Hacking android apps using backup techniques
In the previous article, we had an introduction on how to analyze Android application-specific data using Android backup techniques. This article builds on the previous article. We are going to see how local data storage or basic checks that are performed on a local device can be exploited on a non rooted device using data backup techniques. This shows the significant risk associated with apps that are not so concerned about security.
Before proceeding with this article, I would suggest you to go through my previous article, if you haven't done so.

Learn Vulnerability Assessments
Prerequisites
Install the Star archive command line utility, which is available for download from the link mentioned below.
http://sourceforge.net/projects/adbextractor/
I suggest you to go through the previous article, if you don't know how to use the file downloaded from the link above.
Using the terminal, navigate to the directory where the Star utility is located. This is shown below.
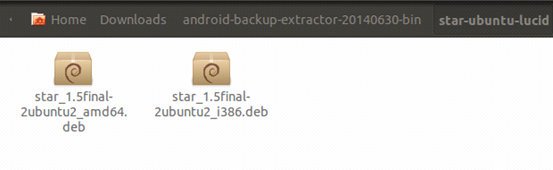
Run the following command to install Star in an Ubuntu machine.
dpkg -i star_1.5final-2ubuntu2_i386.deb
This should install the Star utility in your system.
I am going to use the same working directory I used in the previous article for performing all steps.
Steps at a glance
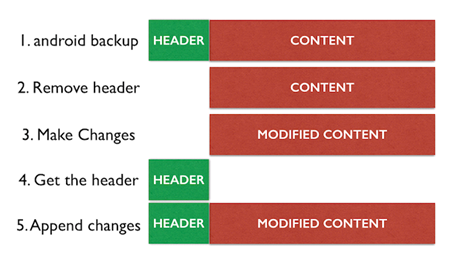
- Step 1: Get the backup of our target app
- Step 2: Remove the header part and save the file
- Step 3: Make required changes to the content of the app
- Step 4: Get the header part from the original ".ab" file
- Step 5: Append the modified content to the header
- Step 6: Restore the backup with the modified content
Though these steps look simple, this involves slightly complex techniques when we try attacking the application. Let us carefully go through each step.
This whole process is well covered in the XDA forums thread given in the references section. If you want to know more about it, please refer to that article.
In this article, we will take a sample application and see how we can modify the content of an app on a non rooted device practically.
The sample application used in this article can be downloaded from the downloads section.
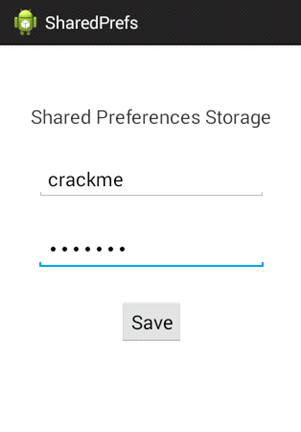
Launch our target application on a non rooted device and enter some data as shown in the figure below. This will save the data in an XML file.
As we did in the previous article, let us first take the backup of our target application using the command shown below.
adb backup -f mybackup.ab com.androidpentesting.sharedprefs
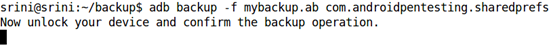
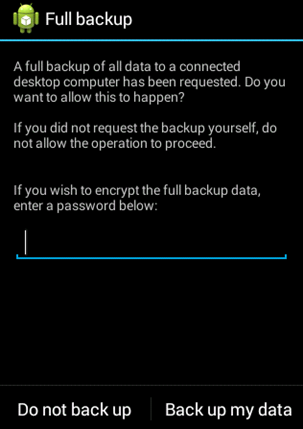
As we can see in the figure above, it is prompting us to confirm the backup operation on the device. So, let us open the device and confirm the backup operation as shown below.
Once we confirm, it will create an Android backup file with an ".ab" extension. Usually, the first 24 bytes will be the header. So, we will use the dd tool to remove the first 24 bytes and create a tar file of the remaining part. This can be done as shown below.
dd if=mybackup.ab bs=24 skip=1| openssl zlib -d > mybackup.tar
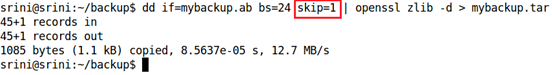
The above command skips the first block from the input file, which is the header part of our Android backup.
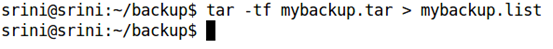
Now, create a ".list" file from the tar file we generated in the previous step. This is to ensure proper order when repacking the backup.
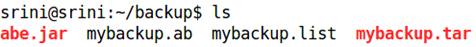
We should have the following files with us now.
mybackup.ab - Actual Android backup taken from the device
mybackup.tar - File generated using dd
mybackup.list - File generated using the tar file
We can simply extract mybackup.tar file using the following command:
tar -xf myback.tar
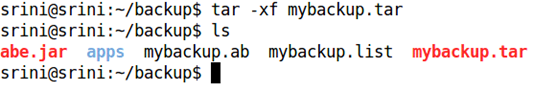
As we can see in the above figure, we have a new folder named "apps". We can get into this directory to view the app specific information.
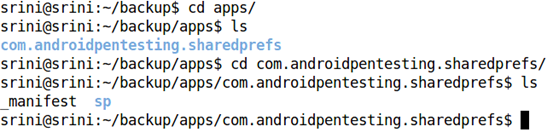
As we can see in the above figure, we have an "sp" folder, which contains the XML file storing our target apps data.
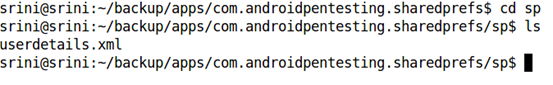
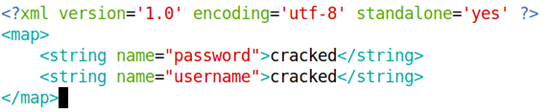
We can view the contents of the XML file as shown below.
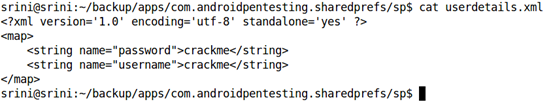
Now, let us modify the contents using a text editor. In my case, I am going to use "vim" and change the content as shown below.
We now need to push this modified file onto the device.
To push this modified file, it should be in Android backup (.ab) format.
For this, we need to add the ".ab" header which we removed in the beginning. So, let us first create the modified ".tar" file with the contents and then add the header to that.
We can do it using the star command as shown below.
star -c -v -f newbackup.tar -no-dirslash list=mybackup.list
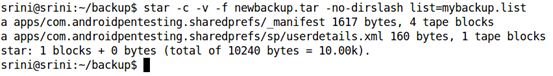
We have the "newbackup.tar" file.
Let us get the header part of the actual Android backup file and append the new tar file to it.
dd if=mybackup.ab bs=24 count=1 of=newbackup.ab
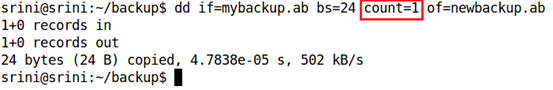
As you can see in the above figure, we are copying only one block from the backup file. This is "newbackup.ab"
The last step would be to append the modified content to the header.
We can do it using the following command.
openssl zlib -in newbackup.tar >> newbackup.ab
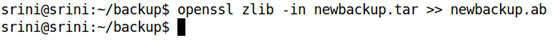
Our modified backup file is ready. We will have to restore this backup file onto the device using the following command.
adb restore newbackup.ab
This is shown in the figure below.
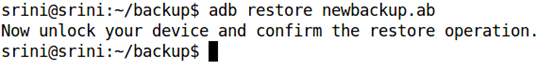
It will display a prompt on the device and we need to confirm the restore operation.
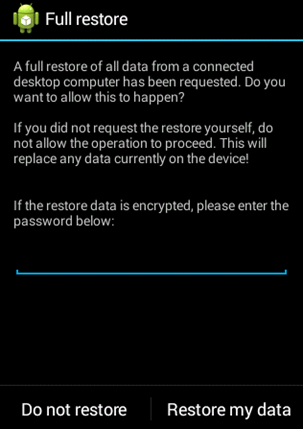
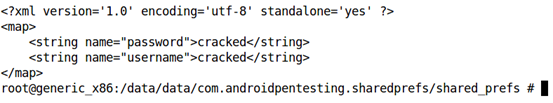
Once we click the button "Restore my data", the data will be restored and we will be able to see the modified content on the device. We can check it by navigating to the location of the app and viewing shared preferences on the device. (Root is required to do this -- trust me, your data is modified :-))
To verify it without root, you can get the backup of this app again and check it on the local system.
As you can see in the figure below, the data has been modified.
If you want a real case study of this attack, please refer to the following video mentioned in the sources section.
How to protect our apps
If your app holds sensitive data, you can stop allowing users from making a backup of the app. This can be done by placing the following line in the AndroidManifest.xml file
android_allowBackup="false"

Learn Python for Pentesting








