Physical security: Managing the intruder
No information security guide is complete without a chapter about securing physical access to information resources. After all, physical access gives even the moderately skilled attacker access to the network, unencrypted workstations and servers, and hardcopy information just waiting for someone to come by and pick it up. Have you looked at the output bin on your shared fax machines and printers, lately?
Physical security does include more than stopping human intruders. However, information on heating, cooling, fire suppression systems, and power backup is available simply by discussing your needs with your facilities management staff. It is not so easy when it comes to intrusion controls. It takes more than a lock or two to secure sensitive information and critical systems. This is the realm of the security professional's expertise.

Learn Secure Coding Fundamentals
In this chapter, we look at the objectives of physical security and various controls to meet those objectives. When you finish, you will have the skills necessary to have an informed discussion with facilities and business management about what is right and what is missing in your organization's physical security plan.
What is physical security?
The best definition I could find for physical security is available from the United States Geological Survey:
There is no object so well protected that it cannot be stolen, damaged, destroyed, or observed by unauthorized individuals. A balanced security system provides protection against a defined set of threats by informing the user of attempted intrusions and providing resistance to the would-be intruder's attack paths (USGS, 2005, p. 12)
The first part of this definition is common to all security efforts; we cannot stop a highly motivated attacker. It is in the second sentence of our definition that we find the objectives of physical security. Said another way, the purpose of physical security is to delay an intruder's advance toward a target long enough to detect and respond with human intervention. Human intervention includes on-site security guards, police, or other relevant human controls.
Achieving physical security objectives requires policies, standards, guidelines, and controls addressing prevention, detection, delay, response, and assessment. We identify gaps with physical security risk assessments and surveys, similar to those used for logical security. Through all physical security planning, we must remember one very important principle: ensuring human safety is the most important outcome.
Motive, opportunity, and means
The same things drive physical intruders that drive cyber criminals: motives like money, advancement of a social agenda, etc. Further, intruders seek opportunities that do not exceed their ability (means) to exploit. Finally, controls help mitigate opportunities, increase required skills, and mitigate the business impact resulting from a successful intrusion. All of this leads us back to the risk formula we examined in Chapter 2:

Figure 13- 1: Expanded Risk Formula
The basic principles of assessing and managing risk are the same for physical security as for configuring logical controls in the data center. Only the processes and controls differ.
Risk assessment
Because we base all security controls on risk, the first step in a physical security program is the risk assessment: sometimes called a physical security survey. Like the logical risk assessment described in Chapter 2, the physical security risk assessment identifies threats, pairs them with vulnerabilities, and determines the probability of successful attacks. Using best practice recommendations, the organization implements reasonable and appropriate controls intended to deter, delay, detect, and detain human intruders.
For additional guidance on the details of physical security survey/assessment tasks and expected results, see the U.S. Army and U.S.G.S references at the end of this chapter.
Physical security controls
Layered security also applies to physical security. Each layer supports others to prevent successful intrusions. For our purposes, I placed controls into two categories:
- Deterrence and Delay (prevention)
- Detection and Detainment
Deterrence and delay
An intruder selects an attack path based on a cost/benefit assessment. If the risk of detection or detainment (apprehension) is too high, he selects another path: if one exists. Further, not all intruders possess a high level of motivation. These potential criminals are easily put off by high fences and other common barriers. Deterrence and delay controls fall into two general categories: location and barriers.
Location, location, location…
We seldom have say in where management builds a facility. In most cases, we are hired well after the organization opens its doors. However, an analysis of structure locations helps determine level of risk, even if we cannot pick up high risk offices and move them to low-risk neighborhoods. Risky locations possess one or more of the following:
- High pedestrian traffic
- High vehicular traffic
- Obscured visibility of areas of probable approach to the site
- High local crime rate
- Infrequent or ineffective police presence
- Volatile/corrupt political or legal environment
-
Significant labor unrest
- Area in general
- Against your organization
The impact each of these has on your organization depends on its industry, its overall impact on the community, and how the locals feel about the organization's quality of citizenship. In other words, do the people like your organization or hate it? Is your product something in high demand by criminals?
The conditions listed above do not remain static. Consequently, review them every year during your annual physical security risk assessment. Use your own observations as well as crime statistics and other publicly available resources to determine overall location risk and changes since the previous year.
Barriers
Deterrence requires barriers: psychological, physical, or both. We should never expect barriers to stop a motivated intruder. Instead, they provide a level of effort and planned delay. Figure 13-2 shows a layered approach to barrier use: site perimeter, building walls and doors, and internal walls and doors.
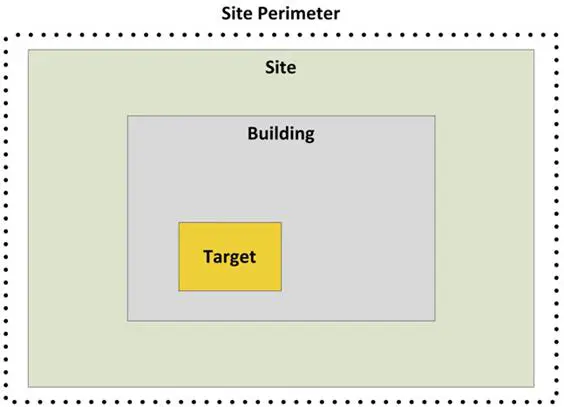
Figure 13- 2: Layered Barriers
Site perimeter
"The perimeter is a clearly bounded space surrounding all property controlled by the organization" (Olzak, 2012). Site barriers tell anyone approaching the site that she is about to enter private property. They usually take the form of signs, landscaping, walls, or fences.
Signs
Signs provide a weak deterrent: one useful only to stop accidental intrusion.

Landscaping and natural barriers
In addition to signs, natural barriers can provide a stronger deterrent. Often consisting of ditches, hills, and vegetation, they introduce some resistance to casual intrusion. One example of a landscaping barrier is the basic berm, shown in Figure 13-3. Adding thick vegetation, such as hedgerows, increases resistance to perimeter entry. In some cases, the location of a site provides natural site boundaries, such as rivers, streams, cliffs, thick brush, or forest. Regardless of whether man-made or natural, most barriers of this type provide little or no real deterrence for motivated intruders.

Figure 13- 3: Berm
Fences
When landscaping and natural barriers do not sufficiently mitigate risk, one of most common choices is fencing. As shown in Table 13-1, fencing characteristics should match the threat type you want to deter and delay. In most cases, an organization is safe enough with one of the chain link designs shown in the table. According to the U.S.G.S (2005), chain link should consist of a mesh of 11-gauge or better wire. To deter an intruder attempting to go under the fence, the bottom links should be no higher than two inches from firm ground. In addition, installers should embed fence posts in concrete, as shown in Figure 13-4.
Table 13- 1: Fence Design and Expected Outcomes
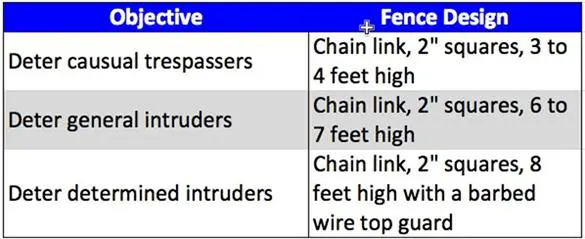
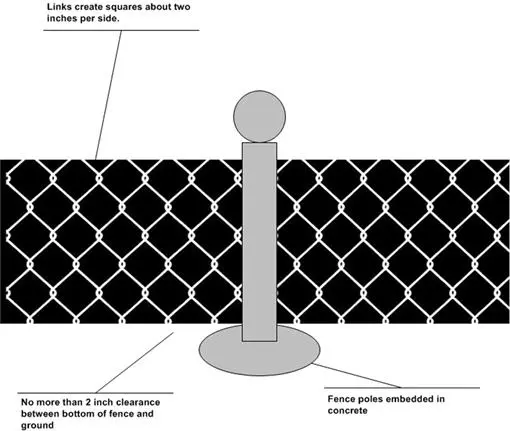
Figure 13- 4: Fence Installation
In some cases, simple fencing is not enough. In such cases, you might have to recommend a top guard. See Figure 13-5. A top guard uses strands of barbed wire or barbed/razor tape, spaced six inches apart, to deter fence climbing. Extending outward at 45 degrees, it increases fence height by about one foot and threatens to make going over the top a painful affair.
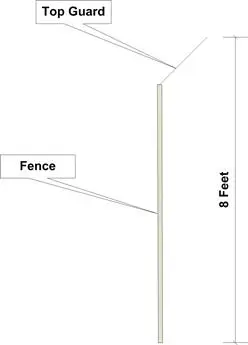
Figure 13- 5: Top Guard (Olzak, 2010)
Adding fences and barbed wire can make your site look harsher than your customers or management might like. It is common to hide fences with hedges or other types of landscaping. If this is one of your organization's requirements, remember to avoid blocking camera or human security views of the fence line. Place berms, hedgerows, etc. outside the fence. In addition, any landscaping, natural barriers, or neighboring structures at or higher than the height of the fence should be at least 20 feet from the fence line. Finally, consider keeping grass and weeds cut around the perimeter. This helps eliminate potential intruder concealment opportunities.
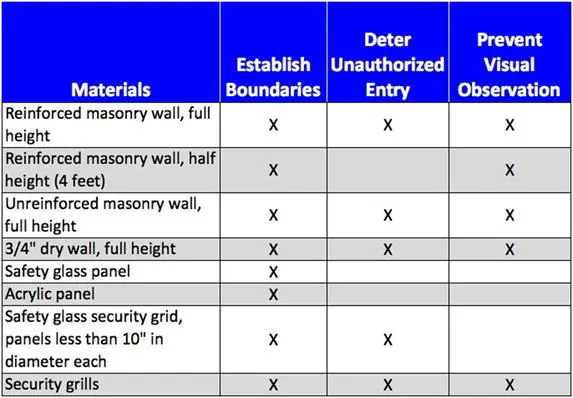
Walls
In situations where security is strengthened by restricting the view from outside the perimeter, walls make a better barrier. Figure 13-6 shows a concrete wall. It is high enough to deter intruders, blocks the view of what is happening inside the perimeter, supports a top guard if necessary, and looks better than many fence solutions.

Figure 13- 6: Concrete Wall (Artisan Precast, 2011)
Structure perimeters
Once an intruder passes the site perimeter, the next barriers to movement toward her objective are the walls and roof of the target building. Walls form external (outside wall) and internal barriers.
External walls
In some cases, external walls might be part of the site perimeter, filling intentional gap in the fence line or wall. When this happens, one consideration is ensuring roof access via the structure's perimeter wall is impossible or restricted. Another variable to assess is the composition of the building's perimeter wall.
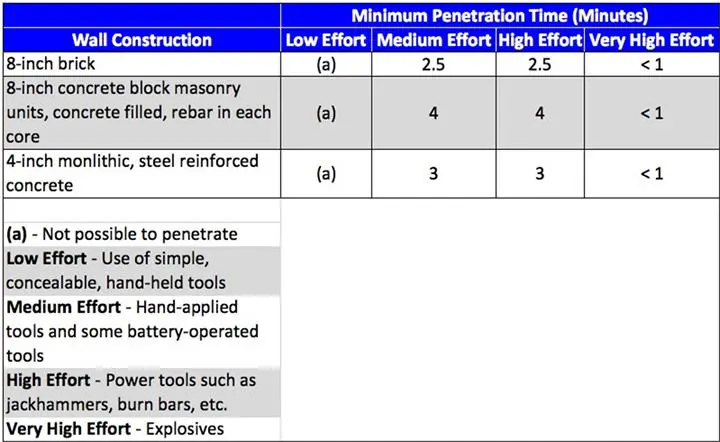
Whether or not a structure is part of a perimeter and the sensitivity of what exists inside the structure affect the types of materials used for the structure's exterior walls. Table 2 provides examples of various wall constructions and the amount of deterrence and delay each provides.
Table 13- 2: External Wall Penetration Times and Relative Effort to Breach (NFESC, 1993)
Interior walls
Interior walls provide additional barriers, assuming the target is not located in a room sharing an outside wall. For example, place data centers in the center of a structure with walls independent from external walls. Once an intruder makes it through an external door or wall, he will meet additional deterrence and delay… as your response team closes in.
An important consideration for interior walls is whether they reach from floor to a solid ceiling. Walls that stop several inches from a plaster or other type of hard surface provide opportunity to enter a secure area by going over the wall. You might want to raise a ceiling tile or two to check around the perimeter of your data center.
Finally, internal walls surrounding sensitive areas should resist an intruder trying to circumvent other controls by breaking through. Table 13-3 provides a look at common internal wall constructions. If all other controls have worked properly (some still to come below), your first responders should already be on the way. Consequently, not all organizations require steel reinforced walls standing guard around servers and storage.
Table 13- 3: Interior Wall Constructions (U.S. Army, 2010)
Barrier gaps
With all the fences and walls going up, employees have to gain ingress somewhere. This requires gates and doors in fences and walls. Additional potential points of entry include maintenance panels, windows, skylights, air circulation vents, etc. In summary, your physical security assessment must consider all points at which access is provided through an otherwise strong barrier. Controlling ingress and egress through perimeter and structural barriers requires one or more of the following:
- Gates
- Vehicle barriers
- Access controls
- Doors
- Grates
- Bars
- Locks
- Window design
Gates
Site perimeter gates are the first point of authorized ingress. Like any barrier gap, they present a weakness to intruders if not properly managed. Most organizations use one of two types of gate access control: automated and manual. Automated access does not require a security guard to open and close the gate. Instead, the organization issues an access card or PIN for employee use when arriving on site. An automated entry system works well for employee access but not for contractor or visitor access. Discretionary access requires a human presence, either at the gate or remotely managing gate access.
Two types of gates are vehicle and pedestrian. Vehicle gates range from simple chain link to crash gates (see Figure 13-7). In some cases, a gate is impractical or requires support to provide stronger resistance. Vehicle controls, such as the retractable bollards shown in Figure 13-8, provide this support.
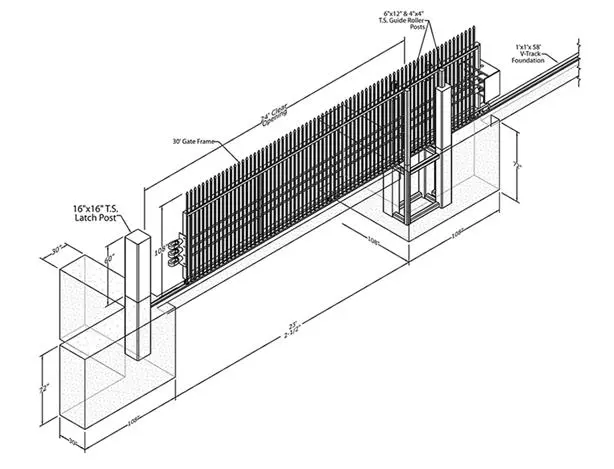
Figure 13- 7: Crash Gate (NEUSS, 2010)

Figure 13- 8: Retractable Bollards (Hercules, 2012)
Like vehicle gates, pedestrian gates are either automatic or manual and come in various styles and levels of resistance. Figure 13-9 shows a common pedestrian gate with electronic access control. Manual points of ingress for moderate to heavy pedestrian traffic often do without gates, with guards controlling access via employee ID or other means of identification. Human presence also provides a means of hindering the unauthorized removal of company property.

Figure 13- 9: Pedestrian/Maintenance Access Gate (Tonbridge, n.d.)
Vehicle and pedestrian control
Some sites are large and contain multiple structures. Controlling vehicle or pedestrian access to restricted areas within the site is the next layer of protection.
Vehicle constraints
Controlling vehicle movement requires strong physical devices, such as bollards and jersey barriers, to control traffic flow (see Figure 13-10). In addition to providing intra-site traffic control, bollards, large rocks, jersey barriers, or other similar anti-vehicle controls help prevent intruders from crashing a vehicle through a perimeter fence.
Doors
Pedestrian control is more complicated. Business operation usually requires employee and vendor access to restricted areas within structures. Deciding who does and does not enter these areas occurs at one or more doors.
External doors
The first door encountered is the primary exterior entry door. It should enter into a reception or guard desk area. Separate the entry area from any restricted area by doors or walls. Lock and closely control access via all exterior doors not opening into the public entry area.
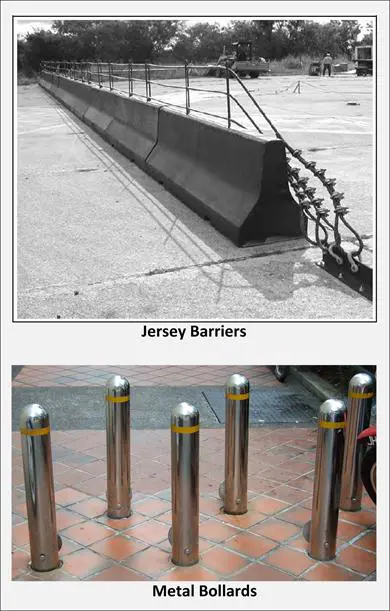
Figure 13- 10: Intra-site Vehicle Barriers (Jersey Barriers, U.S. Army, 2010)
Internal doors
Internal doors provide points of entry through additional barriers within structures. Each door "should be at least as difficult to break through as the surrounding walls" (Olzak, 2012). It makes no sense, for example, to construct steel reinforced walls around a restricted area only to finish off with an easily bypassed door. We look at various locking systems later in this chapter.
A vulnerability to door access control is piggybacking. This occurs when an authorized person unlocks a door and another person, authorized or not, takes the opportunity to enter without using a key code, smart card, key, etc. It is not hard to see examples of this; just watch employees coming to work in the morning. Our willingness to be courteous causes people to hold the door open for the person behind them. One common solution, in addition to policies and employee awareness, is a mantrap, as shown in Figure 13-11.
Although the figure depicts a complicated—and very secure—mantrap configuration, the basic principle is enforceable at low cost. Only one person at a time is allowed to enter the mantrap. In some cases, a guard might watch through a window. In others, a scale might check to see if the contents of mantrap exceed the weight threshold set by security. In this example, cameras determine how many humans are in the mantrap. The approach you take is based on cost and the value of what you protect.

Figure 13- 11: Mantrap (Newton, 2012)
Access "doors"
Maintenance access to wiring, plumbing, and environmental equipment requires hatches and other types of barrier gaps. During your assessment, make sure all access portals are secured with locks commensurate with the access provided. For example, a hatch leading to a site irrigation system for watering the grass might only need a basic padlock. However, a portal leading to a power panel likely requires better security.
In addition to locking doors to restricted areas, ensure hinges are inside the protected area: away from public access. Most locking systems do not prevent someone from removing the hinge pins.
Windows
Employees like windows. It lets the sun in and allows them to check weather and escape from often tedious business tasks. However, windows can also be the best friend of an intruder.
Windows close to the ground (less than 14 feet up the wall) or near a fire escape are the most vulnerable. If these barrier gaps provide access to restricted areas, consider one or more of the following:
- Install windows too narrow for human access (96 square inches or smaller)
- Grillwork or bars
- Alarm the windows (alarms covered in a later section)
Skylights are another challenge. In addition to the recommended precautions above, restrict roof access. Often, it is not only the skylights up there you have to protect.
Ditches, culverts, and nature
Not all fences and walls run over smooth, flat terrain. Many encounter manmade and natural structures that create unintentional gaps, and Mother Nature can create her own intruder friendly conditions. One of the biggest challenges in this category is site drainage infrastructure: ditches and culverts.
When a fence runs over a ditch, for example, it can leave a large opening for easy site access. Any gap exceeding 96 square inches, configured in a way that provides access (e.g., 10" x 10" as opposed to 2" x 50"), requires attention (USGS, 2005). Figure 13-12 shows one way to close the gap under a fence line. Another method is to drive steel rods or posts into the ditch and ditch bank, securely attaching them to the fence.

Figure 13- 12: Ditch Barrier (Hercules, 2012)
In the background of Figure 13-12, another common gap in a perimeter appears: the culvert. Culverts run under roads, walkways, and natural barriers. If large enough, they provide an easy point of access to your site. Locked grates or installation of steel pipe inserts, as shown in Figure 13-13, are two methods to control access. Again, the 96 square inch rule applies.
Finally, the utility companies often install manholes or other access points on a site. Make sure to secure these possible points of entry. This usually requires collaboration with the responsible utility.
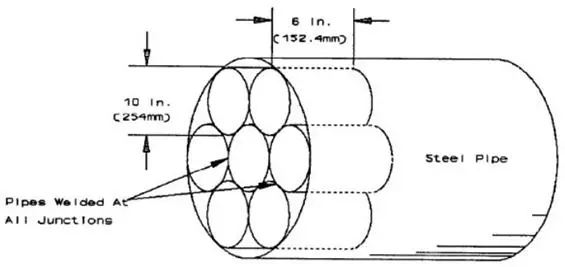
Figure 13- 13: Blocked Culvert
Fence and wall vulnerabilities
Natural events can reduce the effectiveness of a barrier. Further, each type of barrier has its own limitations. For example, an intruder can simply cut a hole in a fence. Conditions you might encounter include (U.S. Army, 2010, p. 4-2)
- Snow or sand drifting against a barrier, making the barrier easy to cross, or it deep enough that an intruder may tunnel near the barrier and move undetected…
- Vegetation such as bushes and trees providing cover and concealment for intruders. They can also provide means to breach or scale the barrier.
- Rain softening the ground around barriers, allowing tunnels or trenches to be dug under barriers.
- Inclement weather such as fog, heavy rain, or snow limiting the visibility of the barrier and providing intruders the opportunity to breach the barrier unseen…
It becomes obvious that barriers are simply one layer in a multi-layered physical security controls framework.
Access control systems
To monitor and control who and what passes through doors and gates, we implement access control systems: locks, centrally managed access, and human response teams.
Locks
"Locks are like passwords: the stronger the better, but always vulnerable when an attacker has enough time and the right tools" (Olzak, 2012). As a physical security control, locks simply add additional deterrence and delay. They should add a planned level of delay and be easy to manage. Lock types include
- Key
- Combination
- Mechanical
- Electronic
Key locks
The most common lock in an organization, and probably the hardest to manage, is the keyed lock on door handles, padlocks, and deadbolt locks. The door handle lock can be a weak control. Firmly pushing a straightened paperclip into the keyhole often does what the right key would do (Olzak, 2010(b)). If the intruder forgot his paperclips, he can try a knife, credit card, or similar tool inserted between the latch and the doorframe.
A better lock for restricted areas is the deadbolt. However, while they are not vulnerabile to paperclips and credit cards, they can be picked. Anyone with the right tools and training can manipulate the lock pins, as shown in Figure 13-14.
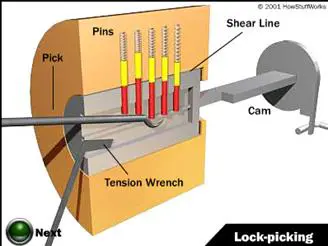
Figure 13- 14: Picking a Deadbolt Lock (Brain & Harris, 2012)
In Chapter 7, we looked at the biggest headache associated with encryption: key management. The same holds true for key locks. We must issue physical keys to authorized employees. However, we must also track who we issued a key to and whether that person still has it or lost it. We must also ensure the employment termination process includes key return. Minimally, an employee should sign for each key received. Further, the key manager should regularly perform a physical check of keys issued: not an easy task in a large company.
Another issue with keys is not having one. For example, if the key manager issues all copies of a specific key, it is possible that access to the area controlled by the relevant lock(s) will be periodically difficult… or impossible. Someone with the key must be available. For this reason, the key manager should retain at least one copy of a key for each lock.
For doors on which deadbolt or handle locks are impractical, the venerable keyed padlock might be the answer. However, the standard hardware store padlock is not usually a good solution. They are easily circumvented using a pick or drill. On the other hand, high security padlocks resist picking and drilling. Figure 13-15 shows a high security discuss lock.
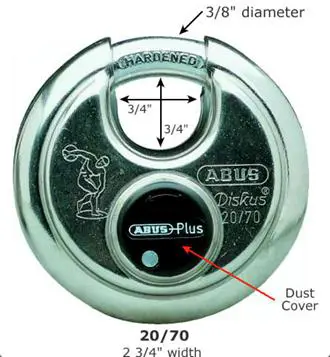
Figure 13- 15: Discuss High-security Padlock
Many myths abound about keyed lock weaknesses. Most are just that: myths. The following debunked myths include five from Peerless (n.d.)and one from Myth Busters:
- Master keys can open any lock. Each master key is different, and each works only with the locks keyed to accept it. In other words, a master key only works with a specific set of locks.
- No one can make a duplicate key of a registered high security key. Although restricted, this is not true. Anyone registered to do so can make a duplicate, usually after showing relevant identification. Do you trust your key manager?
- New locks are necessary when keys are lost. In most cases, this is not true. Call a locksmith and have her rekey the lock.
- Bump key and pickproof locks do not exist. You get what you pay for. If the risk is high enough, and you ask the right questions of your lock vendor, you can purchase locks impenetrable to bump keys and picks. All high security locks are at least bump and pick resistant.
- Any deadbolt lock provides a high degree of security. Not really. Deadbolt locks fall into three grades. Grade 3 is your common household deadbolt intended for interior use. Do not use Grade 3 locks on exterior doors. For exterior doors, both residential and commercial, use Grade 2 deadbolts. Finally, for high security areas use Grade 1 deadbolts.
-
An intruder can go Wild West and shoot off the lock. Again, not really. Any intruder trying this needs body armor and a high-powered rifle (see MythBusters: Shooting Locks). Both are a little inconvenient for an intruder trying to move with stealth.
Rotary and push-button combination locks
Employee turnover, lost keys, and other key management issues make keyed locks a corporate headache. In many cases, a system of combination locks provides security, ease of management, and detection. Combination locks do come with two very big vulnerabilities: employee combination sharing and social engineering. This does not mean you should not use combination locks; it simply means you need to be aware of the issues and put proper control processes in place.
Organizations typically do not use rotary locks for sensitive area entry. Rather, push button locks are more common: both mechanical and electronic. Figure 13-16 shows a mechanical deadbolt version. Your key manager can rekey these locks, and they provide quick access.
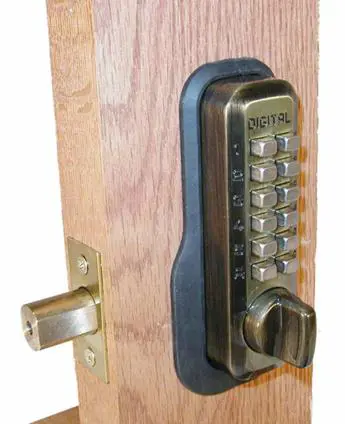
Figure 13- 16: Push Button Mechanical Deadbolt (Lockey® M210)
When selecting a mechanical push button lock, make sure it meets your delay requirements. For example, KrackMaster (2012) describes a method by which an attacker, with few skills, can open an inexpensive mechanical push button lock. Once again, know your risk and ask the right questions when you sit down with facilities management or the lock vendor.
Panic bars
Common in business, panic bars provide convenience and ease of egress in case of emergency. However, an intruder with a crowbar has no problem gaining entry if proper steps are not taken. Figure 13-17 shows a panic bar. Note the lack of a deadbolt. The only thing securing the door is a common latch.

Figure 13- 17: Panic Bar
Figure 13-18 shows an external view of a panic bar installation. The red arrow in the top photo shows the location of the latch securing this steel door. Placing a crowbar here provides enough purchase to free the latch. The bottom photo shows a simple control to prevent crowbar access: installing an inexpensive latch plate protector. Note the damaged concrete in the photo. The business owner installed the plate after a break-in.

Figure 13- 18: Panic Bar Installation with Latch Plate Protector (Olzak, 2008)
Electronic lock systems
Mechanical locks work great when a lock manager only has a few to worry about. However, large organizations usually require a centralized management solution. Electronic locks, although also common standalone solutions, can serve as the sentinels of an integrated door security system. Figure 13-19 depicts a pushbutton electronic lock.

Figure 13- 19: Pushbutton Electronic Lock
Figure 13-20 shows one example of a connected electronic lock configuration. In addition to pushbutton locks, electronic systems can integrate all three access control factors (i.e. something you have, something you know, and something you are) into one access control network. Managers make changes to employee access from a central console. Further, the system administrator can change lock combinations without leaving her office. The system can aggregate lock logs and alert on unusual activity, like after-hours access. Finally, after-hours access is often configurable, denying access to certain areas when personnel are not expected to work.
Again, locks are simply a deterrent; they will not stop a motivated and skilled attacker: or one with a crowbar. Select locks based on risk mitigation and expected detection and response times.
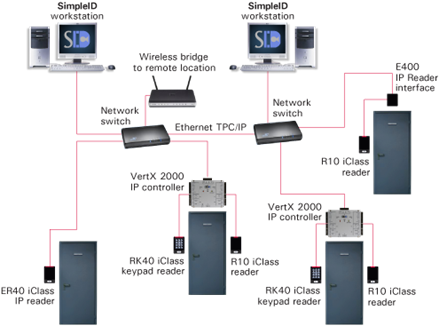
Figure 13- 20: Electronic Lock System (Midpoint, 2009)
Visitor control
Barriers work for the unauthorized visitor, but what about people invited in by your employees? Common visitors include customers, sales people, and maintenance technicians. Allowing them access to our facilities is usually necessary for continued business operation. However, controlling where, when, and how they visit is a critical element of physical security.
Visitor control consists of three fundamental activities:
Detect and detain
In a layered security model, we assume an intruder will eventually break through one or more of our preventive control layers. For this reason, detection and intruder intervention layers complete our physical security controls framework, including
- Landscaping and lighting
- Monitoring, surveillance, and alarms
- Planned, documented, and practiced human response to contain and apprehend/detain an intruder
Landscaping and lighting
Earlier in this chapter, we looked at using landscaping for barriers. In addition to barrier construction, landscape planning also includes ensuring visibility to all probable avenues of approach to the site and to structures within the site. Combined with lighting, carefully planned and maintained landscaping ensures intruders have no opportunity for concealment as they make their way across our property.
Landscaping
The basic principle of landscaping is clearing the grounds (Olzak, 2012).
- Remove all shrubs and tall grass within 10 to 12 feet of both sides of the perimeter barrier.
- Cut grass to eight inches or less on all areas of the site.
- Remove trees within 20 feet of the public side of the perimeter fence or wall.
- Remove all shrubs or trees large enough for concealment within 50 feet of site structures.
- Fill small natural depressions or holes large enough for concealment.
This list includes common steps toward security-friendly landscaping, but each site is unique. During your risk assessment, walk the site. View the site from the perspective of visual monitoring devices and personnel. Identify all possible areas of concealment and, if possible, remove or mitigate their value to an intruder.
Lighting
Darkness is always preferred when an attacker plans an intrusion. It hinders our ability to detect her advance, elevating the possible cost verses benefit. Consequently, lighting is a great deterrent. In addition, well designed lighting eliminates shadows that provide areas of low visibility for monitoring activities.
We measure lighting in one of two ways: foot-candles or lux. A foot-candle is the illumination at a point on a surface one-foot from, and perpendicular to, a light source equal to one candela. A lux also uses the candela standard, but it is measured from a distance of one meter. One foot-candle is approximately 10.76 lux. It is not important to know how to calculate a candela. What is important is the information in Table 13-4.
Table 13- 4: Lighting Guidelines (U.S. Army, 2010)
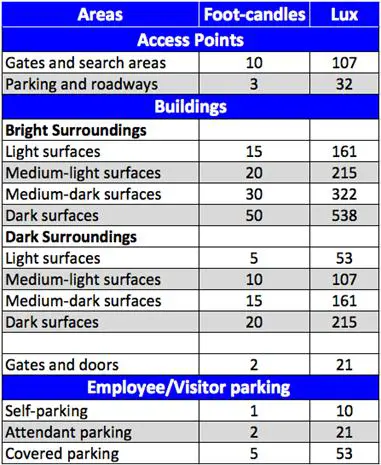
Note that lighting requirements may not be the same for all areas of your site. Selecting a single light source type for placement across your entire site is probably not a good design plan. Areas not specifically covered in the table are perimeter depressions, such as ditches and culverts. For these and other natural or manmade areas of shadow and concealment, consider special lighting placement with the illumination level indicated for gates and doors.
Monitoring, surveillance, and Aaarms
Monitoring and surveillance are fancy terms for looking for the bad guys. Using human or electronic means, anomalous conditions are identified and, if appropriate, alarms initiated. Anomalous conditions include either an actual intruder sighting or evidence of an intrusion. For example, a guard coming upon a hole cut in a perimeter fence has just found an anomalous condition.
Guards
The best monitoring and surveillance controls are human guards. They can differentiate between real and false threats and provide quick response. However, trained and vigilant guards are expensive. For this reason, it is common for small and medium sized businesses to opt for third-party remote management of technical controls (e.g. cameras) with police response.
Cameras
"Cameras provide real-time visibility into structures, restricted areas, and across the site" (Olzak, 2012). When monitored by security personnel, they
- Provide detection of intrusion or anomalous conditions
-
Enable verification of a threat or a false alarm
The important component of camera surveillance is real-time monitoring. Placing unmonitored cameras simply to record activity is not a detect and detain control. While they do provide a level of deterrence, unmonitored cameras are best used for incident reconstruction during post intrusion investigations.
Today, organizations have the option of either running cable from cameras to a central monitoring/recording center or using wireless technology. When using cable, make sure an intruder cannot access it. Usually, this means burying the cable. For wireless, ensure encryption and some form of rogue device detection.
To be effective across all types of probable site conditions, choose the right camera solution. For example, what happens if the site loses power? Can the cameras store video if one or more connections to the security office are down? Is the central monitoring/recording equipment connected to an alternate power supply (e.g. generator) in case of power failure?
Where you place cameras is an important design consideration. It is not necessary to monitor all areas of the site. Rather, identify probable paths of approach and hidden areas. Also, monitor the perimeter barrier, gates, doors to restricted areas, inside restricted areas, and roofs. Although a roof might not provide opportunity for building access, an intruder might be able to disrupt business operation by destroying rooftop infrastructure.
Non-visual detection solutions
We cannot see everything, and guards are human. They can sometimes miss something that quickly passes across a monitor. Even if an intrusion is detected, it is important to know where the intruder is at all times. Finally, it is not always possible to place cameras at all points of entry to the site, to structures, or to restricted areas within structures. For these reasons, technical detection and alarm solutions must support any visual controls. Non-visual detection systems include
- Dry contact switch. A connection is made between two foil strips. For example, one strip is placed on the window sill and the other on the window. If the window is opened, the connection is broken and an alarm condition initiated.
- Electromechanical. Electromechanical switches work on the same principle as dry contact solutions but use a mechanical switch to initiate an alarm.
-
Vibration detector. Often used on fences, ceilings, and walls, these detectors sense attempts to penetrate or circumvent barriers. The piezoelectric sensor cable shown in Figure 13-21 picks up both vibration and sound.

Figure 13- 21: Vibration Detection (AMC, 2012)
- Pressure mat. Step on the mat, an alarm condition initiates.
- Photoelectric or photometric. A light beam establishes a connection between an emitter and a receiver. An alarm condition exists when the beam is broken.
- Wave pattern detector. As shown in Figure 13-22, a wave pattern is created across an expected approach path or around restricted structures. When an intruder passes through the electromagnetic field produced by the wave pattern, detectors sense a change in field characteristics and initiate an alarm.

Figure 13- 22: Electromagnetic Field Interruption (IT, 2007)
- Passive infrared. Changes in a room's heat patterns initiate an alarm.
- Audio/acoustic. Detects changes in ambient noise levels.
- Proximity or capacitance. Works on the same principle as the larger wave pattern detector. However, it is used for smaller, internal detection. For example, approaching a door or a server.
- Air pressure detection. When a door or window to the outside opens, it disturbs the air pressure in a room or structure. These detectors sense that change.
- Duress activation. Unlike the other detectors in this list, duress activation is initiated by a human. Many electronic lock systems include a duress code feature. If an intruder forces an employee to enter a lock code, he can enter the duress sequence instead… at least the first time. This typically initiates a silent alarm condition.
This is not a complete list of all possible products available. There are many that combine two or more of these for hybrid solutions. Further, each listed and unlisted solution comes with advantages and disadvantages when compared with other approaches.
Do your research and know what questions to ask before you sit down with your vendors. Understand environmental factors that might affect each solution presented. Ask about error levels and the rate of false positives. Consider a small pilot installation, if appropriate, to test the vendor's claims and the system's suitability for your application and environment.
Finally, detection and alarm systems must be flexible. This means dividing structures and areas of the site into zones. When arming the alarm system, security personnel can select to ignore one or more zones if business operation requires it. For example, you do not want the data center alarm activated when engineers work overnight. However, you do not want their presence to put the rest of your site or structure at risk.
Response
Incident response is a critical component of physical security. However, it is not always appropriate (or safe) for your employees to assume the role of first responders. This is usually something for the police or armed guard service. In any case, response should achieve the following outcomes:
- Detect the intruder during initial site penetration, if possible. Implement controls to detect intruders as far as possible from assumed targets.
- Assess conditions that activate alarms. While in the military police, I responded to numerous false alarms. Your selection of detection controls should reduce the number, but you will not completely eliminate them. Part of assessment is also determining what is happening. Where is the intruder headed? What is the probable target? What is the total number of intruders? Are they armed? This is important information for first responders.
- Track/Contain the intruder until first responders arrive. Contain or hinder intruder progress only if it is safe to do so. Employee safety is the first priority of any physical security plan.
- Apprehend the intruder: a role assumed by first responders.
- Manage the incident, including root cause analysis to identify what happened, what should have happened and how to improve deterrence, delay, detection, and response activities.
Conclusion
The purpose of physical security is to first deter intruders from entering a site. However, knowing that we cannot deter all potential attacks, we must support deterrence with delay, detection, and response. Through all planning, the most important consideration is human safety.
Barriers should delay intruders. The amount of delay is directly related to how long it will take to detect and apprehend an attacker. Much of this depends on how long it takes first responders to react. Do not assume reaction times. Sit down with police or your security service and set realistic expectations.
Securing a site requires more than fences and locks. It also requires landscape planning and maintenance. The final outcome should be the absence of any area on the site where an intruder can hide in grass or behind shrubs. Further, work with those responsible to remove all trees within 20 feet of your perimeter fence or wall. If the wall or fence is in planning, consider placing it 20 feet inside your organization's properly line. This gives you control over what is planted or constructed close to your fence line.
Support landscaping with lighting. Ensure sufficient illumination for cameras or human surveillance of the property, entry and exit points, and perimeter. Give special attention to ditches, culverts, and other depressions near the perimeter.
Detection controls come in many forms. Understand your business, your environment, and know what questions to ask your vendors. If possible, conduct suitability tests of cameras and sensors.
Finally, ensure your response process is documented and practiced. Every minute your team takes to decide what to do next is one minute of intruder delay wasted. Response should be automatic without the need to find and read the documented process.

Cybersecurity interview guide
Sources
- Vibration Detection Fencing
- Concrete Walls
- How Lock Picking Works
- Hercules Fence
- Intrusion and Burglary
- Picking New High Security Door Locks
- System Diagram
- Crash Gate Drawing
- The TDAR Anti-Tailgating Anti-Piggybacking Barrier for Mantraps
- Design Guidelines for Physical Security of Facilities
- Anatomy of a Small Business Break-in
- Physical Security Locks, Biometrics, and Other Fallacies
- Physical Security: Human Intrustion Defense
- The Art of Physical, Outer Perimeter Security
- Top 10 Myths About Lock Security
- Pedestrian Gate and Door Access
- U.S. Army. (2010). Physical Security, ATTP 3-39.32. United States Army.
- U.S. Geological Survey Manual: Physical Security Handbook, 440-2-H








