SS7 protocol: How hackers might find you
The Signalling System No 7 (SS7), also known as Common Channel Signalling System 7 (CCSS7) or Common Channel Interoffice Signaling 7 (CCIS7), is a set of protocols developed in 1975 that allows the connections of one mobile phone network to another. The information passed from a network to another are needed for routing calls and text messages between several networks.
The SS7 performs out-of-band signaling in support of the call establishment, billing, routing, and information exchange functions of the public switched telephone network (PSTN).

Learn Container Security
When users access a PSTN, he constantly exchanges signaling with network elements, for example, signaling information are exchanged between a mobile user and the telephone network.
Information includes dialing digits, providing dial tone, sending a call-waiting tone, accessing a voice mailbox, etc.
The term Out-of-band signaling is used to specify that signaling that does not take place over the same path as the conversation. The digital channel used for the exchange of a signaling information is called signaling link, when a call is placed, the dialed digits, trunk selected, and other information is sent between switches using their signaling links, rather than the trunks used to carry the conversation.
Out-of-band signaling has the following advantages:
- It allows for the transport of more data at higher.
- It allows for signaling at any time in the entire duration of the conversation, not only at the beginning of the call.
- It enables signaling to network elements to which there is no direct trunk connection.
The SS7 is also used to implement the network roaming when users need to use different network providers.
A hacker accessing the SS7 system can snoop target users, locate them, and transparently forward calls.
The access to the SS7 system is possible by using any number of networks.
In response to the disclosure of security issues related to the SS7 protocol, telco bodies, and operators, including the GSMA, have introduced monitoring services to prevent intrusions or abuse.
Recently a group of hackers demonstrated how spy on mobile users simply using their phone numbers; they have chosen as a target complacent US Congressman.
The group is led by the popular German security expert Karsten Nohl; the researchers demonstrated they were able to eavesdrop and geographic track the politician just knowing his phone number.
There is nothing new in the revelation because the telco community was aware of the technique adopted by security experts, the same team illustrated in the past the technique that exploits security flaws in the Signalling System No. 7, also known as an SS7 protocol.
An attacker can exploit security issued in the SS7 protocol to spy on private phone calls, record them and monitor target's movements.
The US Representative Ted Lieu authorized the researchers to demonstrate that we are all vulnerable, then he shared the findings with the broadcast Sunday night by 60 Minutes.
"First it's really creepy," the US Representative said. "And second it makes me angry. They could hear any call. Pretty much anyone has a cell phone. It could be stock trades you want someone to execute. It could be a call with a bank."
One year ago, hacking SS7
Exactly one year ago, Channel Nine's 60 Minutes reported the existence of a security hole in modern telecommunication systems that could be exploited by cybercriminals to listen in on phone conversations and read text messages.
Karsten Nohl and his team investigated the presence of security flaws in the SS7 system back in 2014.
In that occasion, Nohl and his colleagues were able to intercept data and geo-track every mobile user by exploiting a flaw in the SS7 signaling system.
<iframe width="640" height="360" src="https://www.youtube.com/embed/GeCkO0fWWqc" frameborder="0" allowfullscreen></iframe>
In December 2014, a group of German researchers at the Chaos Communication Hacker Congress revealed the existence of serious security issues in the protocol used by a large number of carriers of mobile telephony. Despite the huge investment in security made by telco companies, the adoption of flawed protocols exposes customers to serious privacy and security risks.
"It's like you secure the front door of the house, but the back door is wide open," said Tobias Engel, one of the German researchers.
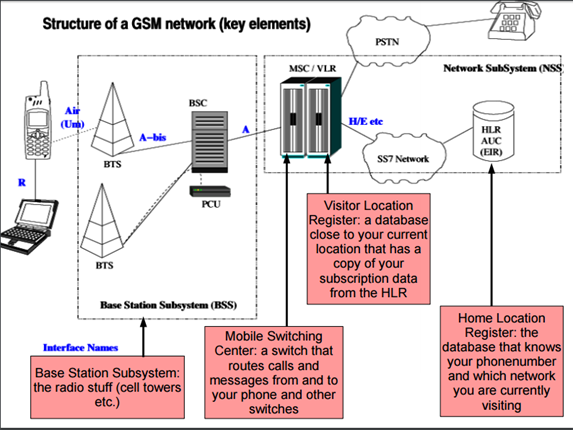
Figure 1 - Tobias Engel Slides presented at CCC Berlin
What does the network know about your location?
Tobias explained that the network knows the location of the cell tower that could be used to have a pretty good approximation of a user's location. Despite the access to the information managed by operators is restricted to the technical operation of the network, voice calls, and short messages can be initiated to your phone number from almost anywhere in the global SS7 network.
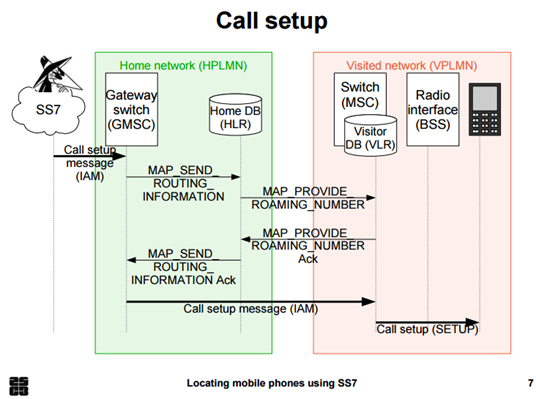
Figure 2 - Tobias Engel Slides presented at CCC Berlin
Below the presentation made by the expert Tobias Engel:
<iframe width="640" height="360" src="https://www.youtube.com/embed/lQ0I5tl0YLY" frameborder="0" allowfullscreen></iframe>
Attacks relying on these security issues already happened in the past, one of the major incidents was registered by the NKRZI (which is the National Commission for the State Regulation of Communications and Informatization in Ukraine) and involved Russian addresses back in April 2014.
The expert noticed that many Ukrainian mobile phone holders have been targeted by SS7 packets sent from Russia to track them and steal information from the mobile devices.
According to the security firm AdaptiveMobile who analyzed the case, a number of Ukrainian mobile subscribers "were affected by suspicious/custom SS7 packets from telecom network elements with Russian addresses over a three day period in April 2014. The packets were revealing the subscribers location and potentially the contents of their phone calls to be obtained."
A series of SS7 packets were sent to the MTS Ukraine's SS7 network that caused the modification of the control information stored in network switches for several MTS Ukraine mobile users. The effect was that one of the affected MTS used tried to call someone else, their call would be forwarded to a physical land line number in St. Petersburg, Russia allowing the interception of the communication.
"In the document, the investigation stated that the custom SS7 packets themselves came from links allocated to MTS Russia, the parent company of MTS Ukraine. The Ukrainian regulator then assigned responsibility for the nodes that generated the SS7 based on the origination addresses in the SS7 packets received. According to the report, some of the SS7 source addresses that originated the attack were assigned to MTS Russia, while others were assigned to Rostov Cellular Communications." stated the AdaptiveMobile.
The incident was not isolated, other cases were observed in different countries, let's consider for example that the same protocol is being used by major Australian providers, this means that Aussies data could be exposed to hackers. Names, addresses, bank account details and medical data stolen due to a security vulnerability that could give hackers the access to their mobile devices.
Another case was reported by the Guardian that revealed security tests conducted by an operator in Luxembourg took Norway's largest network operator Norway offline for over three hours due to an "unexpected external SS7 event."
A preliminary report issued by Telenor states the problem was caused by the reception of "unusual signaling" from another international operator into their networks. Software from Ericsson misinterpreted this very rare signaling messages stopping parts of mobile traffic up.
Ericsson identified how the misperception of signaling occurred and applied the necessary correction to fix the issue.
The reality is that old and insecure protocols could harm our privacy dramatically enlarging our surface of attack.
"Everything about our lives is contained in the palm of our hand," reporter Ross Coulthart said. 'Your sensitive, private data is opened for anyone to see. You could be bugged, tracked and hacked from anywhere in the world. It's long been the dirty little secret of international espionage. What it means is that your smartphone is an open book."
On the TV show, Mr. Coulthart was speaking from Germany with the Independent senator Nick Xenophon, who was located in the Parliament House in Canberra at the time of the phone call.
With the support of the German hacker Luca Melette, Mr. Coulthart demonstrated how to track its interlocutor by exploiting the security issue into the SS7.
Figure 3- 60 Minutes TV Show
"What if I could tell you senator, that it's possible to listen in to any mobile phone from anywhere in the world – would you believe me?'" Mr. Coulthart asked Mr. Xenophon while Melette heard the conversation.
"I find it very hard to believe." replied the incredulous Mr. Xenophon.
Mr. Coulhart then asked the senator for consent to record the phone call.
"But if you reckon they can pull it off, I give my consent, but I find this incredibly hard to believe." responded Mr. Xenophon.
The reporter also intimated to Mr. Xenophon that the hackers could intercept his text messages, but once again he skeptical immediately sent the following text message:
"Hi Ross, I don't believe you!! Nick."
The senator was shocked by the live demo provided by the reporter and the hacker.
"This is actually quite shocking because this affects every Australia," Mr. Xenophon said. "It means anyone with a mobile phone can be hacked, can be bugged – it's just chilling. This is the end of anyone's privacy as we know it." 'This is not about spies or terrorists and pollies – this is about every Australian that is vulnerable because their phones can be hacked."
The article published by the Washington Post confirmed the great interest in surveillance technology that could allow intelligence agencies, cyber criminals, and private actors to track individuals anywhere in the world and spy on their communications.
"The tracking technology takes advantage of the lax security of SS7, a global network that cellular carriers use to communicate with one another when directing calls, texts and Internet data." reports the Washington Post.
The SS7 protocol allows cell phone carriers to collect location data related to the user's device from cell phone towers and share it with other carriers; this means that exploiting the SS7 a carrier can discover the position of its customer everywhere he is.
"The system was built decades ago when only a few large carriers controlled the bulk of global phone traffic. Now thousands of companies useSS7 to provide services to billions of phones and other mobile devices, security experts say," explains the post.
"All of these companies have access to the network and can send queries to other companies on the SS7 system, making the entire network more vulnerable to exploitation. Any one of these companies could share its access with others, including makers of surveillance systems." continues the Washington post.
The use of trackers based on the exploitation of the SS7 protocol is usually associated with another category of surveillance devices that we have analyzed in detail in the past, the "IMSI catchers."
StingRays are common surveillance devices that allow can intercept calls and Internet traffic, send fake texts, install malware on a phone, and of course find the precise location of the victim.
"What's interesting about this story is not that the cell phone system can track your location worldwide,""That makes sense; the system has to know where you are. What's interesting about this story is that anyone can do it." said the popular expert Bruce Schneier.
The Washington Post made explicit reference to a 24-page marketing brochure for the cellular tracking system sold by Verint codenamed SkyLock. The document, dated January 2013 and labeled "Commercially Confidential," reveals the system offered to government agencies as "a cost-effective, new approach to obtaining global location information concerning known targets."
[download]Download the BEST PRACTICES FOR DEVELOPING AN ENGAGING SECURITY AWARENESS PROGRAM whitepaper[/download]
"The key to these surveillance systems is the SS7 network, sometimes described as a private Internet service for cellular carriers. Though it is used by carriers to route calls and other services, there are thousands of companies with access to the SS7 network, which is decades old and easily exploited for surveillance and other purposes," states the document.
"Some customers will already have access to the SS7 network through, for example, a monopoly carrier with close ties to a government and its intelligence service. But for other customers, Verint provides access to the network and the location data stored on it."
The brochure includes screen shots of maps depicting location tracking in what appears to be Mexico, Nigeria, South Africa, Brazil, Congo, the United Arab Emirates, Zimbabwe and several other countries
As said by Eric King, deputy director of Privacy International:
"Any tin-pot dictator with enough money to buy the system could spy on people anywhere in the world," "This is a huge problem."
Mobile localization with SS7
Each mobile phone service provider supplies the localization information within the Initial Address Message (IAM) field of the ISDN User Part (ISUP) protocol from the SS7 frame using a proprietary format. This means that to gather the information it is essential to know the way the ISP manages it.
The Integrated Services Digital Network User Part (ISUP) is an extension of SS7 that is used to set up wired connections between exchanges. The ISUP is the protocol used to support the signaling necessary to provide voice and non-voice services in telephone communications.
The SS7 localization data is sent using the 'Cell ID' attribute in the ISUP protocol, in the IAM message, "Location number" field and "Called number address" field.
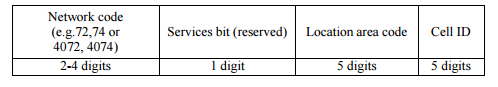
Figure 4 - Localization data format. (V. Cazacu, L. Cobârzan, D. Robu, F. Sandu)
The above information is stored by a mobile operator in a database alongside with geographic information that can be used to store the caller position based on the positioning string.
There are many malicious entry points to an SS7 network that could be exploited by hackers, including any unsecure operator, a Network Element OAM interface exposed on the Internet or a compromised Femto Cell.
The tracking user location depends on non-filtered MAP messages (e.g. SRISM / SRI, PSI, PSL, ATI) and the accuracy is a function of the type of messages allowed by the operators.
For example, the access to the CellID could allow an attacker to identify the position in a Street, meanwhile using the MSC GT the accuracy is related to a city area or a Region.
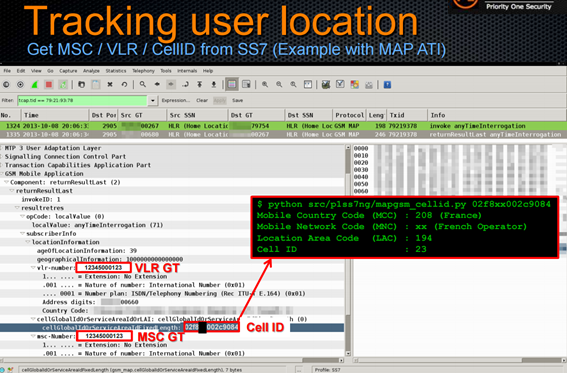
Figure 5 - Tracking users location with CELL ID (P1 Security – Hackito Ergo Sum)
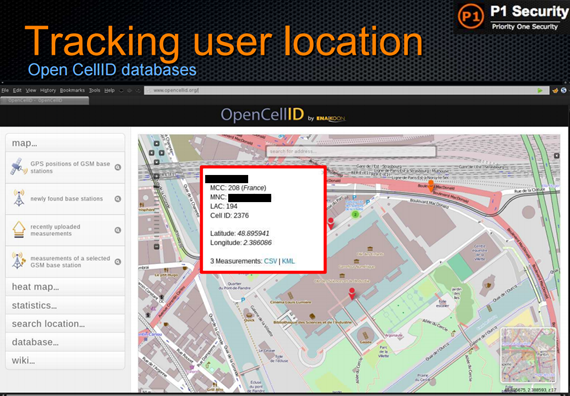
Figure 6 - Tracking users location with CELL ID (P1 Security – Hackito Ergo Sum)
Impact of SS7 adoption
The SS7 is widely adopted; it is currently used by more than 800 telecommunication companies around the world.
The SS7 protocol allows cell phone carriers to collect location data related to the user's device from cell phone towers and share it with other carriers. By exploiting the SS7, a carrier can discover the position of its customer everywhere he is.
Besides allowing telecommunication companies to query the location of phones on other carriers' networks, the SS7 protocol allows them to route calls and text messages through a proxy before reaching the legitimate destination. Of course, the features implemented by a proxy could allow an attacker to spoof the identity of the victims.
"The flaws, to be reported at a hacker conference in Hamburg this month, are the latest evidence of widespread insecurity on SS7, the global network that allows the world's cellular carriers to route calls, texts, and other services to each other. Experts say it's increasingly clear that SS7, first designed in the 1980s, is riddled with serious vulnerabilities that undermine the privacy of the world's billions of cellular customers.
The flaws discovered by the German researchers are actually functions built into SS7 for other purposes – such as keeping calls connected as users speed down highways, switching from cell tower to cell tower – that hackers can repurpose for surveillance because of the lax security on the network." reports The Washington Post.
A hacker can access the network might access a wealth of subscriber's information.
The SS7 protocol is also used by telecommunication companies to offer a number of services to various industries. For example, telecommunication companies use the SS7 to offer banks a service that allows them to confirm the presence of a customer's phone in a specific country to authorize its transaction avoiding fraudulent activities.
"As long as you have SS7 access, it's extremely easy," Les Goldsmith, a researcher from security firm ESD explained to Ars. "Any one of the telcos that has a roaming agreement with the target network can access the phone." Goldsmith presented his study on the SS7 security at the last RSA conference in San Francisco.
Conclusions
The majority of the telecommunication companies intends to replace the SS7 protocol for more secure one, the Diameter, but they will maintain the backward-compatibility with the SS7 continuing to expose mobile users to the risk of a hack.
According to 60 Minutes, intelligence agencies like the NSA exploit the SS7 protocol for their surveillance activities.
Lieu sharply criticized US agencies that may have turned a blind eye to such vulnerabilities.
"The people who knew about this flaw should be fired," he said. "You cannot have 300 and some million Americans, and really the global citizenry, be at risk of having their phone conversations intercepted with a known flaw simply because some intelligence agencies might get some data. That is not acceptable."
The attack scenarios illustrated are worrying and open the door to massive surveillance activities. Months ago the American Civil Liberties Union (ACLU) has also warned people against possible abuse of such vulnerabilities by intelligence agencies and law enforcement.
"Don't use the telephone service provided by the phone company for voice. The voice channel they offer is not secure," principal technologist Christopher Soghoian told Gizmodo. "If you want to make phone calls to loved ones or colleagues and you want them to be secure, use third-party tools. You can use FaceTime, which is built into any iPhone, or Signal, which you can download from the app store. These allow you to have secure communication on an insecure channel."
Unfortunately, the vulnerabilities into SS7 protocol will continue to be present, even as cellular carriers upgrade to advanced 3G technology to avoid eavesdropping.
Users are totally vulnerable to surveillance operations that rely on the exploitation of flaws in the SS7 system.
Users can avoid sending SMS and instead use encrypted messaging services such as WhatsApp. In a similar way, users can make calls by using voice over IP services avoiding carries voice network.

Learn Windows 10 Host Security
Sources
- SS7 protocol surveillance
- SS7 flaw surveillance
- SS7 attacks ukraine
- Flaws SS7 protocol spy on phone
- Surveillance solutions
- Hackers access call message send world moment
- SS7 hack explained
- Intro to SS7 Tutorial
- Intro computer nets
- Invasive phone tracking
- Phone hacking
- German researchers discover a flaw
- Locating mobile phones
- Worldwide attacks on SS7 network
- For sale systems that can secretly track where cellphone users go around the globe
- Russia Ukraine telecom monitoring
- Skylock product description
- Acta Emeng








