Wordfence: Security Plugin for WordPress
Wordfence is a free security plugin for WordPress. Security "plugins" for Wordpress are often highly criticized as many may give a false sense of security or simply just automate creating .htaccess files - sometimes recklessly. However, Wordfence stands clear apart and above other plugins as it offers malware detection, checks for out-of-date plugins or themes, provides firewall throttling or blocking rules, has the ability to restore compromised or altered WordPress theme or plugin files, and offers an optional paid vulnerability scan from their data center. Those are just a few of the highlights which are to be touched upon below. Let's dive in.
The Wordfence Scan
Wordfence functionality is based around a security scan the plugin performs. Out of the box, the plugin is ready to use and scan. Simply install and click Scan. The Wordfence Scan checks for the following issues:

Learn Python for Pentesting
Remote scan of public facing site [paid feature]
Comparing core WordPress files against originals in repository
Comparing open source themes against WordPress.org originals
Comparing plugins against WordPress.org originals
Scanning for known malware files
Scanning file contents for infections and vulnerabilities
Scanning files for URLs in Google's Safe Browsing List
Scanning posts for URL's in Google's Safe Browsing List
Scanning comments for URL's in Google's Safe Browsing List
Scanning for weak passwords
Scanning DNS for unauthorized changes
Scanning to check available disk space
Scanning for old themes, plugins and core files

Restore Modified or Possibly Compromised Plugin or Theme Files
The biggest feature of Wordfence is that it analyzes all core WordPress files, theme files, and plugin files for changes against the current available versions of those components. Users can click to repair/restore the original version of the file, view changes on screen, or ignore the finding. To avoid a customized theme from being flagged in this check, one should make use of WordPress child themes for theme changes.
Wordfence performs this by checking MD5 and SHA hashes of the installed files in a Wordpress installation against a database of hashes of original files. The hashes are sent securely via 443 SSL to the Wordfence servers. This provides a quick and simple way to compare if files are different or have been modified for any reason, such as from malware or compromise.

Live Traffic
Wordfence offers an optional Live Traffic view. This runs via JavaScript that records its own analytics separate from any other logging. Information such as browser agent, IP address, geo-location, and the ability to click 'block' beside the IP makes this an invaluable feature. The only feature lacking is any ability to dump or export all of the traffic data to a CSV or XML file, which would be valuable.

Blocked IPs
Antoher feature in Wordfence is the ability to block an IP address from access to the WordPress site. Specific IP addresses can also be blocked from accessing the WordPress Login page to add security around the login area.
Note that Firewall and IP Blocking only prevent access to the WordPress site itself. This is not a replacement for a full operating system firewall, nor does it interact with iptables or other operating system level restrictions. Frankly, a WordPress plugin controlling an operating system firewall would probably be a bad idea. An example screen that is shown to a blocked IP is below.


Country Blocking
Scheduled Scanning
Two paid features are blocking entire geographical regions by geo-location as well as scheduled scanning. These add convenience but are not required for the full plugin functionality.
Wordfence Options
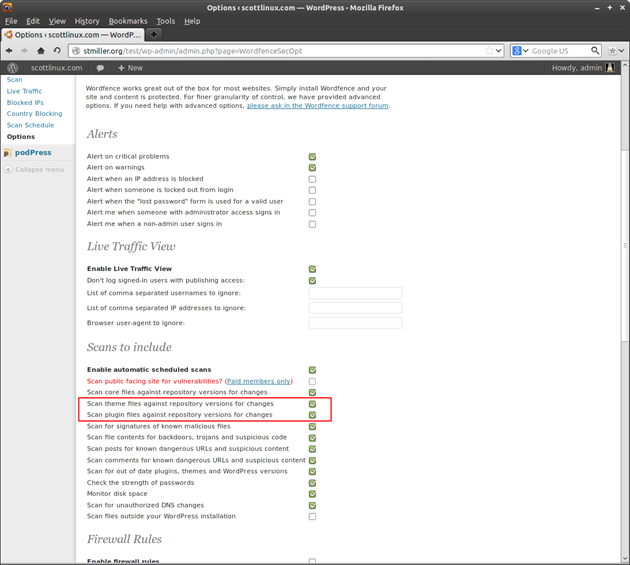
Once single Options page provides the entire configuration for Wordfence. Making changes here is completely optional, though users who want to make more changes under the hood will want to inspect this area.
Starting at the top, a drop down menu offers a quick security-hardening setting. In case the site is under attack or being the focus of abuse, the security level can be changed quickly here to various levels. Otherwise, each individual option can be set as shown below.

Advanced Options
Alerts
Various email alerts are possible from email alert when a user logs into the site, to emails about critical security problems found.

Live Traffic View
Here the Live Traffic View can be disabled if desired. I mention this as the only information leakage from the Wordfence plugin is the Live Traffic View javascript which is visible in the HTML source. (See screenshot below). It is still possible to block IP addresses with Live Traffic View disabled, though of course no fancy Live Traffic View would be available to see live traffic.
Scans to Include
In the Scans to Include section, it is best to enable two options that are not on by default to scan themes and plugins for changes. Often malware or another compromise will alter or change files on the server. These options let Wordfence check that all files in themes and plugins are of their originals and not compromised.
- Scan theme files against repository versions for changes
- Scan plugin files against repository versions for changes
Firewall Rules
Wordfence offers its own firewall to either throttle or block IP addresses based on various actions.
For instance, to avoid situations where the site may be flooded or DoS'd, enable the feature to throttle or block a connection after a large number of requests (32 per second). As previously mentioned, these rules only restrict access to the WordPress site itself, and have no effect on the operating system level Firewall.

Login Security Options
To add additional security around the WordPress login, Wordfence offers many good features. After X number of bad login attempts, the IP can be blocked. The more fascinating feature offered here is Don't let WordPress reveal valid users in login errors. Many Wordpress hacks based around the login page are from information leakage where WordPress confirms valid usernames at the login page.
While these are great features to add security around the login, the best security is to prevent access to the WordPress login page entirely by Apache server authentication if at all possible.
Other Options
In the final section Other Options, specify a home or work IP address in the whitelist so Wordfence does not block or limit valid connections from valid WordPress administrators.
If the option to Participate in the Wordfence Security Network is selected, IP addresses that have violated login or firewall rules are sent to Wordfence to help in a global block list for other users. If desired, disable this option for privacy reasons.

Effectiveness and Conclusions
Wordfence offers extremely easy deployment of added security layers to WordPress. The highly customized options make Wordfence a good choice for one who perhaps is not interested in the Firewall, but only want to audit code changes. The Firewall can be disabled, and only code changes can be scanned, as one example. Wordfence has a large user community on their forums ( http://www.wordfence.com/forums ) and offers support for paid users. A negative often spoken of security plugins is that they often only automate or change what one could change for themselves anyway. But here Wordfence's code auditing, firewall with throttling options, malware detection, and other features are a bit far from what one could do themselves or at least not without quite a bit of effort. Wordfence operates in large part with its cloud servers located in Seattle, Washington who play a large part in the code auditing and IP block lists correlation, as well as perform scanning for paid users.

Learn ICS/SCADA Security Fundamentals
Of all of the various security plugins for WordPress, Wordfence provides unique layered security options with an extremely easy-to-use interface. Check it out at http://www.wordfence.com.







