Preparing for a successful IAM integration project (Part 2 of 2)

Iteration-Based Delivery

What should you learn next?
As mentioned before, an identity management implementation project will often extend 18-36 months based on the size and complexity of the organization. This is an extraordinary amount of time for any project sponsor to maintain passion around the project. The answer is iterations of value statements which deliver highest values first while bringing the organization updates as to where the remaining items will be coming.
Being human, we love instant satisfaction. In business, many people demand that level of velocity simply because they don't have time for less. Creating smart, valuable and achievable iterations of your identity management implementation allows you to be in front of your stakeholders and users more often, delivering their value they asked for or explaining when they will see it while they see value others are currently enjoying.
Don't forget to include an open and methodical method to create your iterations so one business unit doesn't feel left out. Often, the emotion of a particularly bothersome manual task overpowers the logical understanding of delivery of a feature which saves the business more money. You can stem this off by using a simple stack ranking matrix (see Image 1) that allows all business unit stakeholders and project members to vote on what value statements are most important. Using defined analytics removes the emotions and maintains the team synergy.
Evangelization
If possible, I would have listed this under every single other heading before, during and after your IAM project. Evangelization is what brings the project home to the users. Before and after each iteration and stage, your evangelization engine should be revving in 5th gear.
As you are ready to start an iteration, revisit with your stakeholders to make sure that you didn't miss anything before things begin and they remember their expectations. Reviewing your current backlog of remaining items at this time is a great practice. Follow up after the iteration release to see if it met their expectations. Ask what could have been done better; praises will come freely however criticism must often be solicited. You need the critical opinions to correct your trajectory for future iterations so that you keep you project team engaged for the length of the implementation.
Simply put, keeping your organization knowledgeable and forewarned is the key lynchpin that holds together the rest of your project. Identity cannot be brought in "under the radar" like a new project planning system or CRM application. By it's very nature, identity is the forefront, presented before every employee, contractor and vendor in your organization.
Resistance can be passive in not accomplishing pre-planning tasks around workflows and access requests. Even worse, it can be overt with a powerful team publicly announcing that they won't be conforming with the new system. Either can lead to a snowballing impact strong enough to stall the staunchest sponsors goals.
Yes, everyone knows that communication wins the game. The question remains: are you prepared for that level of communication before you start?
Until the next time,
Hammer
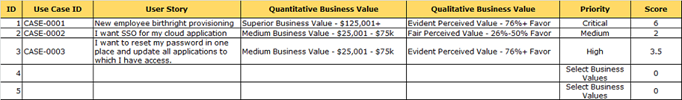
Image 1 - Requirements/Use Case Ranking Matrix
You can download this template here: http://preview.tinyurl.com/lf4kmlr
This article was originally posted on the Identropy Blog: http://blog.identropy.com/IAM-blog/bid/111258/Preparing-for-a-successful-IAM-integration-project-Part-2-of-2
Get your guide to the top-paying certifications
With more than 448,000 U.S. cybersecurity job openings annually, get answers to all your cybersecurity salary questions with our free ebook!