Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Hospital Security

Security Awareness for Healthcare Facilities

Hospital security policies & procedures

What Does Security Awareness Mean for Doctors, Nurses and Hospital Staff?

Security Awareness for Healthcare Professionals

The Heart of It All – The Biometric Sensor

Reversing Binary: Spotting Bug without Source Code

Application Logs & Developer Backdoors

DLL Hijacking using Damn Vulnerable Thick Client App

An Introduction to Biometric Key Performance Indicators and Standards

Reversing & Patching .NET Applications using Damn Vulnerable Thick Client App

Reversing & Decrypting Database Credentials using Damn Vulnerable Thick Client App

The Most Controversial Biometric of All – Facial Recognition

ActiveX Security Model

Perfect SAP Penetration Testing: Threat Modeling

Network discovery tools

Solving the VulnOS 2 Lab

Linux Malware: Novelties in the Threat Landscape

Vein Pattern Recognition
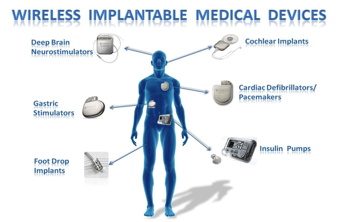
Hackable Medical Devices

Other Healthcare IT Regulations

Injection Attacks Using DAMN Vulnerable Thick Client App

HITECH Act and IT Security

HIPAA Security Checklist