Attacking Gaming Systems: A Dangerous Trend
Introduction
The gaming industry is one of the most lucrative markets, for this reason, is becoming even more attractive to cybercriminals.
Hackers are employing tactics used to target other industries, like banking and retail, to hit gaming firms and players online.

Learn Network Security Fundamentals
Last year, the Steam online video game platform publicly admitted that 77,000 of its gamer accounts are hacked every month. The news shocked the gaming industry, for the first time a major video game company admitted to being a cybercrime target.
This year, the Kaspersky Lab researcher Santiago Pontiroli launched an investigation into how many gamers are being exploited by cybercriminals. The expert uncovered the existence of a new type of malware developed specifically to hack Steam accounts. The "Steam Stealer" was able to bypass the Steam client's multifactor authentication (MFA) protocols, which enables hackers to take over a player's account.
We have to consider that of the 1.2 billion video game players worldwide, nearly 700 million of them play online. It has been estimated that the video game industry revenues are more than $86.8 billion annually, nearly double the amount of the film industry. Now it is easy to understand why the gaming industry is a privileged target for financially motivated hackers and fraudsters.
Online video games are indeed vulnerable to attacks. Unfortunately, the video game industry is still largely in denial over the fact that it is a systemic problem. Dark Reading reports:
"In-video game attacks occur when a player's account is hijacked using readily available malware that enables man-in-the-middle exploits, keylogging, remote access, and other hacks. Once inside, cyber criminals can steal player credentials, gain access to a player's game account, transfer in-game assets to other accounts, and sell those assets on the 'grey market,' an unauthorized, but not necessarily illegal place that is used to sell virtual items and currency for real money."
Another element to consider while analyzing cyber security for the gaming industry is the emergence of a 'gray market' sustained by the demand for virtual items that people obtain through regular gameplay and then sell them for real money. Known as 'gold farming,' it is so rampant and profitable that in a World Bank report it is estimated that it generates $3 billion a year for people in developing countries.
The high demand for virtual items is motivating gold farmers in automating their operations through thousands of bots that allow speeding up the accumulation process. This phenomenon has flooded the online gaming economies and has caused publishers to lose as much as 40 percent of in-game revenue per month, of course, there are also serious damages to the reputation of the gaming firms.
One of the biggest hacks of all time, the one suffered by the Sony's PlayStation Network in 2011, resulted in 77 million account holder details being compromised and twelve thousand credit card details were leaked. Not too bad for cybercriminals.
Which are the most common hacking techniques against gaming industry?
- DDoS attacks to cause disruption – Denial-of-service (DoS) or distributed denial of service (DDoS) attacks are frequently used by hackers to bring down websites or web services of gaming companies. The most clamorous DDoS attacks against gaming platform were launched by the 'Lizard Squad' crew that knocked the Sony's PlayStation Network and Microsoft's Xbox Live offline last Christmas Day, causing thousands of gamers to be unable to access both services."
- Spoofed websites for grabbing credentials and more – Usually hackers deliver malware to users by way of fake websites designed to steal from them.
- Stealing money with ransomware and scareware – In March 2015 media reported cybercriminals were infecting gamers' machines with ransomware. The victims were not able to continue playing their games until they paid a Bitcoin ransom.
- Brute force attacks and keyloggers to spy on passwords – Login usernames and passwords are always sought after by cyber criminals–irrespective of what sector the victim's business is in. And, gaming sites are no exception, as Sony, Ubisoft and others know well.
- Utilizing social engineering to achieve all of the above –Social engineering attacks, such as phishing, are exploited to target gamers.
It's Pokemon Go Mania, from PoodleCorp to OurMine
While the gamers worldwide are going crazy for the last Nintendo game Pokemon GO, which uses augmented reality, the hacking group PoodleCorp claimed credit for taking down the servers of the popular game 'with DDOS attack.'
The hacking crew flooded the servers of the company with so many requests that they went down, and users in Europe and US were not able to access the gaming platform.
The most concerning aspect of the attack is that according to the PoodleCorp it is just a test for a bigger offensive on a large scale.
"Just was a lil test, we will do something on a larger scale soon," said the post by user XO.
The group posted the date 1 August on its Twitter account; experts speculate that it could be the date of the announced bigger attack. Poodlecorp plans to shut down the Pokémon Go servers globally for an entire day.


Figure 1 - PoodleCorp Tweet
Why Pokémon Go?
It's simple; the hacker is targeting the most popular target at the moment to demonstrate their strength and gain notoriety.
"We take the servers offline because it is popular right now and nobody can stop us," @xotehpoodle said to Tech.mic. "We do it because we can, nobody can stop us and we just like to cause chaos. We chose August 1 so we have time to relax and not care about doing anything."
"basically the entire day" — by using the same method they claimed to have used over the weekend, a DDoS attack. They plan to hit the servers with "a massive botnet consisting of about 600,000 devices ranging from DVRs to routers to cameras to computers to dedicated servers," @xotehpoodle said.
But Poodlecorp isn't the only group trying to knock the popular game offline, hackers belonging to the dreaded hacker group OurMine launched their attack against the Pokemon Go servers too.
OurMine explained that it had launched the attack to encourage the staff behind Pokemon Go to improve the security of its services.
Also, OurMine targeted Pokemon Go servers with a distributed denial of service (DDoS) attack causing serious problems to the players that were not able to access the platform.
The group announced it would not stop the attack until representatives from Pokemon Go contacted them.
"No one will be able to play this game till Pokemon Go contact us on our website to teach them how to protect it!"
Pokemon Go access was spotty throughout Sunday, with users complaining about the server outage.
Members of OurMine targeted many IT VIP and celebrities, including Sundar Pichai and Jack Dorsey, they highlight the importance of a proper security posture that their victims haven't, so they are offering their support for an amount of money from $30 – $5000 for its services.
"We don't want other hackers attack their servers, so we should protect their servers," OurMine explained.
As we have seen two different hacker crew with totally different motivation, have chosen the same target, the gaming industry, demonstrating how much attractive are this kind of services are for hackers.
And they were not alone ...
The game is viral, for this reason, crooks are trying to exploit its popularity to spread a malicious version of the Pokemon GO app and infect Android mobile devices by delivering a backdoor and gain complete control over the victim's smartphone.
Security researchers from the security firm Proofpoint discovered a malicious Android application that included the DroidJack remote access tool (RAT). The official Pokemon GO app was first launched in Australia and New Zealand on July 4th, and later on July 6th in the US, but the malicious app was first uploaded to an online malware detection repository on July 7.
The popularity of Pokemon Go pushed gamers into searching for the app also outside the official app stores, many media outlets published instructions on how to download the game from third-party stores.
"The augmented reality game was first released in Australia and New Zealand on July 4th and users in other regions quickly clamored for versions for their devices. It was released on July 6th in the US, but the rest of the world will remain tempted to find a copy outside legitimate channels. To that end, a number of publications have provided tutorials for "side-loading" the application on Android. However, as with any apps installed outside of official app stores, users may get more than they bargained for." reported ProofPoint in a blog post.
To install the malicious Pokemon GO app, the gamer needs to "side-load" it by disabling an Android security setting.
"Unfortunately, this is an extremely risky practice and can easily lead users to installing malicious apps on their own mobile devices," highlights Proofpoint. "Should an individual download an APK from a third party that has been infected with a backdoor, such as the one we discovered, their device would then be compromised."
The good news is that it is quite easy to check if the version you have downloaded is infected, for example by comparing the SHA-1 digest of the legitimate app with the one calculated for the application you have downloaded.
Another thing to consider is that the malicious Pokemon GO app requests more permissions of the legitimate one.
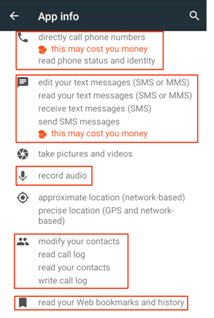
Figure 2 - Pokemon Go permissions
"Bottom line, just because you can get the latest software on your device does not mean that you should," the security researchers write. "Instead, downloading available applications from legitimate app stores is the best way to avoid compromising your device and the networks it accesses."
Conclusions
To improve the resilience of the gaming industry to cyber attacks, it is essential to adopt threat intelligence processes and encourage the information sharing, more or less the same strategy used by organizations in other sectors.
It is expected that large-scale attacks will continue to occur until the gaming industry wakes up and begins tightening up on cybersecurity. Cyber criminals aren't going to stop until they're stopped, and the only way to do it is to profile them and recognize their technique, tactics, and procedures.
References
http://securityaffairs.co/wordpress/47376/cyber-crime/gaming-industry.html
http://securityaffairs.co/wordpress/49246/malware/malicious-pokemon-go-android.html
http://securityaffairs.co/wordpress/49647/breaking-news/pokemon-go-hacking.html

Take your hacking to the next level
Learn how to pentest and be an ethical hacker with expert-guided training, or learn more about the world of ethical hacking.
https://techcrunch.com/2016/07/17/ourmine-attacks-pokemon-go-servers/








