classified military projects, policy documents and corporate memoranda, business dealings, contracts, etc. is the primary aim of cyber exploitation. The exploited data has its own life cycle: Localization>Packing>Sending. To further explain, after the sensitive info is located, is packed, most commonly via RAR archiving, but other options like ZIP, 7-ZIP, or CAB are also plausible. The compressed file could be split up into chunks, and/or encoded, as to draw less attention, and then is sent via FileTransfer Protocol or the existing backdoors (Mandiant, 2013).
Cyber exploitation acts do not have for a purpose causing harm to the victim's network infrastructure. If we are willing for a moment to adopt the "extraversion-introversion" psychological theory by Carl Jung, the cyber exploitation bears clandestine nature and ulterior motive that benefit from concealing, consequently the introversion behaviour is predominant. The ultimate goal is attained by stealing sensitive data. However, the negative impact may come later, after the stolen information is used (Deloitte, 2011).
Once the data is transferred to exploiter's system, then the final point of cyber exploitation life-cycle is reached:
Mission Accomplished
Conclusion
This contribution follows the cyber exploitation "lifetime" from the moment the idea and plan is conceived, throughout its execution in practice, to the final result. In this regard, the step-by-step frame gives the reader a chance to comprehend some of the essential features characteristic for these events. These distinguishing marks can be extracted even from the alternative denomination of the cyber exploitation term, namely, "advanced persistent threat."
Advanced— underscores the sophistication of the threat, in terms of technology and application.
Persistent— functions as a twofold implication modus, giving a hint for the longevity of the process, as well as its resistance to remediation.
Threat—signifies the self-evident nature of cyber exploitation acts.
However, as it has been written before, these acts do not lead directly to damaging consequences, hence they are not cyber attacks. One must be able to set the line of demarcation in order to know what he is dealing with. Consequently, if we have better understanding about the nature of the particular act, cyber exploitation in this case, learn more about the process of evolvement in detail, then we have better chance to avoid great deal of problems which entail the theft of valuable data.

Learn Container Security
Sources
- Brian Grow and Mark Hosenball, (2009). In Cyberspy vs. Cyberspy, China has the edge.
- Deloitte, (2011). Cyber Espionage The harsh reality of advanced security threats.
- Information Warfare Monitor, (2009). Tracking GhostNet: Investigating a Cyber Espionage Network.
- Information Warfare Monitor & Shadowserver Foundation (2010). Shadows In The Cloud: Investigating Cyber Espionage 2.0, Joint Report: Information Warfare Monitor Shadowserver Foundation.
- Kak, A. (2012). Mounting Targeted Attacks with Trojans and Social Engineering — Cyber Espionage.
- Mandiant, (2013).APT1Exposing One of China's Cyber Espionage Units.
- Markoff, J. & Barboza, D.(2010).2 China Schools Said to Be Tied to Online Attacks.
- Nolan, J. & Levesque M.,(2005). Hacking human: data-archaeology and surveillance in social networks.
- Schreier,F. (2011).On Cyberwarfare.
- Smith, A. M., & Toppel, N. Y. (2009). Case study: Using security awareness to combat the advanced persistent threat. Paper presented at the 13th Colloquium for Information Systems Security Education (CISSE), University of Alaska. Fairbanks, Seattle.
- Surdu, S. (2012). An Evolving Threat: Trends in cyber espionage, financial crime and advanced targeted attacks.







