Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Security+ Study Guide: Domain 1.0 - Network Security
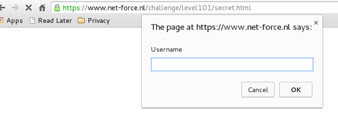
The Pitfalls of Client-Side Authentication: Solutions to Net-Force JavaScript CTF challenges

Interview: Cortney Thompson, Chief Technology Officer at Green House Data

Bypassing Jailbreak Detection Using Xcon

The seven steps of a successful cyber attack

Sharkfest 2014 Part II

Build A Simple Cloud Using the Open Hardware Technology

Reverse Engineering of Embedded Devices

Cyber Threat Assessment Template For Special Forces
Insider vs. outsider threats: Identify and prevent

Interview: Chris Steel, Chief Solutions Architect at Software AG Government Solutions, Inc.
Asprox / Kuluoz Botnet Analysis

APT28: Cybercrime or State-sponsored Hacking?

Case Study: Evading Automated Sandbox - Python PoC

Windows Functions in Malware Analysis - Cheat Sheet - Part 2

ELF File Format
Dealing with bad characters & JMP instruction

15 + Modules for Making Your Drupal Website Secure

How to Prevent a Domain Name Theft

Interview: J. Wolfgang Goerlich, Cyber Security Strategist for Creative Breakthrough

iOS Application Security Part 42 - LLDB Usage continued

Windows functions in malware analysis - cheat sheet - Part 1
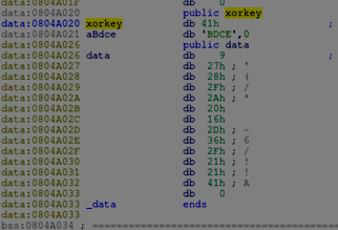
Introducing IDA scripting
The Basics with Node.js Examples