Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

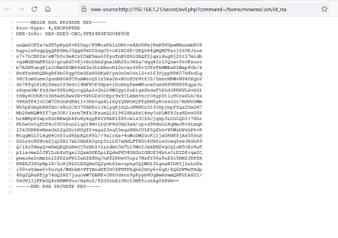
CORROSION: 1 VulnHub CTF Walkthrough Part 2

Passion and perseverance equal success for this inspiring scholarship winner

Twitch and YouTube abuse: How to stop online harassment

Top 6 bug bounty programs for cybersecurity professionals

How will zero trust change the incident response process?

Understanding hackers: The insider threat

Proper CMMC scoping is key to a smooth CMMC assessment

Cybersecurity Weekly: Most popular phishing trends, Microsoft emergency update and a REvil ransomware sting

ISO 27001 auditing: 6 things to know about auditing training and careers

Malware instrumentation with Frida

Tunneling and port forwarding tools used during red teaming assessments

CORROSION: 1 Vulnhub CTF walkthrough, part 1

Your next security bug won't even be in the software that you wrote

This combat medic turned cyber pro says “diversity is required”

Can your personality indicate how you’ll react to a cyberthreat?

Security in Action Framework: Determine if an MSSP is a good fit for you

Paraben CEO shares the importance of creative thinking in digital forensics
EVILBOX: ONE VulnHub CTF Walkthrough

ISC2 CGRC domain #7: Continuous monitoring

ISC2 CGRC domain #6: Authorization and approval of information system

Understanding hackers: The 5 primary types of external attackers

ISC2 CGRC domain #5: Assessment and audit of security and privacy controls

Cybersecurity Weekly: Mitigating ransomware risks, new iOS privacy report and privacy predictions for 2022
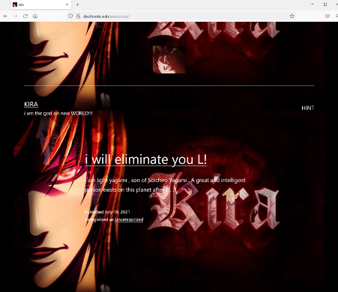
DEATHNOTE: 1 VulnHub CTF walkthrough