Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Breaking down barriers: How to make cybersecurity more inclusive and diverse

Twitter private tweets bug and Cisco phone router vulnerabilities

Cisco XSS zero-day flaw and PaperCut vulnerabilities

Breaking the Silo: Integrating Email Security with XDR

DevSecOps: Continuous Integration Continuous Delivery (CI-CD) tools

3CX hackers hit critical infrastructure and secondhand routers cause security concerns

What is Security Service Edge (SSE)?

Computer forensics interview questions

Hyundai data breach and Microsoft’s warning to accountants

The digital security forensic analyst salary guide

Western Digital cloud breach and the MSI ransomware hack

TMX loan data breach, Italy bans ChatGPT and WordPress Elementor Pro exploit

Applying linguistics to cybersecurity: The journey of Jade Brown, a 2022 Infosec Scholarship winner

Average SCADA Security (CSSA) salary

The top 12 information security risk analyst questions you need to know

ChatGPT data leak and Gmail message theft by North Korean hackers
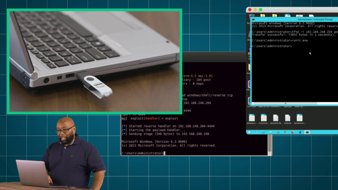
Connecting a malicious thumb drive: An undetectable cyberattack

Threat hunter

The Path to “Career 4.0”: Amy Bonus leverages humanities, FinTech experience to bring Cybersecurity to the layperson

U.S. federal agency hack and the return of FakeCalls Android malware

Secure cloud computing: What you need to know

Security engineer: Degree vs. certification

Massive AT&T data breach and fake jobs targeting security researchers

How to configure a network firewall: Walkthrough